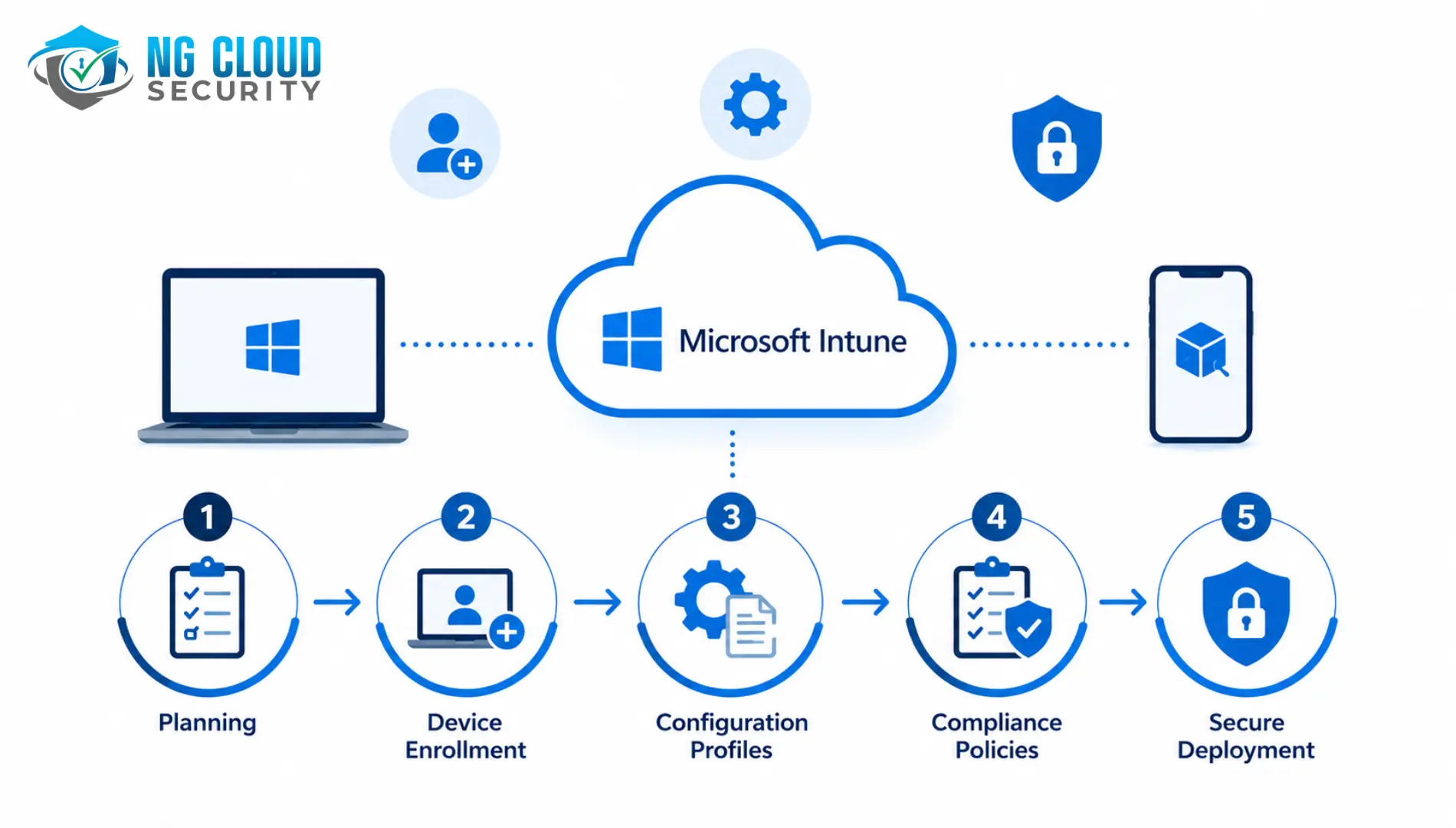
Microsoft Intune deployment has grown from a mobile device management add-on into the cornerstone of enterprise endpoint security strategy. In 2026, it manages more than 200 million devices worldwide and holds a 37% share of the MDM market — yet a significant number of deployments fail to reach their potential because they are rushed, poorly […]
Artificial Intelligence is rapidly transforming how organizations operate. From Microsoft Copilot and AI assistants to autonomous AI agents that interact with business systems, organizations are embracing AI to improve productivity, automate processes, and unlock new business opportunities. However, AI adoption introduces new risks that traditional governance and security models were not designed to address. AI […]
Cyber threats are becoming more sophisticated every year. Businesses now face ransomware attacks, phishing campaigns, insider threats, cloud security risks, and advanced persistent threats that can disrupt operations and lead to significant financial losses. While many organizations understand the importance of security monitoring, building and managing an internal Security Operations Center requires substantial investment in […]
Microsoft Purview is one of the most powerful data compliance and governance platforms available for Microsoft 365 environments — yet a significant number of enterprise deployments fail to deliver their intended outcomes. Dashboards fill up with alerts that no one acts on. DLP policies stay in simulation mode for months. Sensitive data continues to leave […]
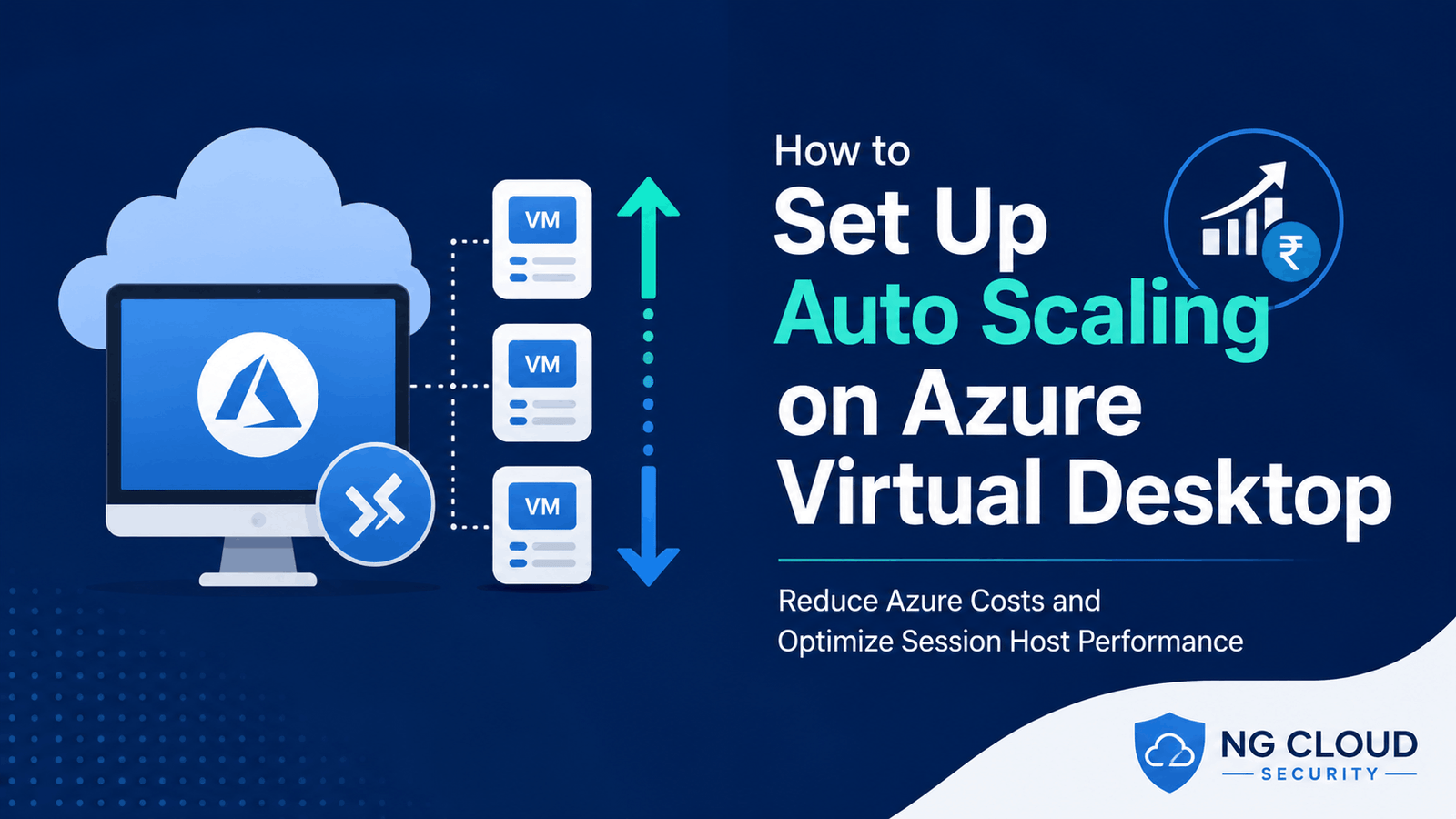
How to Set Up Auto Scaling on Azure Virtual Desktop Azure Virtual Desktop has become one of the most popular solutions for delivering secure remote desktops and applications to users anywhere in the world. Organizations adopt Azure Virtual Desktop because it offers flexibility, scalability, centralized management, and enhanced security while reducing the need for traditional […]
Microsoft 365 consulting companies in India are transforming how businesses collaborate, automate, and secure their digital workspaces. Finding the right partner can make all the difference — and India is home to some of the world’s best Microsoft 365 and Office 365 consulting firms, ranging from global IT giants to specialised cloud security experts. Here […]
Businesses today depend heavily on cloud platforms, SaaS applications, remote teams, and third party service providers. While this digital transformation improves efficiency and scalability, it also increases cybersecurity and compliance risks. Organizations now need stronger visibility into how vendors manage sensitive customer data, security controls, and operational processes. This is where SOC reports become important. […]
Small businesses are increasingly becoming targets for cyberattacks because they often lack dedicated security teams and advanced protection tools. A single infected laptop or employee device can expose customer records, financial information, and cloud applications. This is where endpoint security software becomes essential. Endpoint security software helps protect all devices connected to your business network, […]
Microsoft has officially announced major changes to Microsoft 365 commercial plans that will take effect from July 1, 2026. Along with updated pricing, Microsoft is adding new AI, security, and endpoint management capabilities across several Microsoft 365 and Office 365 plans. For businesses using Microsoft 365 for collaboration, productivity, and security, this update is important […]
The effects of hacking are no longer limited to large enterprises. Today, small startups, growing companies, and global organizations all face cyber risks that can impact revenue, operations, and trust. In my experience, many business owners only think about cyberattacks after an incident has already disrupted their business. By then, the cost is often much […]