How to Trace Email Sender Location for Cybersecurity Investigations
Email remains one of the most common entry points for cyber attacks. From phishing campaigns to business email compromise, attackers often hide behind fake identities. In many investigations, one key question comes up early which is how to trace email sender location.
From my experience working on real security incidents, tracing an email is not about finding an exact address. It is about collecting technical evidence, analyzing patterns, and building a reliable picture of the sender’s origin. If you already have strong email security controls in place, tracing becomes faster and more accurate.
Why Email Tracing Matters in Cybersecurity
Understanding how to trace email sender location helps organizations respond faster to threats. Security teams use this process to identify phishing campaigns, investigate suspicious emails, and improve their detection capabilities.
It also plays a key role in advanced monitoring environments such as managed SOC services, where continuous analysis of email threats is required. Without proper tracing, it becomes difficult to understand attacker behavior and improve defenses.
Step One: Analyze Email Headers
The most important step in how to trace email sender location is analyzing the email header. Every email contains hidden metadata that shows how it traveled across servers.
You should look for fields such as:
- Received entries
- IP addresses
- Mail server information
- Time stamps
The earliest Received entry usually indicates the origin point. Most email platforms allow you to view headers easily.
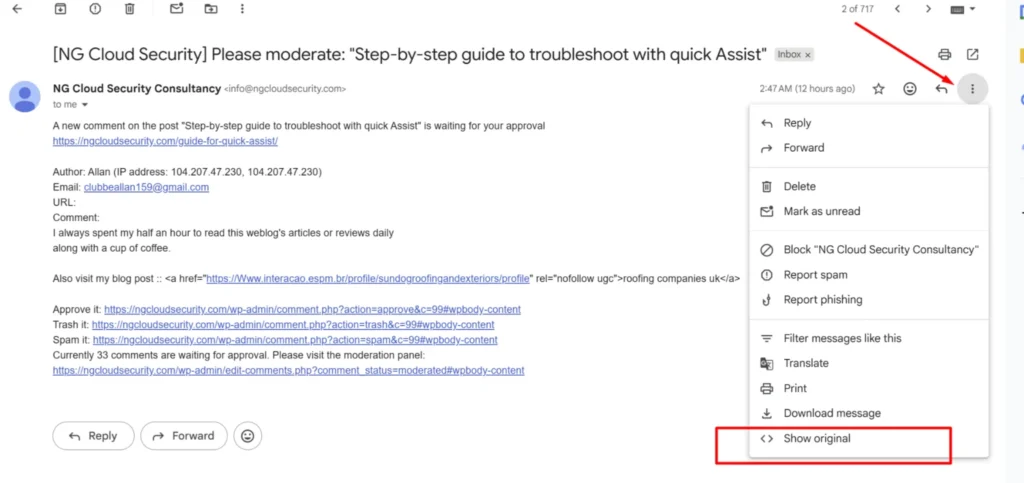
In many cases, especially in basic phishing attempts, header analysis alone can reveal useful clues.
Step Two: Identify the Originating IP Address
After extracting the header, the next step is to identify the actual sending IP.
Focus on the earliest server entry. This is often the closest point to the sender. However, attackers may try to manipulate headers, so validation is critical.
If the IP does not match the claimed domain, it is a strong indicator of spoofing. This is where combining header analysis with digital certificate validation can provide better clarity.
Step Three: Perform IP Geolocation Lookup
Once you have the IP address, use IP lookup tools to estimate the location. This step is central to how to trace email sender location.
These tools provide:
- Geographic region
- Internet service provider
- Organization details
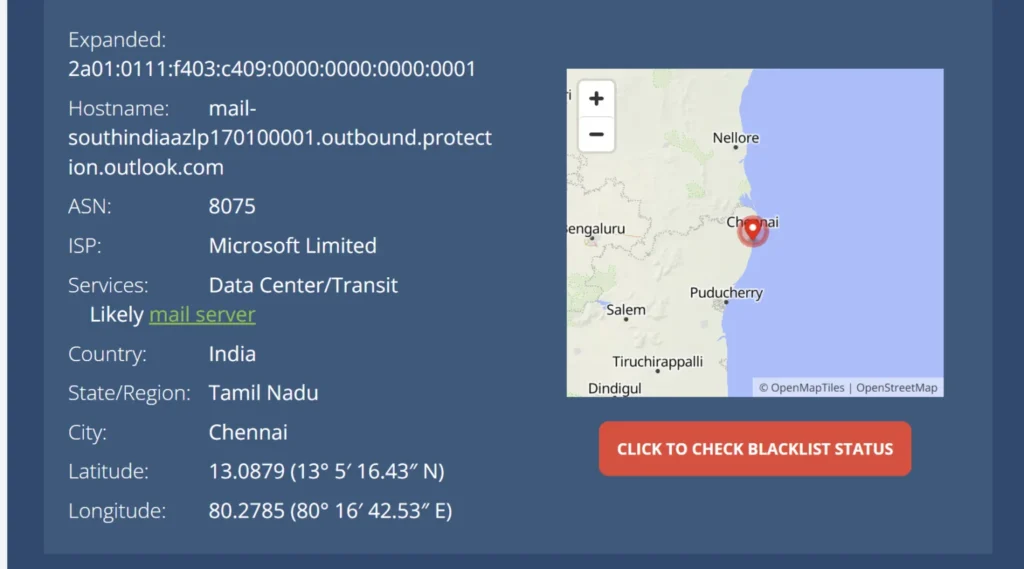
While this gives a general idea, it is not always precise. Attackers often use cloud infrastructure or anonymization techniques, which can mask their real location.
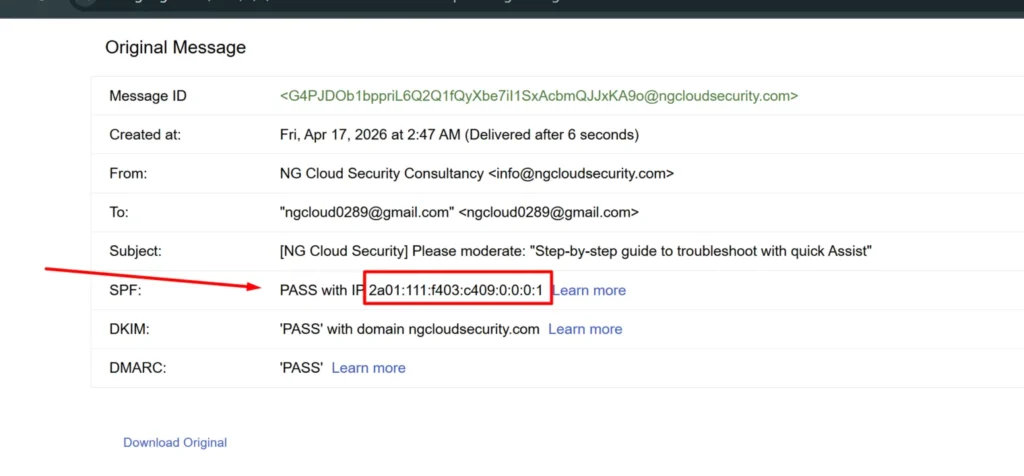
Step Four: Check Email Authentication Records
To strengthen your findings, always verify authentication mechanisms such as SPF, DKIM, and DMARC.
If you want a deeper understanding of how these work in real environments, you can explore DMARC policies and enforcement strategies.
When authentication fails, it usually indicates that the email was spoofed. This is very common in targeted phishing attacks.
Step Five: Correlate with Threat Intelligence
Tracing an email should never rely on a single data point. Correlation is essential.
Security teams check IP addresses against threat intelligence feeds, blacklists, and known malicious infrastructure. In advanced setups like extended detection and response platforms, this process is automated.
This step helps confirm whether the sender is part of a known attack campaign.
Step Six: Analyze Email Content and Links
Beyond technical tracing, content analysis plays a major role.
Look for:
- Suspicious links
- Fake domains
- Urgent or manipulative language
Many phishing emails rely on social engineering rather than technical sophistication. If needed, organizations can further strengthen defenses through endpoint security assessment to detect malicious payloads delivered via email.
Limitations of Email Tracing
It is important to understand the limitations of how to trace email sender location.
Some common challenges include:
- Use of VPN or proxy networks
- Compromised systems acting as relay points
- Cloud based infrastructure masking origin
- Manipulated email headers
Because of these factors, tracing does not always lead directly to the attacker. Instead, it provides investigative leads.
Best Practices for Accurate Email Investigations
To improve accuracy and reliability, follow a structured approach:
- Always analyze complete email headers
- Validate IP data using multiple sources
- Combine tracing with behavioral analysis
- Document findings for future reference
- Align investigation with Zero Trust security principles
From my experience, a layered investigation approach delivers the best results.
How to Strengthen Email Security Proactively
Tracing emails is reactive. A better strategy is prevention.
Organizations should:
- Deploy advanced email filtering solutions
- Enforce strong authentication protocols
- Monitor threats continuously using security operations services
- Train employees to identify phishing attempts
- Implement modern cloud security frameworks
A strong security posture reduces both the frequency and impact of email based attacks.
Final Thoughts
Learning how to trace email sender location is a critical skill in cybersecurity investigations. While it may not always reveal the exact identity of the attacker, it provides valuable insights that help security teams respond effectively.
By combining header analysis, IP tracking, authentication checks, and threat intelligence, organizations can build a complete picture of an attack. In today’s evolving threat landscape, this capability is essential for any modern security strategy.