What Is Digital Certificate in Network Security and How It Protects Data
In modern network environments, trust is the foundation of secure communication. From my experience working with different business systems, one gap I often notice is that many organizations invest in security tools but overlook identity verification. This is where a digital certificate in network security becomes critical.
A digital certificate is not just a technical file. It is the backbone of secure communication, authentication, and data protection across the internet. Without it, there is no reliable way to verify whether a system, user, or website is genuine.
What Is a Digital Certificate in Network Security
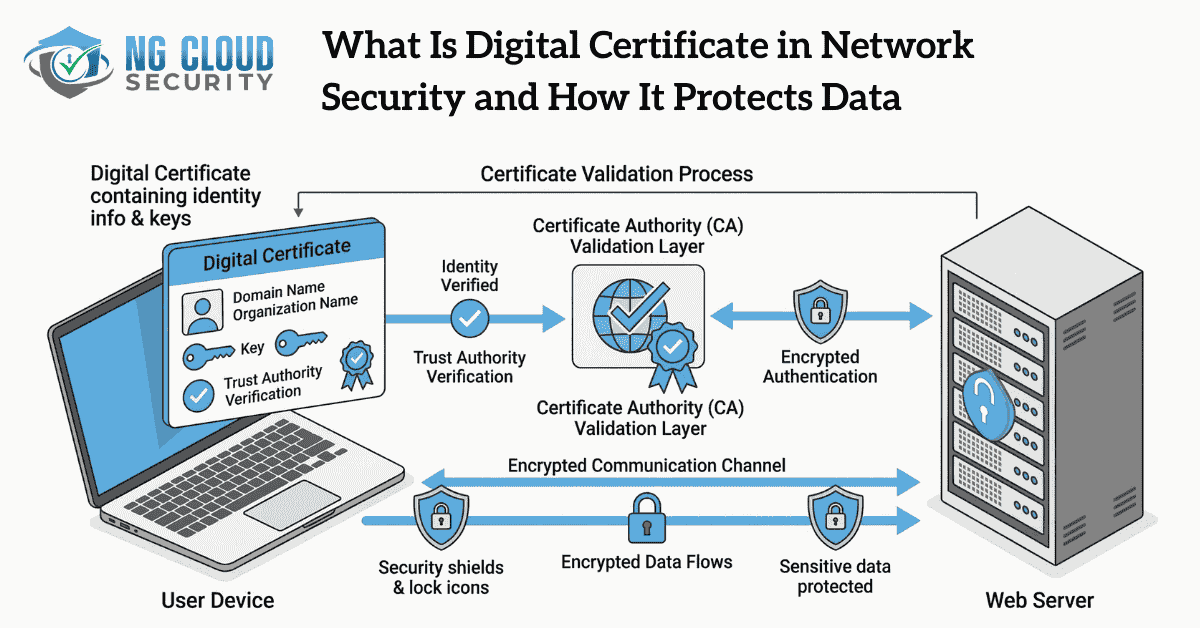
A digital certificate is an electronic credential that verifies the identity of a user, device, or server using cryptography and Public Key Infrastructure. It creates a trusted connection between a public key and an entity.
It includes key details such as the certificate owner, public key, issuing authority, and a digital signature. This ensures that the certificate is authentic and cannot be tampered with.

In simple terms, it works like a digital identity card that proves legitimacy in online communication.
Core Components of a Digital Certificate
To understand it properly, it is important to look at its structure.
A digital certificate contains a public key, identity information, validity period, and a digital signature from the issuing authority. The validity period ensures that certificates expire and must be renewed, which maintains security over time.
Another important concept is Public Key Infrastructure, which manages how certificates are issued, validated, and revoked.
If you want to understand how identity systems work at a broader level, you can explore identity and access management in enterprise environments.
How Digital Certificates Work
The working process of a digital certificate is based on trust and verification.
When a user connects to a secure website, the server shares its digital certificate. The browser verifies this certificate with a trusted Certificate Authority. Once verified, a secure session is established.
This process uses a public key and a private key. The public key encrypts the data, and the private key decrypts it. This ensures that even if data is intercepted, it cannot be read.
In real world implementations, this mechanism plays a major role in protecting sensitive business data and user information.
Role of Certificate Authority
A Certificate Authority is a trusted third party that issues digital certificates. It verifies the identity of the requester before issuing the certificate.
The entire trust model of digital communication depends on the credibility of the Certificate Authority. If the authority is trusted, the certificate is trusted.
Some organizations also use private Certificate Authorities for internal systems. This is common in enterprises that follow a Zero Trust security approach where identity verification is enforced at every level.
Types of Digital Certificates
Different types of digital certificates are used based on the purpose and level of trust required.
SSL or TLS Certificates
These certificates secure communication between users and web servers. They enable HTTPS and encrypted communication and protect sensitive information during transmission.
Code Signing Certificates
These certificates verify that software or applications are genuine and have not been altered after publishing.
Client Certificates
These are used to authenticate users or devices before granting access to systems or networks.
Email Certificates
These secure email communication by encrypting messages and verifying sender identity. You can also explore how this works in detail in email security strategies.
Validation Levels
Certificates also come with different validation levels such as domain validation, organization validation, and extended validation. Each level provides a different degree of trust.
Benefits of Digital Certificate in Network Security
Digital certificates provide strong security benefits that go beyond basic encryption.
They ensure secure communication, verify identity, and protect data integrity. They also help organizations build trust with users and customers.
Another important advantage is scalability. Certificates can be issued, renewed, and revoked efficiently, making them suitable for growing organizations.
For businesses adopting cloud environments, certificates play a key role in securing communication, which aligns with cloud security best practices.
How Digital Certificates Protect Data
Digital certificates protect data through three core mechanisms.
First is encryption, which converts data into a secure format that cannot be understood by attackers.
Second is authentication, which verifies the identity of both sender and receiver.
Third is data integrity, which ensures that information is not modified during transmission.
Real World Use Cases
Digital certificates are used across multiple areas in network security.
They secure websites through HTTPS, protect email communication, validate software authenticity, and enable secure remote access.
They are also widely used in cloud and enterprise systems to secure communication between services and users.
In industries such as finance, healthcare, and ecommerce, digital certificates are essential for compliance and data protection.
Digital Certificates vs Digital Signatures
A digital certificate and a digital signature serve different purposes but work together.
A digital certificate verifies identity and enables secure communication. A digital signature ensures that data or documents are authentic and have not been altered.
In simple terms, the certificate confirms identity, while the signature confirms integrity.
Challenges and Limitations
Despite their importance, digital certificates come with challenges.
They require proper configuration and lifecycle management. Expired certificates can cause service disruption and trust issues.
There is also dependency on trusted authorities. If a Certificate Authority is compromised, it can impact security.
However, these challenges can be minimized with proper management and monitoring.
Best Practices for Implementation
From my experience, organizations should focus on proper certificate lifecycle management.
Always use trusted Certificate Authorities. Monitor certificate validity and renew them on time. Secure private keys properly and use automation where possible.
Having centralized visibility of certificates across systems improves security posture and reduces operational risks.
Conclusion
A digital certificate in network security is a fundamental component for secure communication, identity verification, and data protection. It builds trust between systems and ensures that sensitive information remains secure.
As cyber threats continue to evolve, the role of digital certificates becomes even more important. Organizations that implement and manage certificates effectively are better positioned to protect their data and maintain trust in the digital world.