Top 20 Security Concerns In Cloud Computing You Should Know
Cloud computing has completely changed how businesses manage infrastructure, applications, and data. Organizations now rely on cloud platforms for flexibility, scalability, collaboration, and cost optimization. From startups to global enterprises, cloud adoption continues to grow rapidly across every industry.
However, as cloud adoption increases, so do the security concerns in cloud computing. Many businesses move workloads to the cloud without fully understanding the risks involved. In my experience, companies often focus heavily on performance and scalability while overlooking cloud security fundamentals that protect sensitive business data.
A single misconfigured cloud setting, weak password, unsecured API, or lack of visibility can expose an organization to serious cyber threats. These risks can lead to data breaches, operational downtime, compliance penalties, financial losses, and reputational damage.
If your organization uses AWS, Microsoft Azure, Google Cloud, or hybrid cloud environments, understanding these risks is essential for long term security and business continuity.
You can also explore our guide on cloud security challenges to understand modern cloud risks in greater detail.
Why Cloud Security Matters
Cloud environments store highly sensitive business information including customer records, intellectual property, financial data, employee information, applications, and communication systems.
Modern businesses commonly use:
- Infrastructure as a Service
- Platform as a Service
- Software as a Service
While these cloud models improve efficiency, they also increase the attack surface. Every application, API, user account, device, and integration creates another potential entry point for attackers.
Organizations that fail to secure cloud environments properly may face:
- Data breaches
- Ransomware attacks
- Compliance violations
- Insider threats
- Unauthorized access
- Service disruptions
- Financial penalties
Businesses investing in proactive cloud security strategies are better prepared to reduce risks and maintain customer trust.
For organizations planning secure cloud adoption, our cloud security services and cloud security assessment solutions can help strengthen visibility and protection.
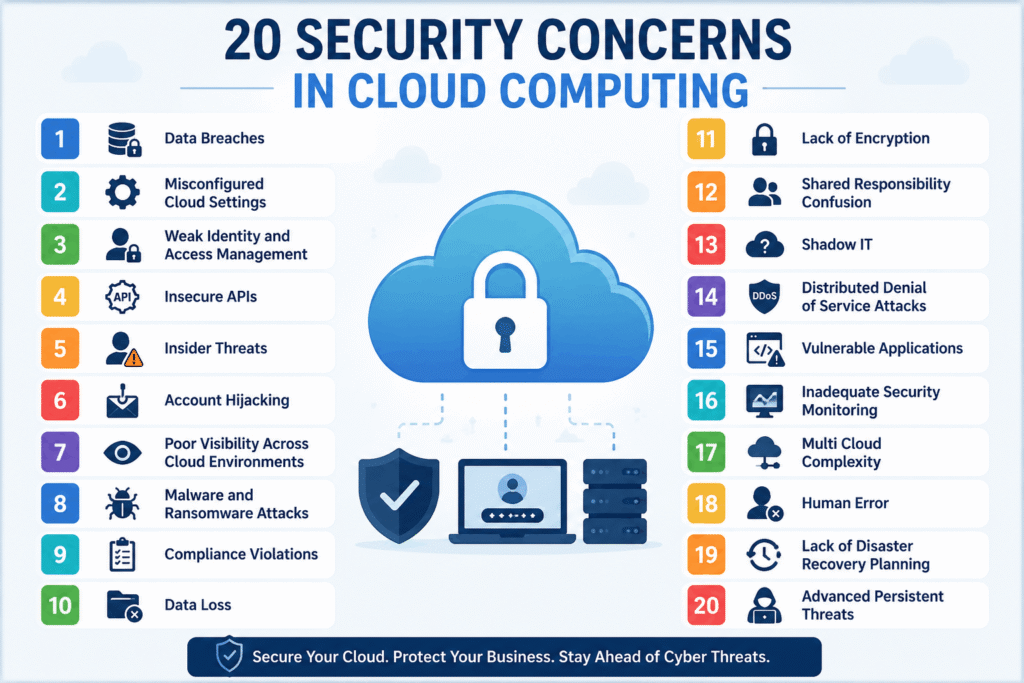
1. Data Breaches
Data breaches remain one of the biggest security concerns in cloud computing. Attackers target cloud environments because they contain valuable customer information, business records, and financial data.
Weak authentication, poor access management, and exposed storage systems often lead to unauthorized access.
Businesses should use encryption, access controls, and continuous monitoring to reduce breach risks.
2. Misconfigured Cloud Settings
Cloud misconfigurations are among the most common causes of cloud security incidents.
Publicly exposed storage buckets, improperly configured databases, and open ports can accidentally expose sensitive information to the internet.
Regular cloud audits and automated configuration reviews help minimize these risks.
3. Weak Identity And Access Management
Identity and Access Management plays a major role in protecting cloud infrastructure.
When users receive unnecessary permissions, attackers can gain broader access after compromising a single account.
Organizations should follow least privilege access principles and regularly review user permissions.
Learn more about modern identity protection in our guide on Identity and Access Management benefits.
4. Insecure APIs
Cloud platforms depend heavily on APIs for communication between applications and services.
Poorly secured APIs can expose sensitive information and create entry points for attackers.
Strong authentication, API gateways, encryption, and regular security testing are critical for API protection.
5. Insider Threats
Not every threat comes from external attackers. Employees, contractors, or vendors with cloud access may accidentally or intentionally expose sensitive information.
Insider threats often bypass traditional security tools because the user already has authorized access.
User monitoring and access control policies help reduce insider related risks.
6. Account Hijacking
Cybercriminals commonly use phishing attacks, stolen credentials, and brute force techniques to compromise cloud accounts.
Once attackers gain access, they may steal data, deploy malware, or move laterally across systems.
Using Multi Factor Authentication significantly improves account security.
7. Poor Visibility Across Cloud Environments
Many organizations operate across multiple cloud providers and hybrid environments.
Without centralized monitoring, security teams struggle to identify suspicious activity, unauthorized access, or risky configurations.
Cloud Security Posture Management solutions improve visibility and help security teams detect threats faster.
8. Malware And Ransomware Attacks
Ransomware attacks targeting cloud environments continue to increase.
Attackers may encrypt business critical data, disrupt operations, or demand financial payments for recovery.
Regular backups, endpoint protection, employee awareness training, and real time threat monitoring reduce ransomware risks.
Businesses looking to strengthen endpoint protection can also explore our article on top endpoint security threats.
9. Compliance Violations
Organizations operating in healthcare, finance, ecommerce, and government sectors must comply with industry regulations.
Improper cloud security controls can result in non compliance with GDPR, HIPAA, PCI DSS, and other standards.
Regular security assessments help organizations maintain compliance readiness.
You may also find our guide on SOC 2 Trust Principles useful for understanding compliance requirements.
10. Data Loss
Cloud data can be lost because of accidental deletion, ransomware attacks, hardware failures, or failed backup systems.
Organizations should implement automated backups and disaster recovery planning to reduce operational downtime.
11. Lack Of Encryption
Sensitive business information should always be encrypted both in transit and at rest.
Without encryption, attackers may intercept or access sensitive data more easily.
Strong encryption policies improve both security and compliance.
12. Shared Responsibility Confusion
Many organizations misunderstand the shared responsibility model in cloud computing.
Cloud providers secure the infrastructure itself, but businesses remain responsible for protecting applications, user accounts, configurations, and data.
Understanding these responsibilities is essential for avoiding security gaps.
13. Shadow IT
Employees sometimes use unauthorized cloud applications without approval from the IT department.
These unmanaged applications create security, compliance, and visibility risks because sensitive data may move outside approved systems.
Organizations should implement strict cloud usage policies and monitor unauthorized tools.
14. Distributed Denial Of Service Attacks
Distributed Denial of Service attacks attempt to overwhelm cloud services with massive amounts of traffic.
These attacks can disrupt applications, impact availability, and affect customer experience.
Traffic filtering and cloud based DDoS protection services help reduce this risk.
15. Vulnerable Applications
Applications hosted in cloud environments may contain outdated software, insecure code, or missing security patches.
Attackers actively scan for vulnerabilities in web applications and cloud workloads.
Regular vulnerability assessments, penetration testing, and patch management improve security.
16. Inadequate Security Monitoring
Without continuous monitoring, organizations may fail to detect suspicious activity early.
Security monitoring solutions help identify unusual behavior, unauthorized access attempts, and policy violations before major damage occurs.
Organizations can strengthen detection capabilities using Microsoft Sentinel solutions and Defender for XDR services.
17. Multi Cloud Complexity
Managing security across multiple cloud providers becomes increasingly difficult as environments grow.
Different platforms often use different policies, controls, and security configurations.
Centralized cloud security management helps maintain consistency across environments.
18. Human Error
Human mistakes continue to cause major cloud security incidents.
Employees may accidentally expose credentials, misconfigure services, or click phishing links.
Regular cybersecurity awareness training is one of the most effective ways to reduce human related risks.
Our guide on email security against phishing attacks explains how phishing threats impact organizations.
19. Lack Of Disaster Recovery Planning
Unexpected outages, cyberattacks, and infrastructure failures can affect cloud services at any time.
A strong disaster recovery strategy helps businesses restore systems quickly and minimize downtime.
Organizations should regularly test recovery plans and backup systems.
20. Advanced Persistent Threats
Advanced Persistent Threats involve highly skilled attackers who remain hidden inside systems for extended periods.
These attacks focus on stealing sensitive data and maintaining long term access without detection.
Organizations need continuous monitoring, threat intelligence, and incident response capabilities to defend against advanced attacks.
Additional Cloud Security Risks Businesses Often Ignore
Third Party Vendor Risks
Third party vendors and external integrations can introduce additional cloud security risks.
If a connected vendor experiences a security breach, your organization may also become exposed.
Vendor risk assessments and strict access reviews are essential.
Phishing And Social Engineering Attacks
Phishing remains one of the most effective ways attackers steal cloud credentials.
Employees may unknowingly share login information through fake emails or malicious websites.
Security awareness programs and strong authentication policies reduce phishing related risks.
Container And Kubernetes Security Risks
Modern cloud applications increasingly rely on containers and Kubernetes environments.
Improper container configurations, insecure images, and weak orchestration settings can create serious vulnerabilities.
Container security scanning and runtime monitoring help improve protection.
How Businesses Can Improve Cloud Security
Understanding security concerns in cloud computing is only the first step. Organizations also need a proactive security strategy.
Use Multi Factor Authentication
Multi Factor Authentication adds an extra layer of protection beyond passwords.
Conduct Regular Security Audits
Regular audits help identify vulnerabilities, compliance gaps, and risky cloud configurations.
Monitor Cloud Activity Continuously
Continuous monitoring improves visibility and helps security teams detect threats faster.
Encrypt Sensitive Information
Encryption protects business data from unauthorized access and interception.
Train Employees On Cybersecurity
Employees should understand phishing risks, password security, and safe cloud practices.
Implement Zero Trust Security
Zero Trust security verifies every user and device before granting access.
You can learn more from our guides on Zero Trust Network Access vs VPN and Zero Trust security principles.
Final Thoughts
Cloud computing continues to transform how businesses operate, collaborate, and scale. However, cyber threats continue to evolve alongside cloud technologies.
Organizations that ignore security concerns in cloud computing often face operational disruption, compliance challenges, and financial damage.
A proactive cloud security strategy improves visibility, strengthens protection, supports compliance, and helps businesses confidently scale cloud operations.
By understanding these risks and implementing proper safeguards, businesses can securely adopt cloud technologies while reducing exposure to modern cyber threats.
