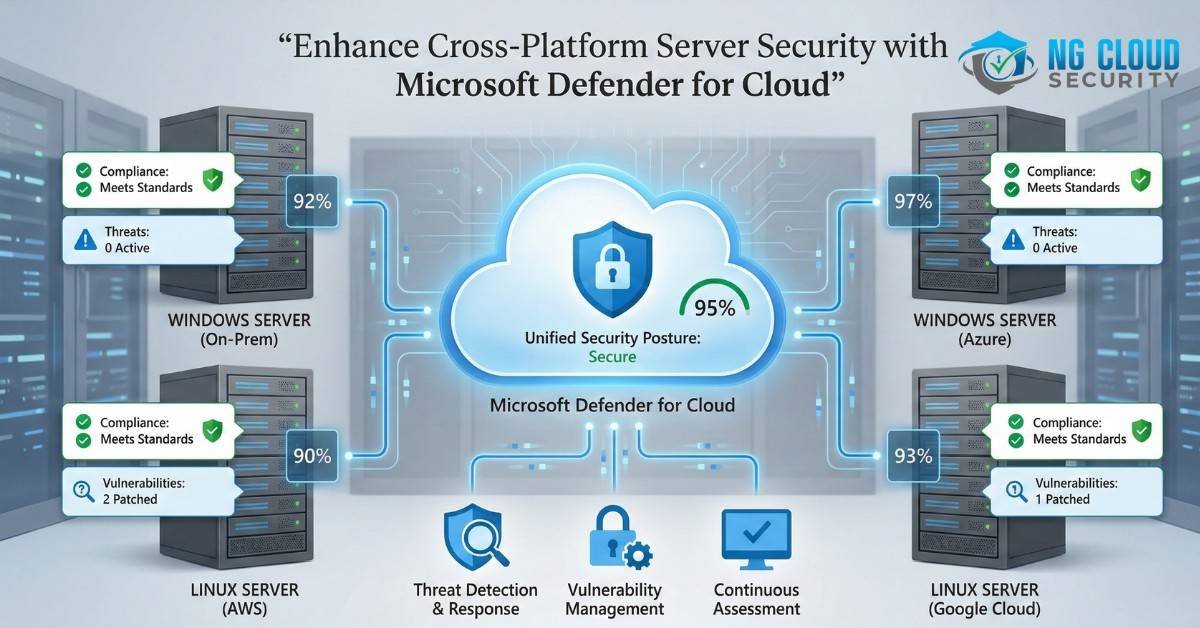
In today’s multi-cloud, hybrid IT environments, maintaining real-time security and operational efficiency across diverse servers can be challenging. Organizations need robust solutions that offer comprehensive protection with minimal disruption and downtime. Microsoft Defender for Cloud is the answer, providing an integrated security management platform that seamlessly unifies security operations across various infrastructures. Why Choose Microsoft […]
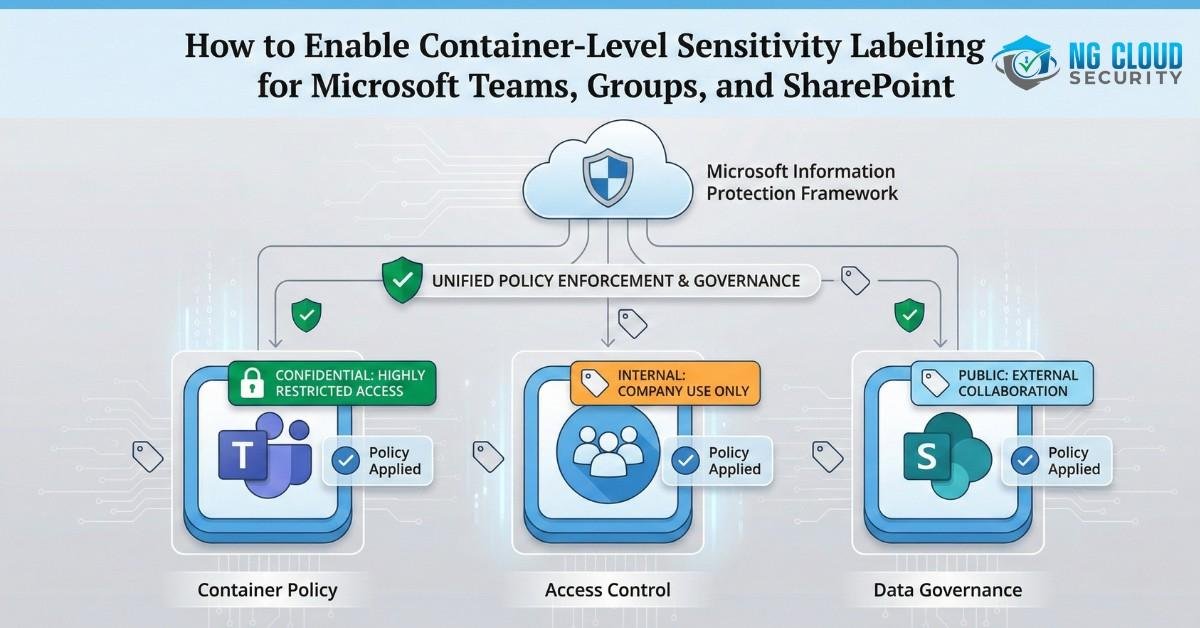
Microsoft Teams, Groups, and SharePoint play a critical role in modern collaboration within Microsoft 365 environments, making data protection and classification essential for organizations. In this article, we will discuss how to enable Microsoft Information Protection (MIP) sensitivity labeling for Microsoft 365 Groups, Teams, and SharePoint Online sites. Since this configuration is disabled by default […]
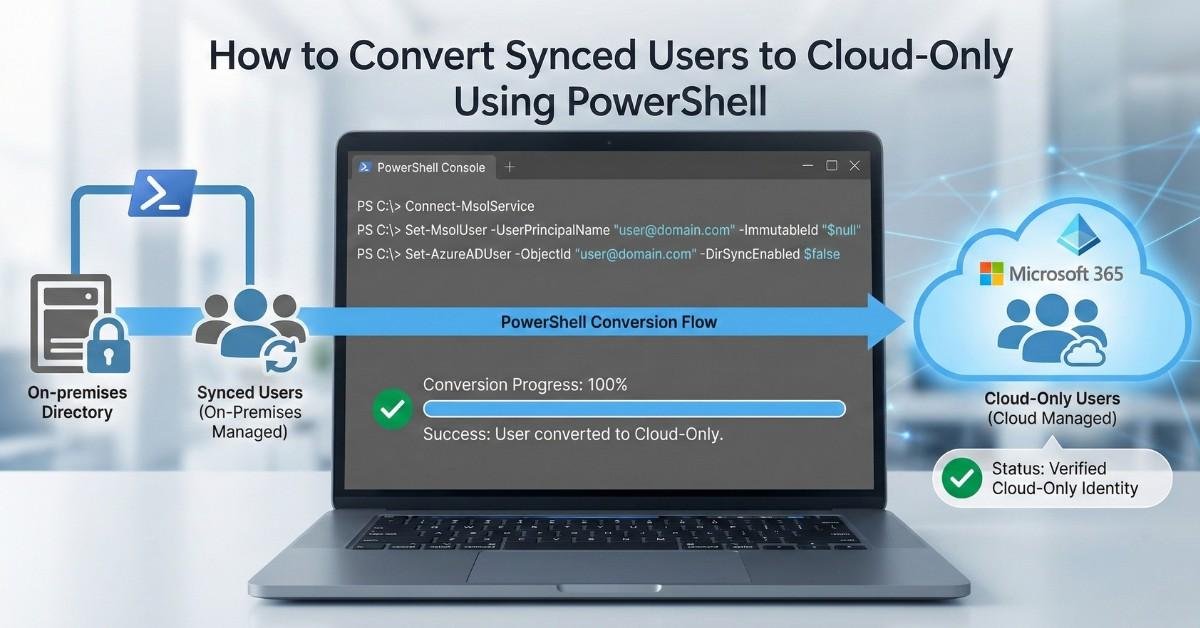
To convert synced user to cloud only using PowerShell, organizations must disable Microsoft Entra ID (Azure AD) directory synchronization. Once synchronization is turned off, Microsoft automatically converts all synced identities into cloud-only users while preserving their existing Microsoft 365 data and permissions. This method is the recommended and supported approach when planning to convert on-prem user to […]
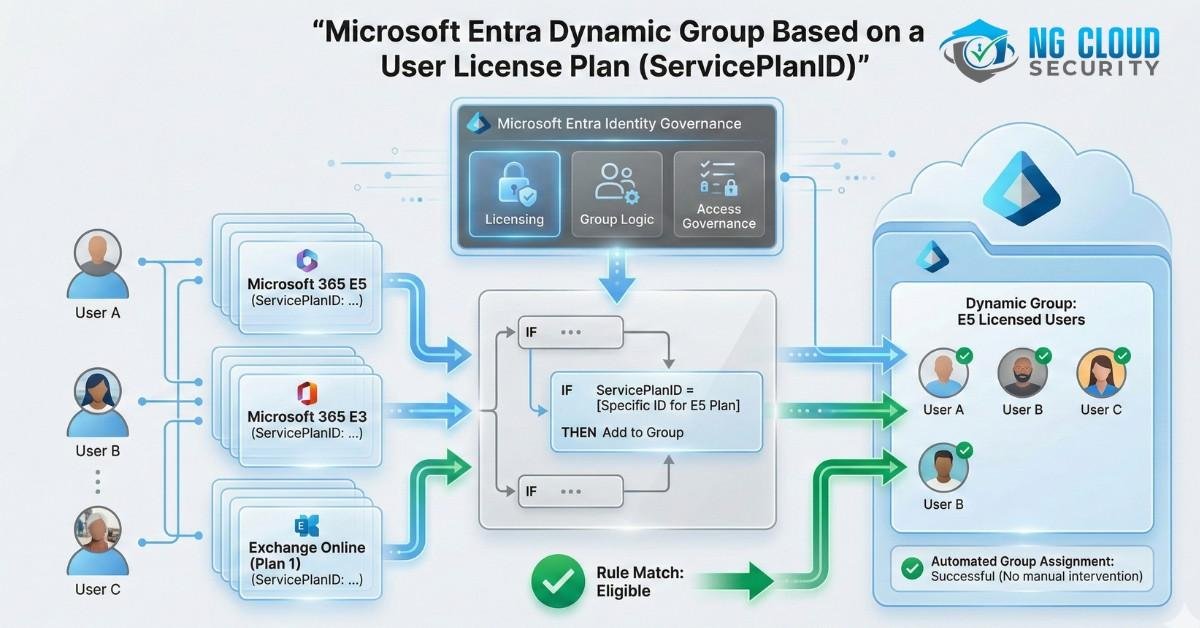
Microsoft Entra offers an excellent feature that allows users to create a Microsoft 365 group based on a set of rules. These rules can dynamically query user attributes to identify specific matching conditions. For instance, one can create a dynamic membership rule that adds users to a particular group based on their “state” property. For example, […]
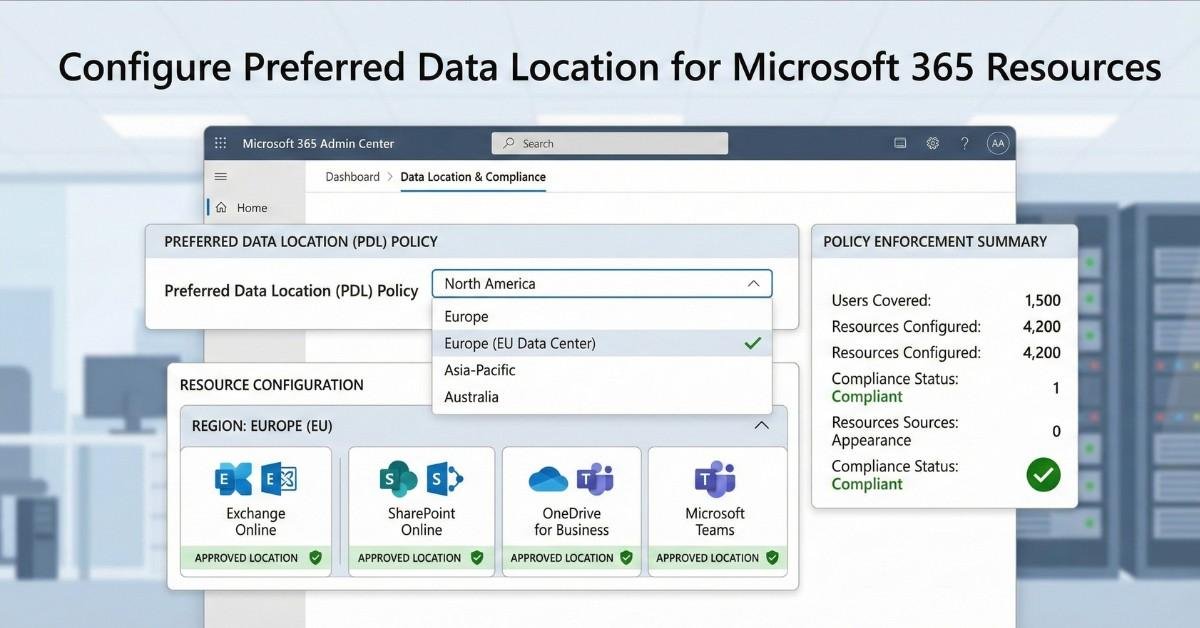
Microsoft 365 Resources can be optimized for global organizations by configuring the preferred data location attribute through Microsoft Entra Connect Sync. In this article, we will guide you through the process of enabling the preferred data location setting, which defines the geographical region where a user’s Microsoft 365 data is stored when Multi-Geo capabilities are […]
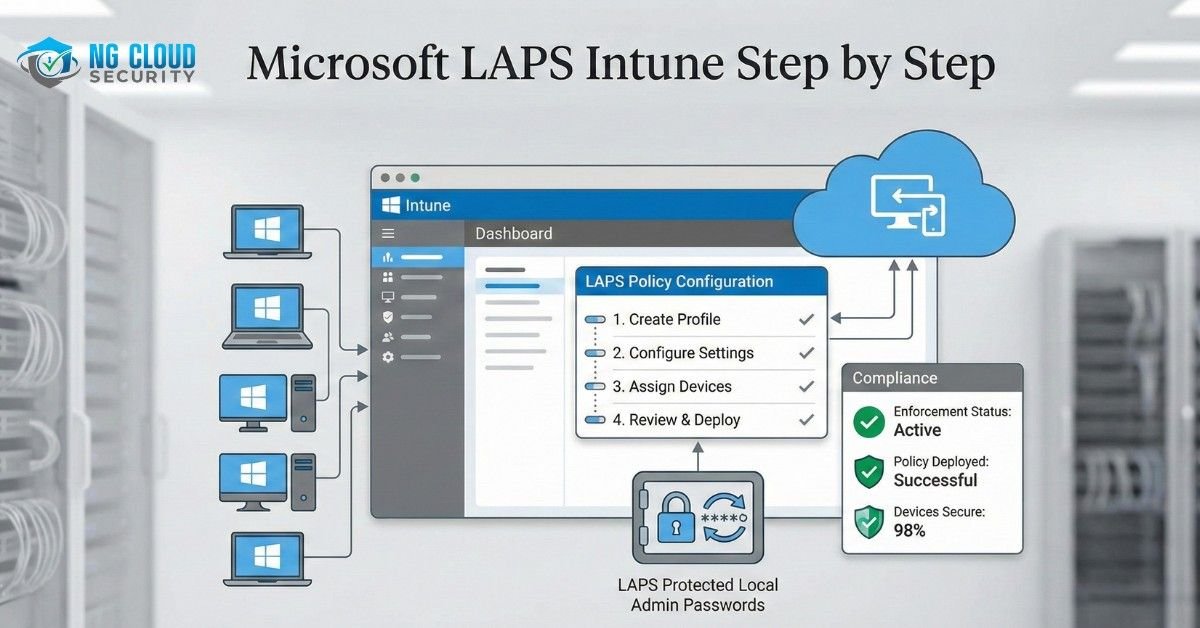
What are Microsoft LAPS? Microsoft LAPS Intune enables organizations to securely manage and automatically rotate local administrator passwords across Windows devices, reducing security risks caused by shared or outdated credentials. While changing a domain administrator password is straightforward, managing local administrator passwords across multiple systems can be challenging. Windows Local Administrator Password Solution (LAPS) addresses […]
Your Microsoft 365 Security Assessment in 5 Steps provides a structured approach to evaluating and strengthening the security posture of your Microsoft 365 environment. Organizations must regularly assess security configurations, identify vulnerabilities, and understand potential risks to protect sensitive data and ensure compliance. This guide outlines a practical step-by-step methodology to review existing security controls, […]
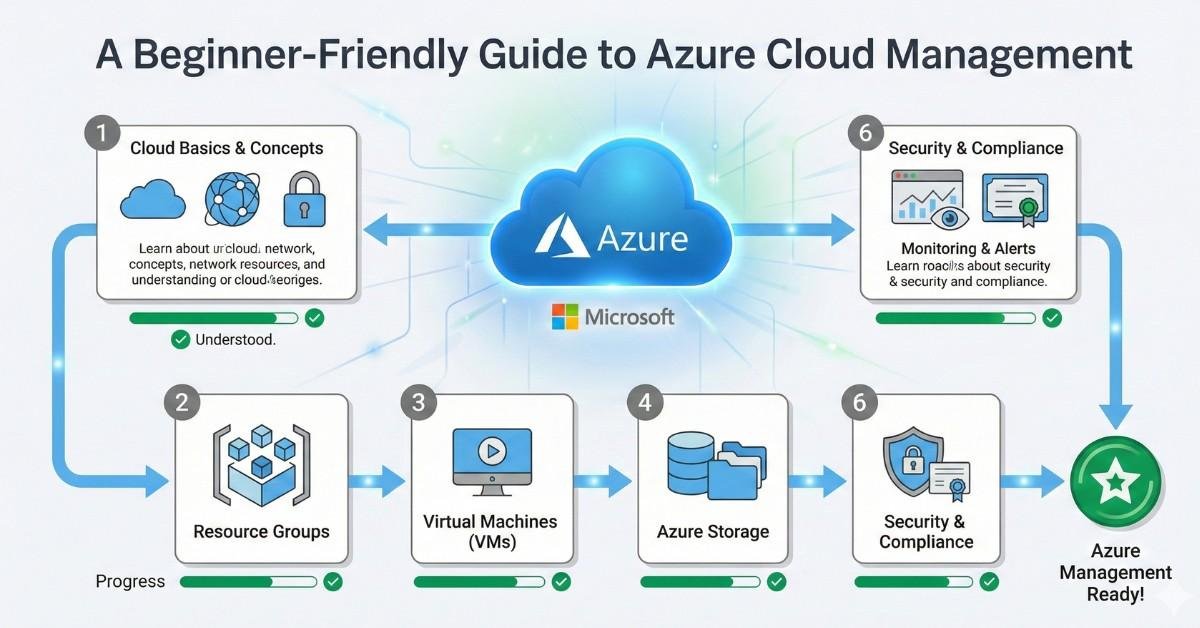
Managing cloud infrastructure can be overwhelming, especially for businesses just beginning their cloud journey. Microsoft Azure offers a robust set of services to help you deploy, manage, and scale your workloads but without a clear strategy, this can lead to higher costs, reduced visibility, and increased security risks. In this guide, NG Cloud Security walks you through […]
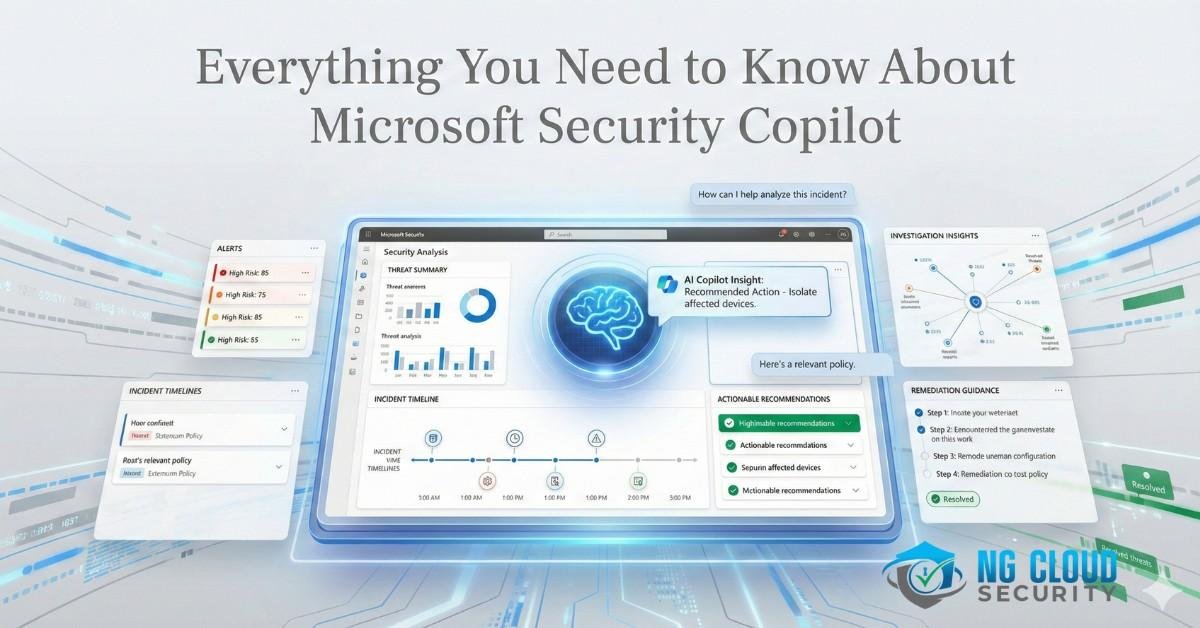
In today’s ever-evolving digital landscape, staying ahead of cyber threats requires more than just advanced tools, it demands intelligent, AI-driven solutions. Microsoft Security Copilot is one such innovation that’s transforming how businesses detect, investigate, and respond to cyber threats in real-time. Built on the power of generative AI and integrated deeply into Microsoft’s security ecosystem, Security Copilot […]
Microsoft Defender for XDR helps organizations simplify cybersecurity by providing unified threat detection and response across endpoints, identities, email, and cloud environments. As cyber threats continue to grow in complexity, managing multiple disconnected security tools becomes challenging and inefficient. Microsoft Defender for XDR removes security silos by bringing all security signals into a single platform, […]