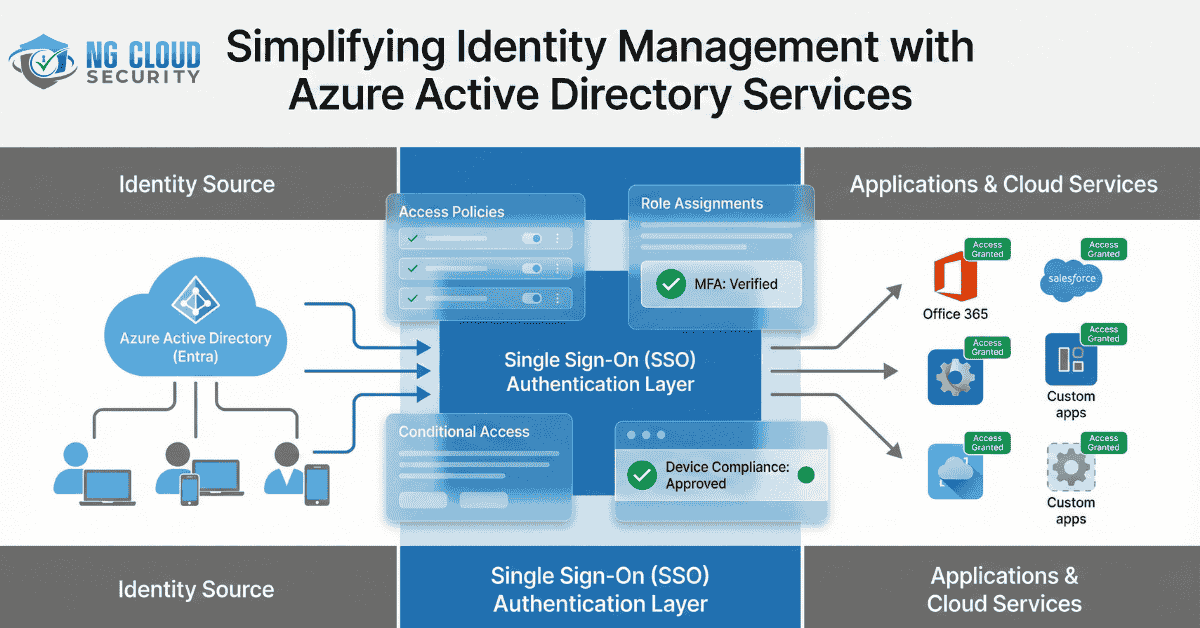
In today’s cloud-driven business environment, secure identity and access management have become essential. As organizations embrace hybrid and multi-cloud infrastructures, the need for centralized identity control, enhanced user authentication, and secure access to corporate resources has grown significantly. Azure Active Directory Services (Azure AD) has emerged as a leading solution for these challenges, offering a […]
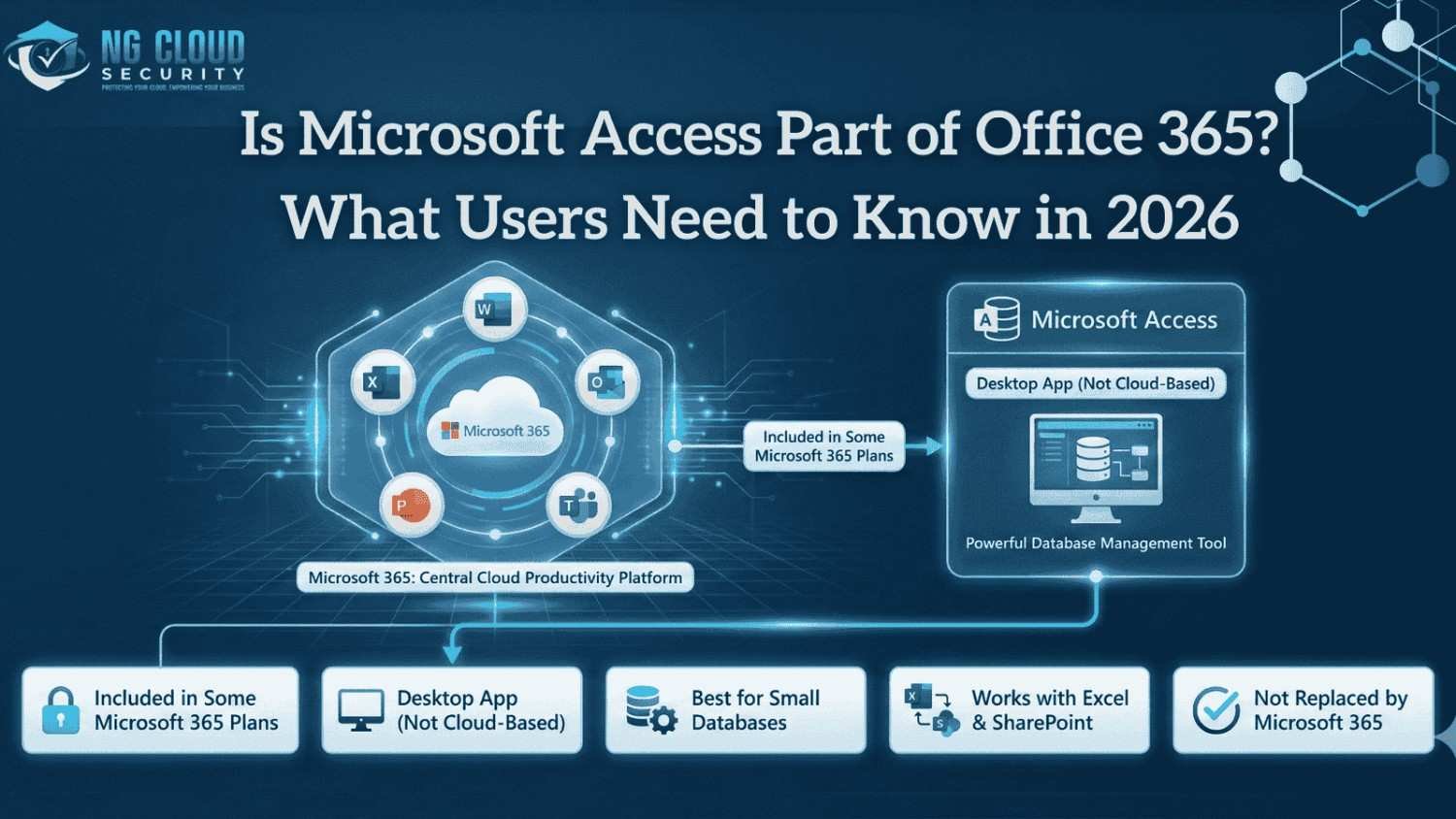
In my experience working with organizations adopting Microsoft 365, one question keeps coming up again and again. Is Microsoft Access part of Office 365, and does it still make sense to rely on it in a cloud first environment? The confusion is understandable. Microsoft 365 has evolved rapidly, focusing more on cloud services, browser based […]
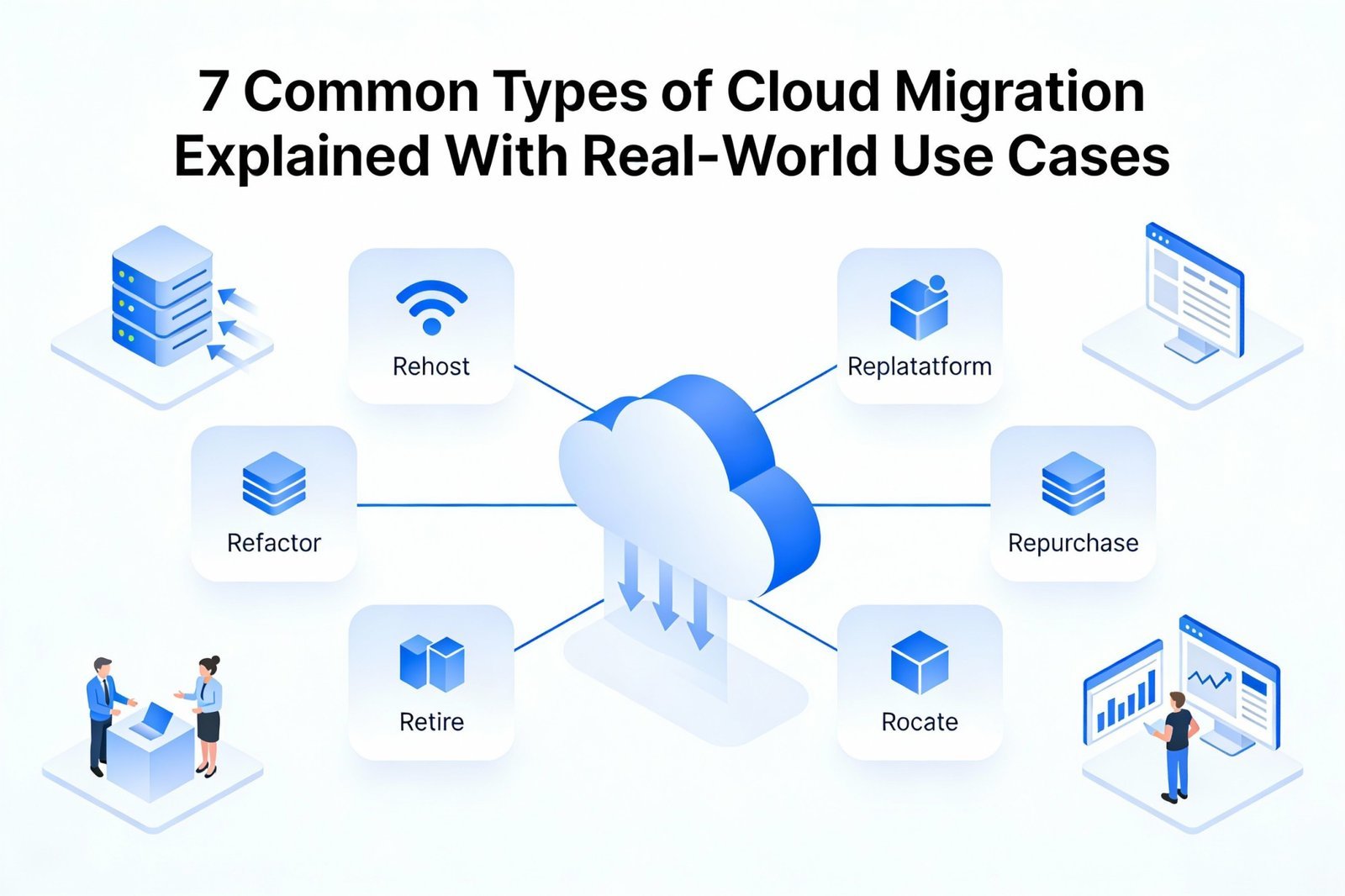
When business leaders ask me how long does cloud migration take, my honest answer is always it depends. In enterprise environments, cloud migration is not a single task. It is a structured transformation that impacts infrastructure, applications, security, and operations. In my experience, organizations that first understand the different types of cloud migration approaches move faster and avoid […]
When people talk about cybersecurity, Mac devices are often assumed to be safer by default. In my experience, that assumption creates more risk than protection. Mac endpoints are now widely used in enterprises, remote teams, and leadership roles, making them a prime target for modern attacks. This is where understanding what is endpoint security for Mac becomes […]
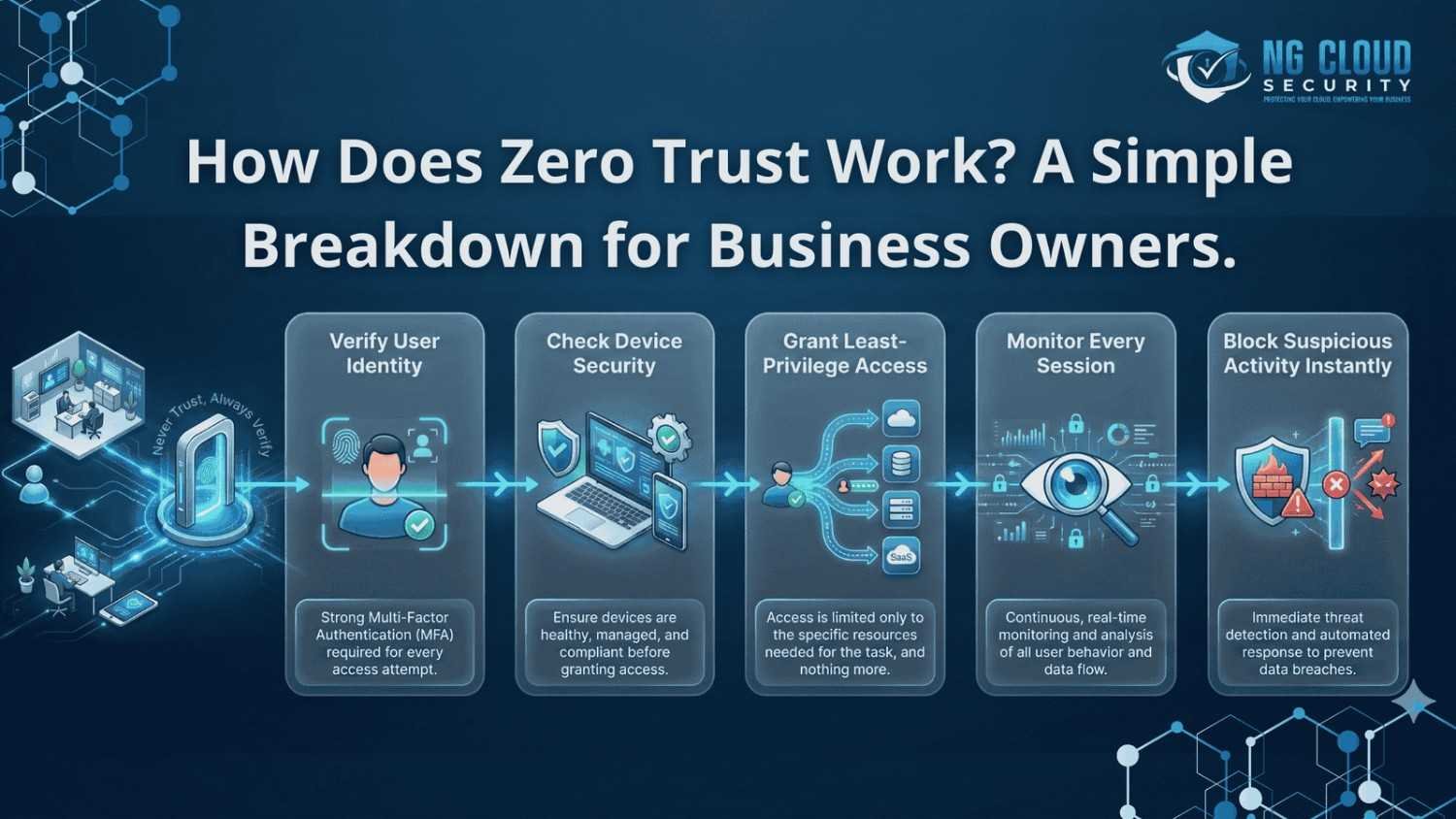
One of the most common questions I hear from business owners today is simple but important. How does zero trust work and why is it becoming the foundation of modern cybersecurity. From my experience working with organizations moving to cloud and hybrid environments, traditional security models no longer match how businesses actually operate. Users work […]
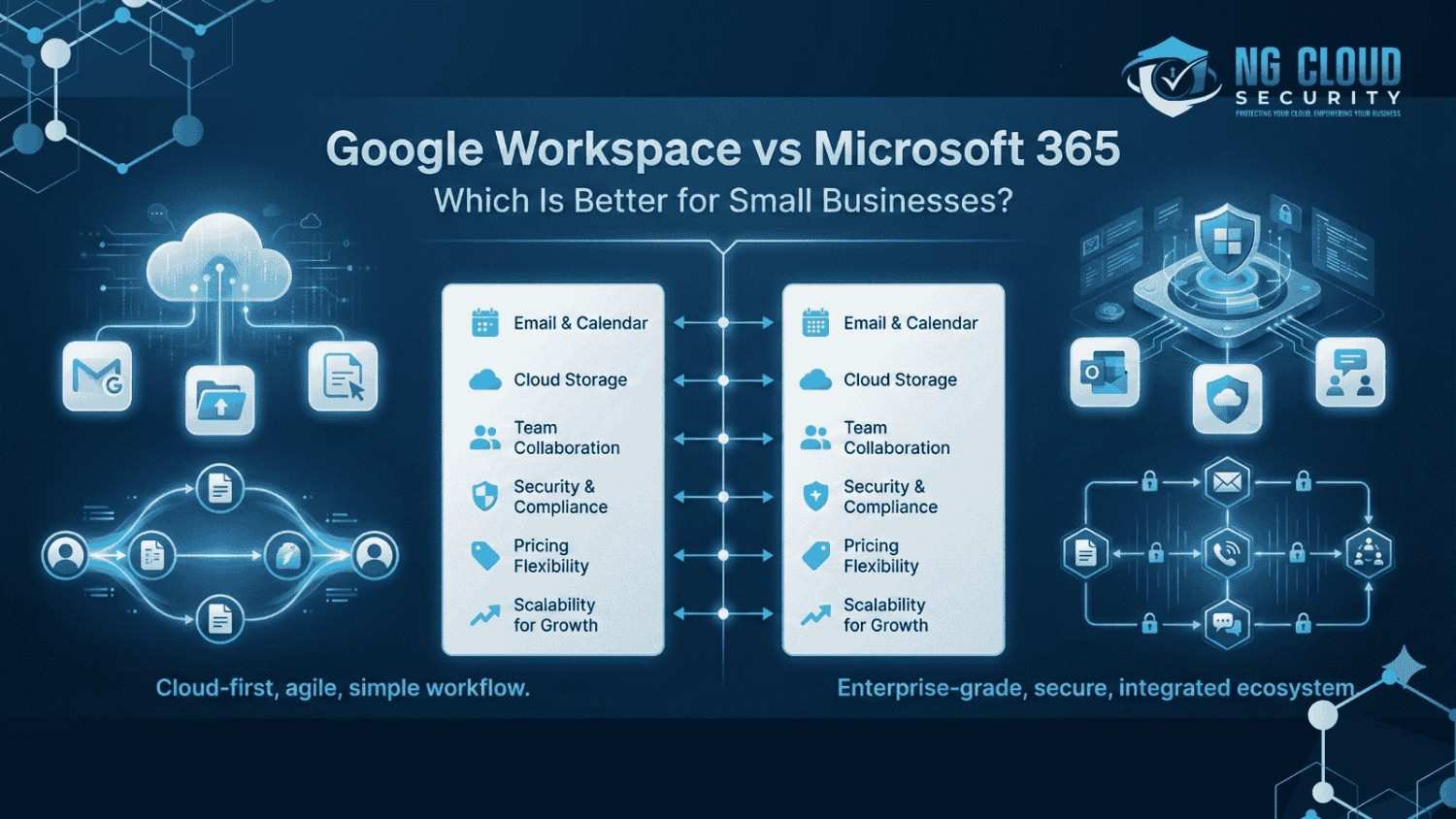
When small business owners ask me to compare productivity platforms, the discussion usually comes down to google workspace vs microsoft 365 for small business. I have seen both platforms used across different industries, and the right choice often depends on how a business works today and how it plans to grow. Productivity tools are no […]
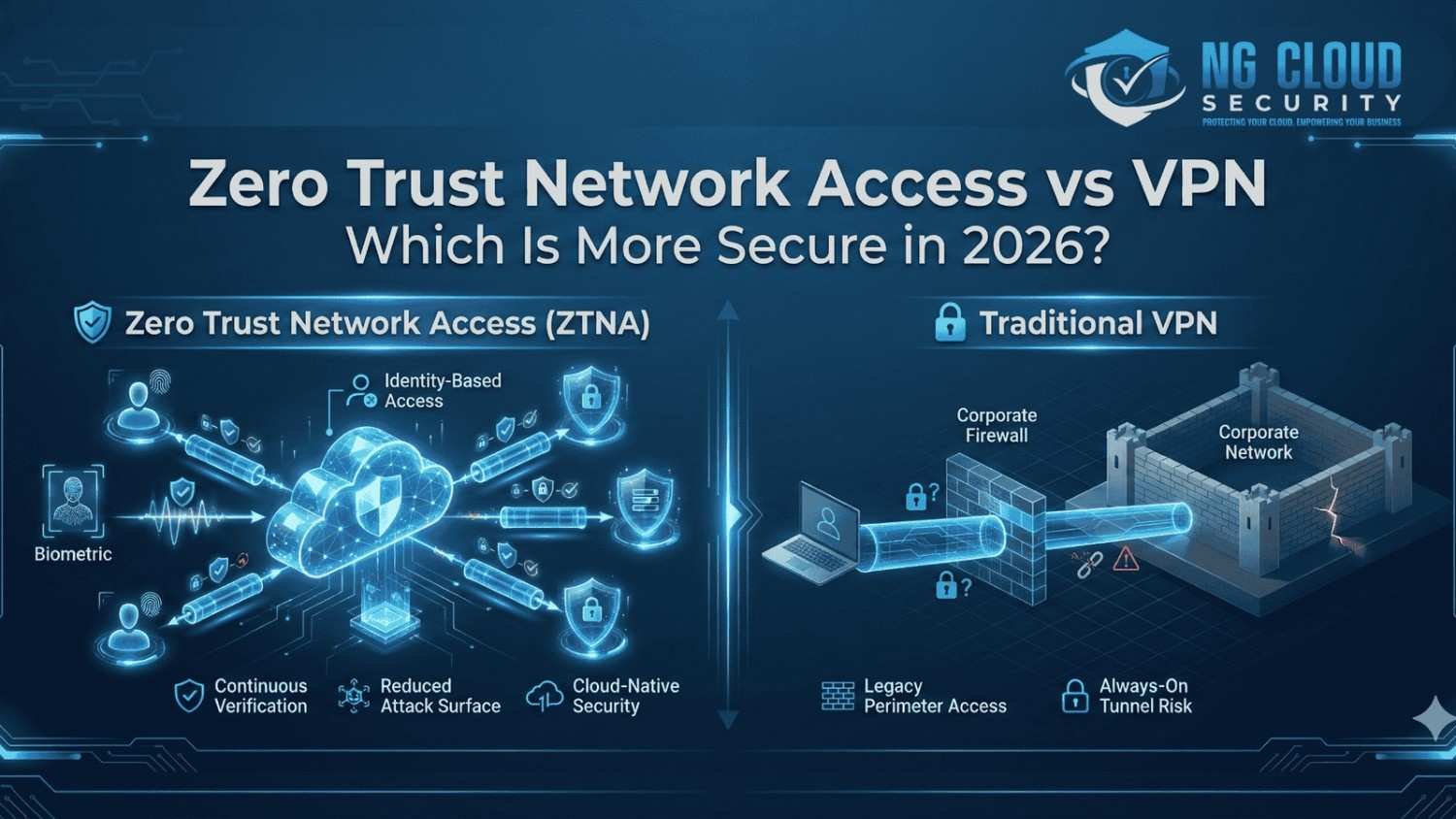
Over the last few years, I have seen a major shift in how organizations think about remote access security. As cloud adoption grows and workforces become more distributed, the conversation around zero trust network access vs vpn has become more important than ever. In 2026, security teams are no longer asking which solution is easier […]
Modern businesses are expected to move fast, stay secure, and support flexible work environments. In my experience, many organizations struggle not because of people or processes, but because their digital tools do not work together. This is where Microsoft 365 creates real impact. When used correctly, the benefits of Microsoft 365 go far beyond email […]
Introduction to Types of Cloud Migration In my experience working with growing businesses and large enterprises, cloud migration almost always starts with confusion. Everyone knows they need the cloud, but very few are clear about the different types of cloud migration and how each one impacts security, cost, and long term scalability. Cloud migration is […]
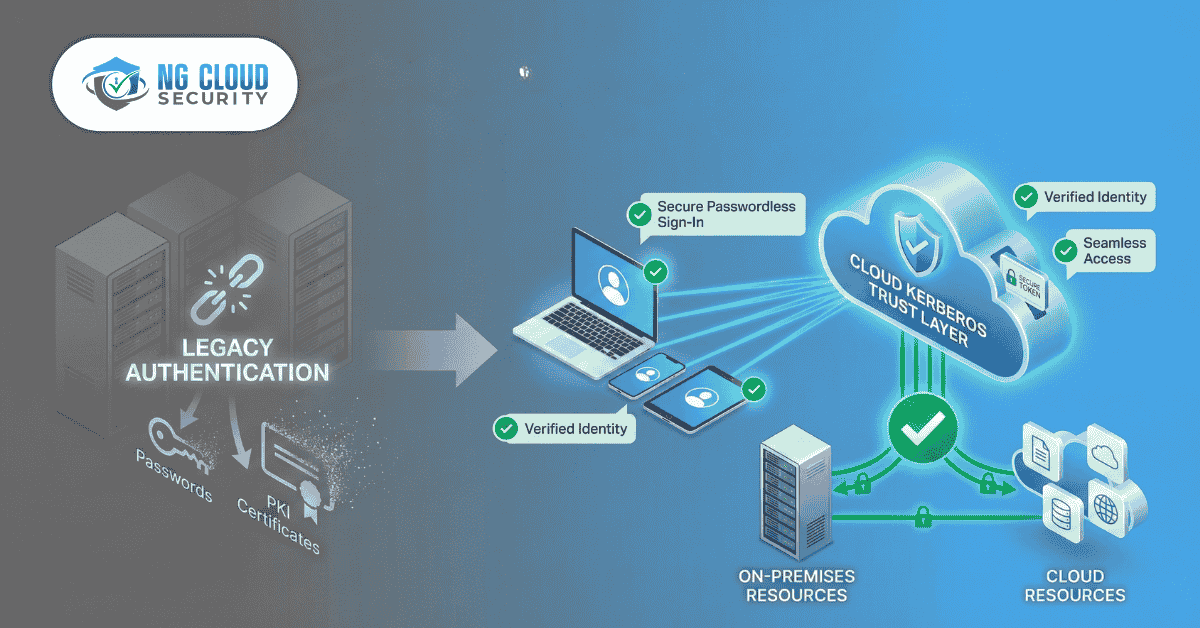
Ditch the PKI and simplify hybrid passwordless authentication with Windows Hello for Business using Cloud Kerberos Trust. Windows Hello for Business (WHfB) is a modern authentication solution built into Windows that replaces traditional passwords with secure, phishing-resistant sign-in methods. Instead of passwords, users authenticate using biometric verification such as fingerprint or facial recognition, or a […]