Blog
Explore cybersecurity insights, cloud security strategies, Microsoft 365 guidance, and expert tips to protect modern businesses from evolving cyber threats.
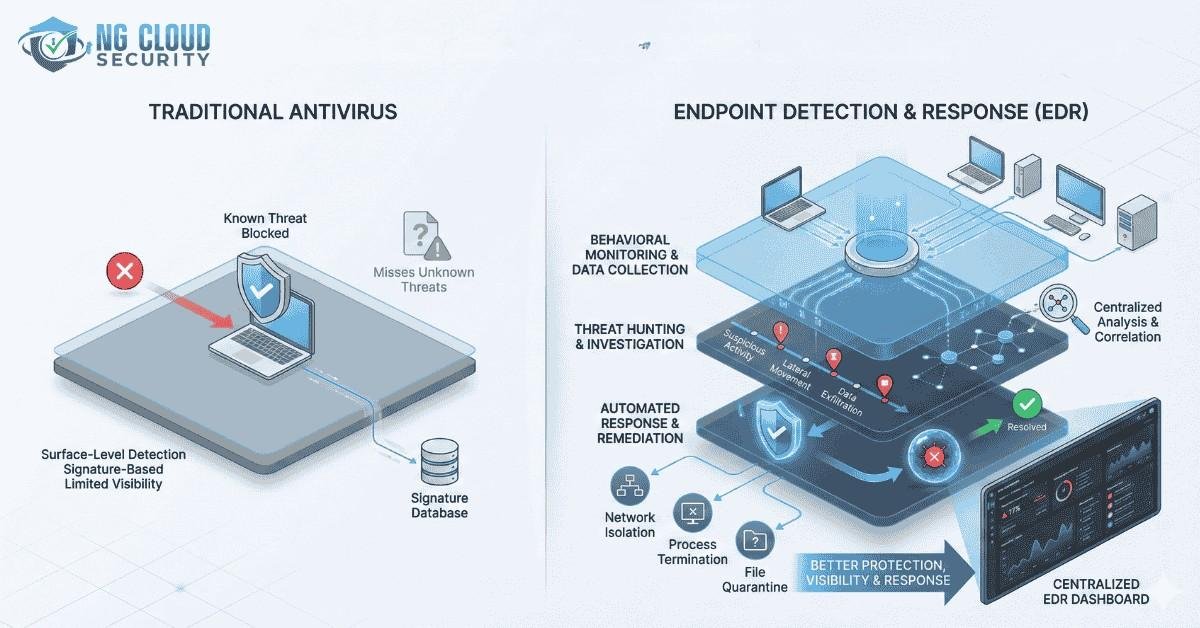
The main difference between EDR and antivirus is one of the most common questions I hear from business owners and IT leaders very frequenlty. Many organizations still depend on traditional antivirus because it feels familiar and safe. Yet the threat landscape has changed faster than most security tools. Attackers no longer behave like the viruses […]
Endpoint security has become a critical part of modern cybersecurity strategy. In my experience working with cloud first and hybrid environments, I have seen how a single endpoint security controller problem can quietly weaken an organization’s defenses. When endpoint visibility breaks, threats often go unnoticed until real damage is done. If you are already investing […]
One of the most common questions I hear from business leaders and IT teams is does Microsoft 365 have a PDF editor. It sounds like a basic requirement, yet it often creates confusion once teams start working with contracts, policies, invoices, and compliance documents inside Microsoft 365. Having worked with Microsoft 365 across different industries, […]
When enterprise leaders ask me how long does cloud migration take, I usually pause before answering. Not because the question is unclear, but because the timeline depends on many moving parts. In real enterprise environments, cloud migration is not a single project. It is a transformation that touches applications, infrastructure, security, compliance, and people. From […]
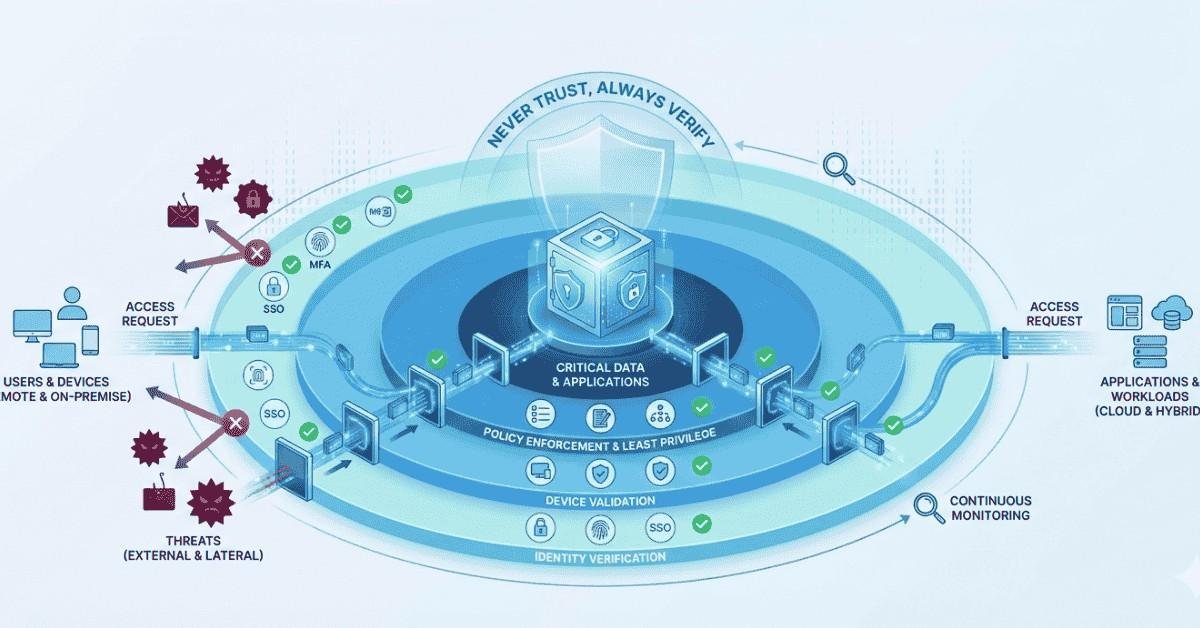
Overview Securing Remote Access is essential when allowing remote users on personal devices to access Azure Virtual Desktop (AVD) and Windows 365 (W365) while restricting access to other cloud applications and organizational data. In this article, we discuss how organizations can safely enable BYOD access without exposing sensitive resources. Securing Azure Virtual Desktop (AVD) plays […]
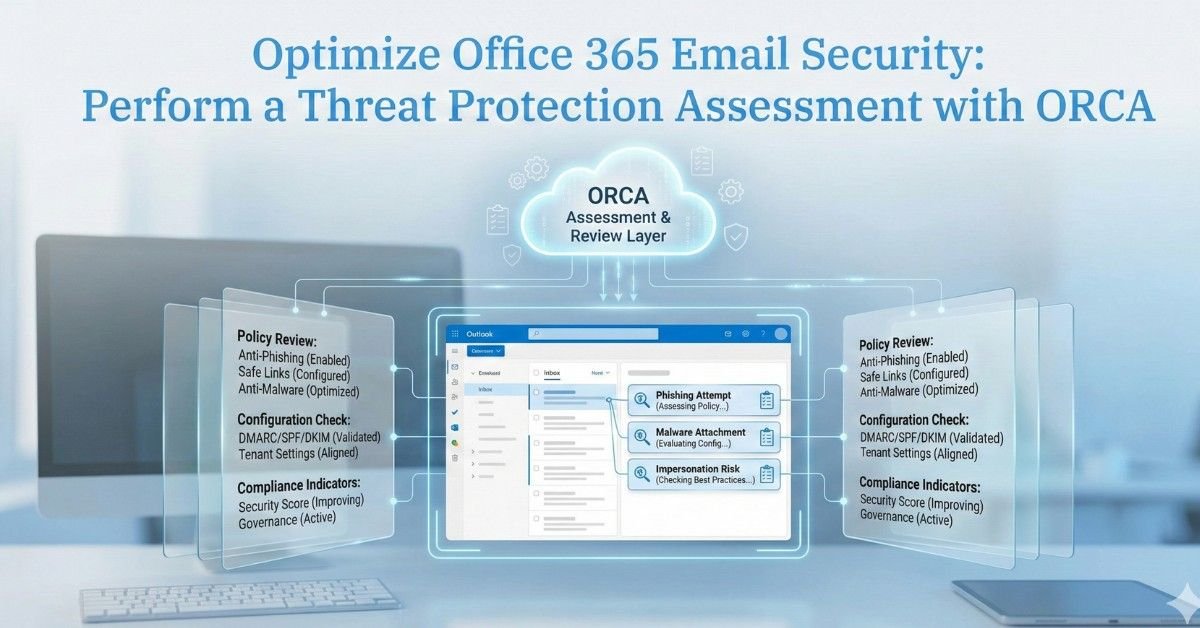
Comprehensive Office 365 Email Security is essential for protecting modern business communications, as email remains the primary collaboration channel for most organizations. However, it is also one of the most targeted entry points for cyber threats such as phishing, malware, and business email compromise (BEC). Microsoft Office 365 provides powerful built-in security capabilities, but these […]
Optimize Office 365 Email Security by regularly reviewing Microsoft Defender for Office 365 Advanced Threat Protection (ATP) configurations to defend against phishing, malware, and business email compromise attacks. Microsoft’s Office 365 ATP Recommended Configuration Analyzer (ORCA) helps organizations evaluate existing security settings and identify gaps based on Microsoft security best practices. This article explains how […]
Concerned about managing your Microsoft 365 and Azure Cloud environment? Leave it to us. NG Cloud Security, a trusted Microsoft Security Solution Partner, delivers comprehensive managed service support designed to keep your IT operations secure, optimized, and continuously available. Our 24×7 dedicated support team ensures seamless management of Microsoft 365, Azure Cloud, and identity infrastructure […]
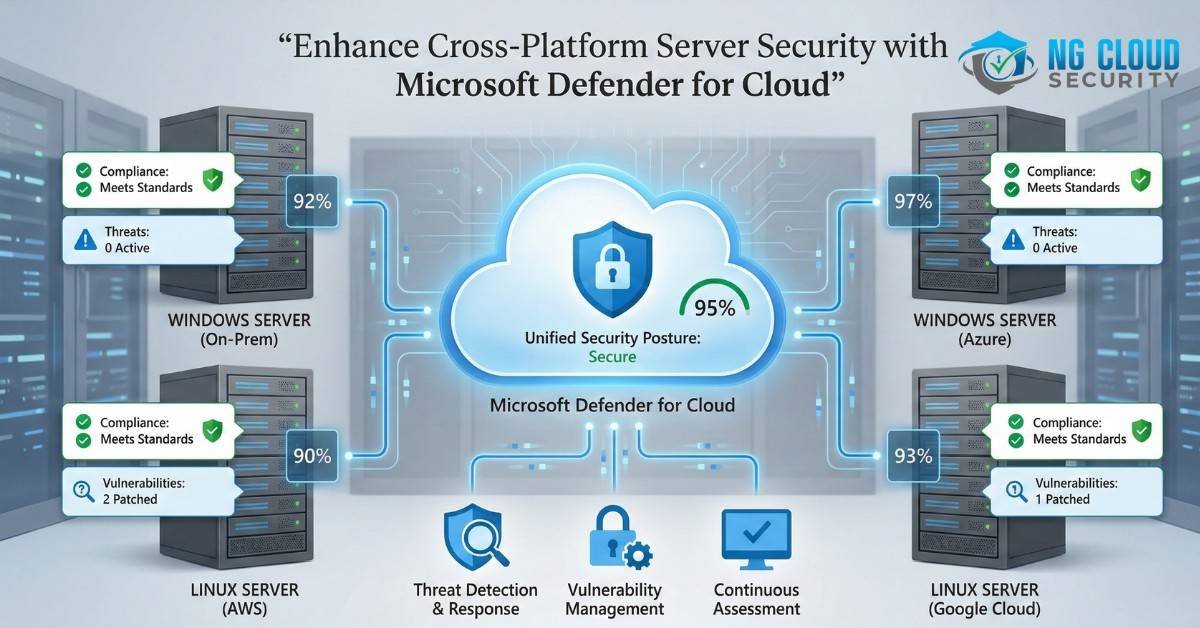
In today’s multi-cloud, hybrid IT environments, maintaining real-time security and operational efficiency across diverse servers can be challenging. Organizations need robust solutions that offer comprehensive protection with minimal disruption and downtime. Microsoft Defender for Cloud is the answer, providing an integrated security management platform that seamlessly unifies security operations across various infrastructures. Why Choose Microsoft […]
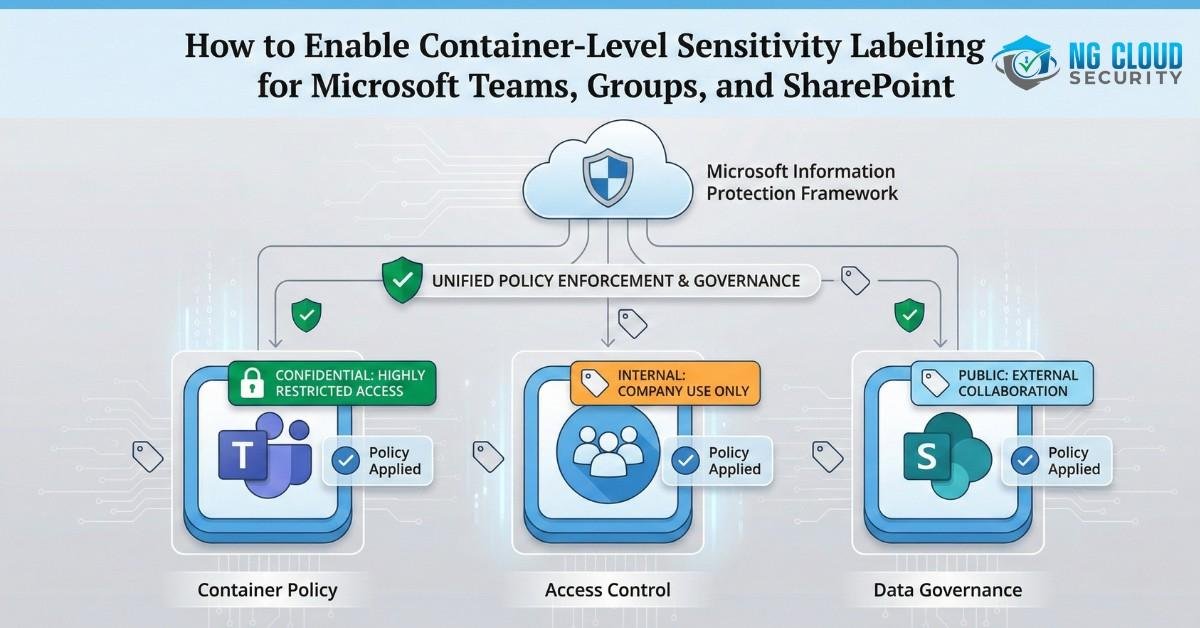
Microsoft Teams, Groups, and SharePoint play a critical role in modern collaboration within Microsoft 365 environments, making data protection and classification essential for organizations. In this article, we will discuss how to enable Microsoft Information Protection (MIP) sensitivity labeling for Microsoft 365 Groups, Teams, and SharePoint Online sites. Since this configuration is disabled by default […]