Blog
Explore cybersecurity insights, cloud security strategies, Microsoft 365 guidance, and expert tips to protect modern businesses from evolving cyber threats.
In an era where cyberattacks occur every 39 seconds, securing every access point to your network is more critical than ever. Endpoint security is a modern cybersecurity approach that safeguards every device known as an endpoint that connects to your corporate network. Whether it’s a laptop, mobile phone, or IoT device, NG Cloud Security helps […]
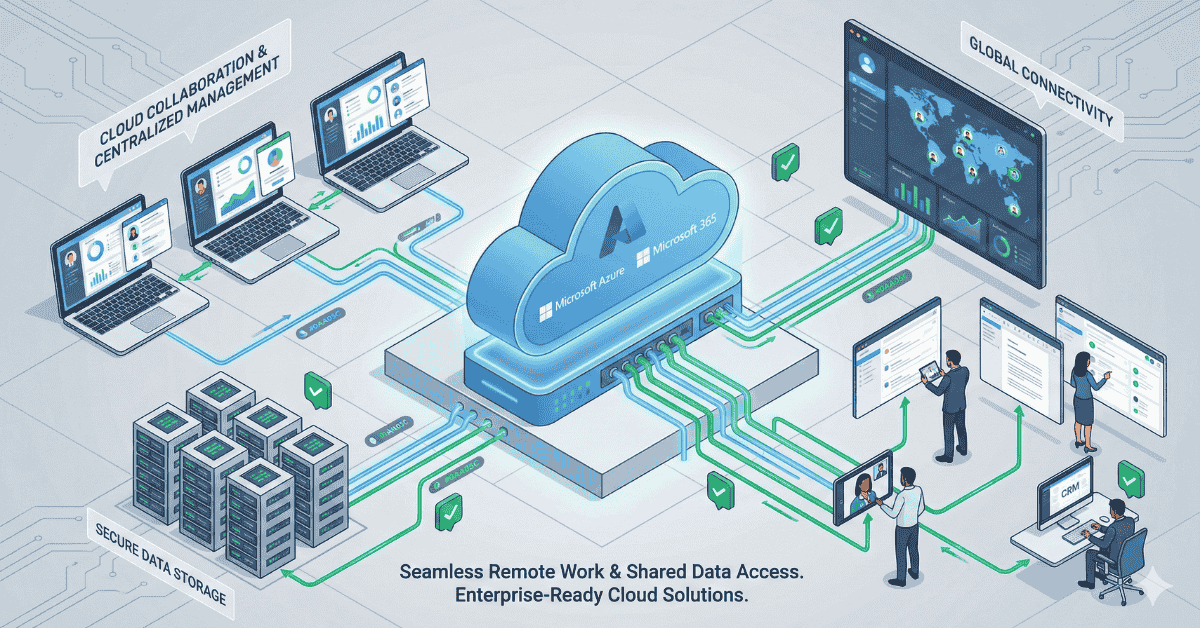
Microsoft 365 Managed Services help organizations maintain secure, optimized, and continuously available IT operations in today’s digital-first business environment. As companies increasingly rely on cloud platforms for collaboration and productivity, even minor downtime can impact revenue and customer trust. Managed services ensure proactive monitoring, security management, performance optimization, and ongoing support across Microsoft 365 and […]
Why Businesses Need Cloud Security Consulting Services in 2026 is becoming a critical question as organizations rapidly adopt cloud technologies to improve scalability, agility, and cost efficiency. While cloud adoption enables innovation, it also introduces risks such as cyber threats, compliance challenges, and data breaches. Cloud security consulting helps businesses build secure, resilient, and compliant […]
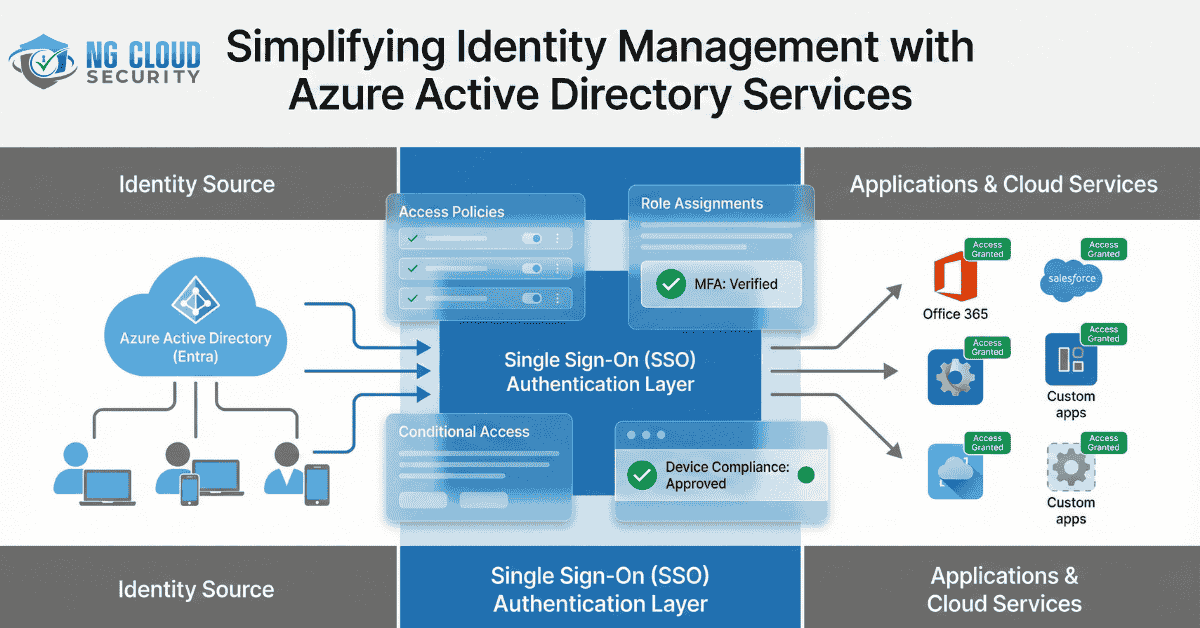
Enterprises face an increasing number of cyber-threats in today’s digital world. These threats target the weakest security link: identity. Securing identity is now a must-have with hybrid work, cloud adoption and more sophisticated attacks. Azure Active Directory Services, now part of Microsoft Entra, provides enterprises with advanced security and governance to protect users and devices. […]
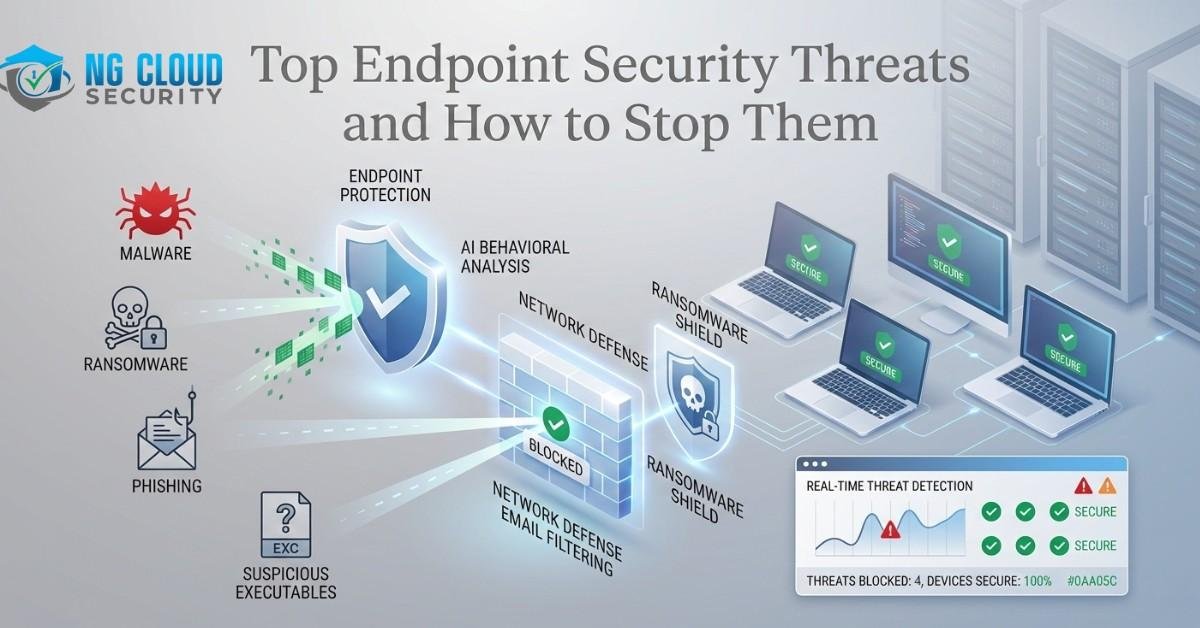
Endpoint Security Threats are becoming one of the biggest cybersecurity challenges in today’s digital landscape. As cyber threats evolve rapidly, organizations must stay proactive in protecting endpoints such as laptops, desktops, and mobile devices from unauthorized access and attacks. NG Cloud Security helps businesses strengthen endpoint protection through advanced security solutions designed to detect, prevent, […]
In today’s digitally-driven world, email remains one of the most widely used communication channels for both businesses and individuals. While emails offer convenience and efficiency, they are also a prime target for cybercriminals. One of the most prevalent threats is phishing attacks—deceptive attempts by attackers to trick users into revealing sensitive information suchas passwords, credit […]
Businesses across India are embracing the cloud to stay agile, efficient, and future-ready. Whether it’s about scaling operations, improving collaboration, or strengthening data security, cloud technology has become the backbone of digital transformation. However, the migration process itself can be complex — involving risks of downtime, data loss, and security breaches ifnot executed correctly. That’s […]
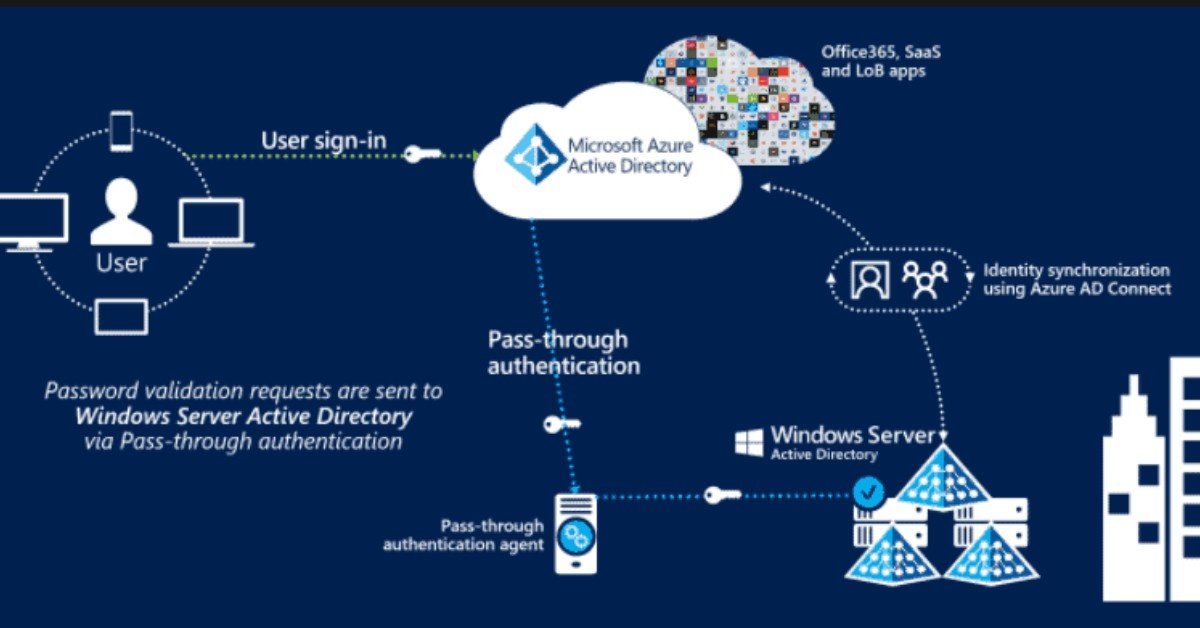
In today’s cloud-driven business environment, secure identity and access management have become essential. As organizations embrace hybrid and multi-cloud infrastructures, the need for centralized identity control, enhanced user authentication, and secure access to corporate resources has grown significantly. Azure Active Directory Services (Azure AD) has emerged as a leading solution for these challenges, offering a […]
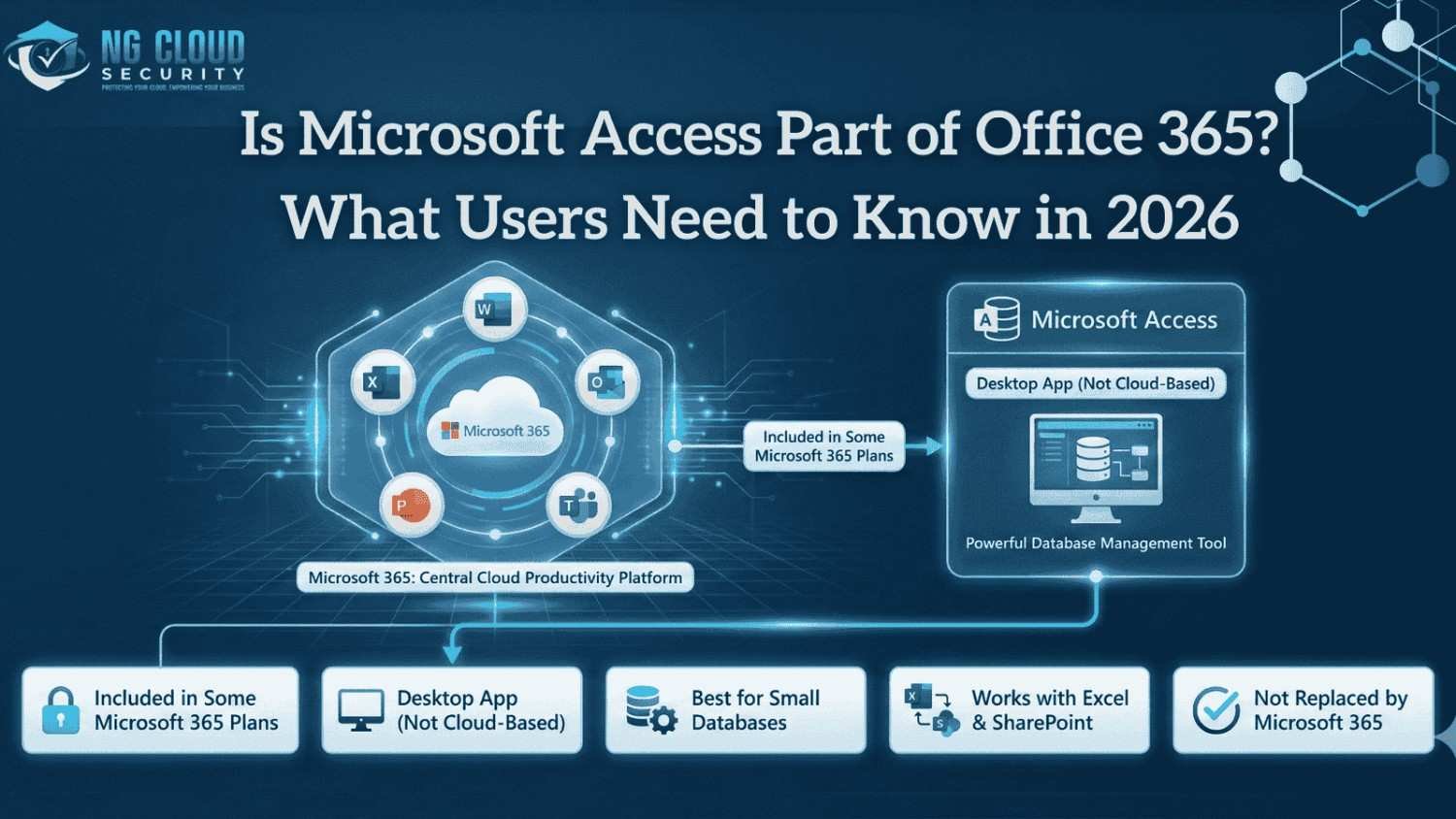
In my experience working with organizations adopting Microsoft 365, one question keeps coming up again and again. Is Microsoft Access part of Office 365, and does it still make sense to rely on it in a cloud first environment? The confusion is understandable. Microsoft 365 has evolved rapidly, focusing more on cloud services, browser based […]
When business leaders ask me how long does cloud migration take, my honest answer is always it depends. In enterprise environments, cloud migration is not a single task. It is a structured transformation that impacts infrastructure, applications, security, and operations. In my experience, organizations that first understand the different types of cloud migration approaches move faster and avoid […]