Blog
Explore cybersecurity insights, cloud security strategies, Microsoft 365 guidance, and expert tips to protect modern businesses from evolving cyber threats.
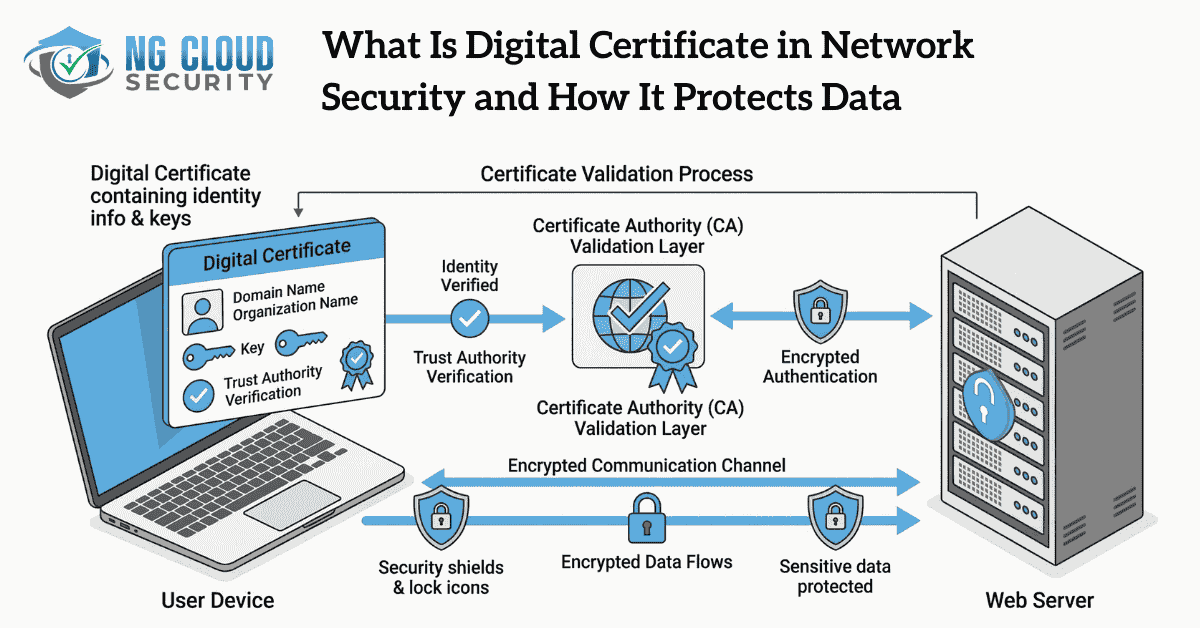
In modern network environments, trust is the foundation of secure communication. From my experience working with different business systems, one gap I often notice is that many organizations invest in security tools but overlook identity verification. This is where a digital certificate in network security becomes critical. A digital certificate is not just a technical […]
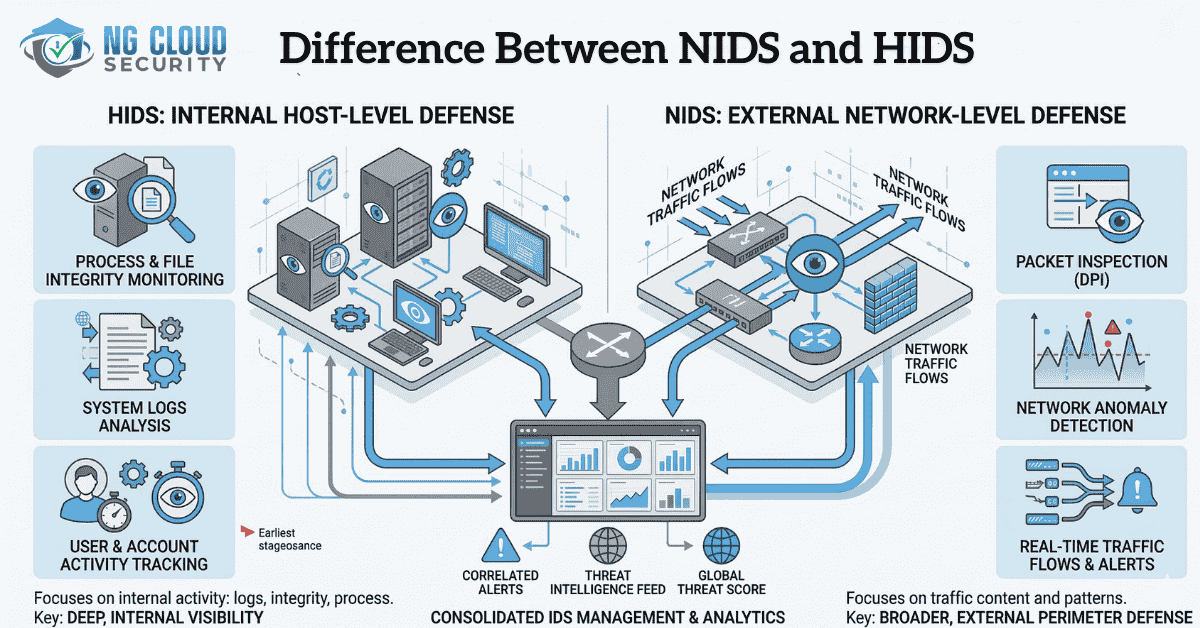
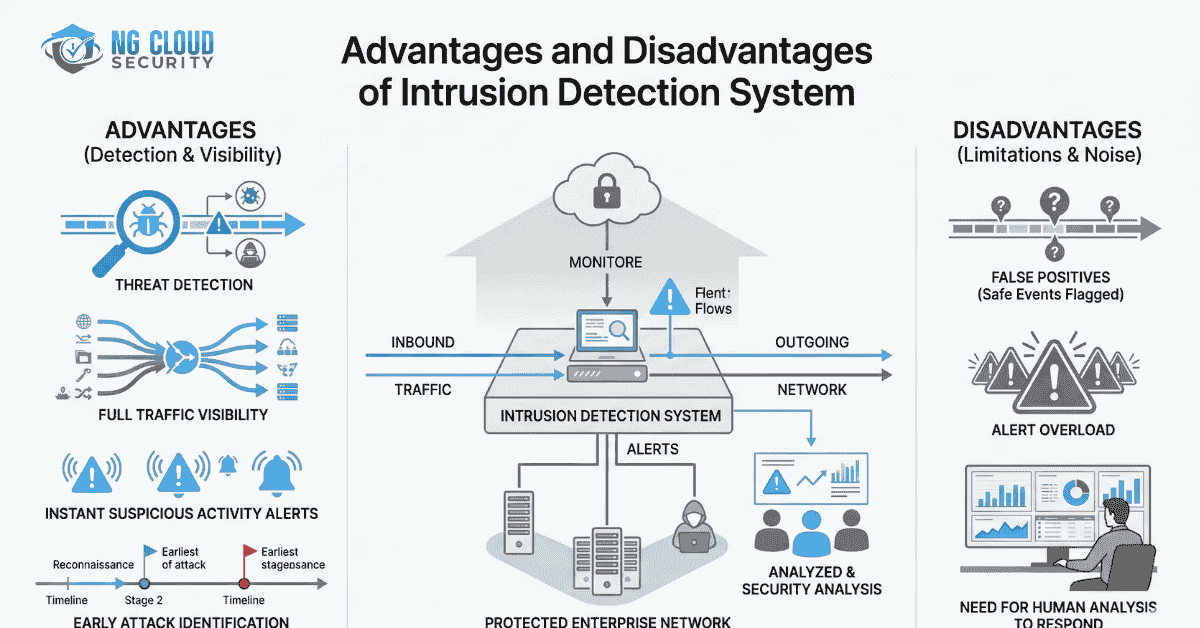
Cybersecurity threats continue to evolve as organizations expand their digital infrastructure. Modern environments now include cloud platforms, remote work systems, SaaS applications, and connected devices. Because of this growing complexity, monitoring suspicious activity across systems and networks has become a critical part of security operations. Intrusion detection technologies help security teams detect malicious activities before […]
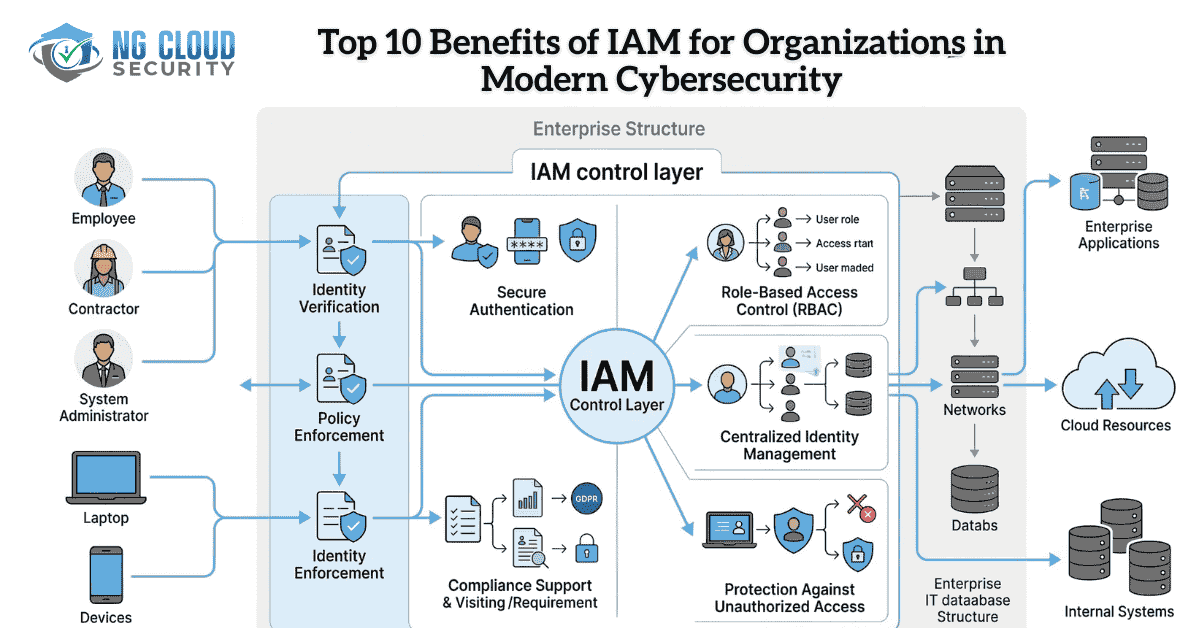
Digital transformation has expanded how organizations access applications, data, and cloud platforms through secure cloud migration strategies. Employees, contractors, and partners now connect from multiple locations and devices. While this improves productivity, it also introduces serious security risks if access is not controlled properly. This is where Identity and Access Management becomes essential. Identity and […]
Cyber threats are becoming more advanced every year, and organizations must continuously monitor their networks to detect suspicious activity before it turns into a serious security incident. One of the most widely used technologies for this purpose is an intrusion detection system. An intrusion detection system helps organizations monitor network traffic, detect unusual behavior, and […]
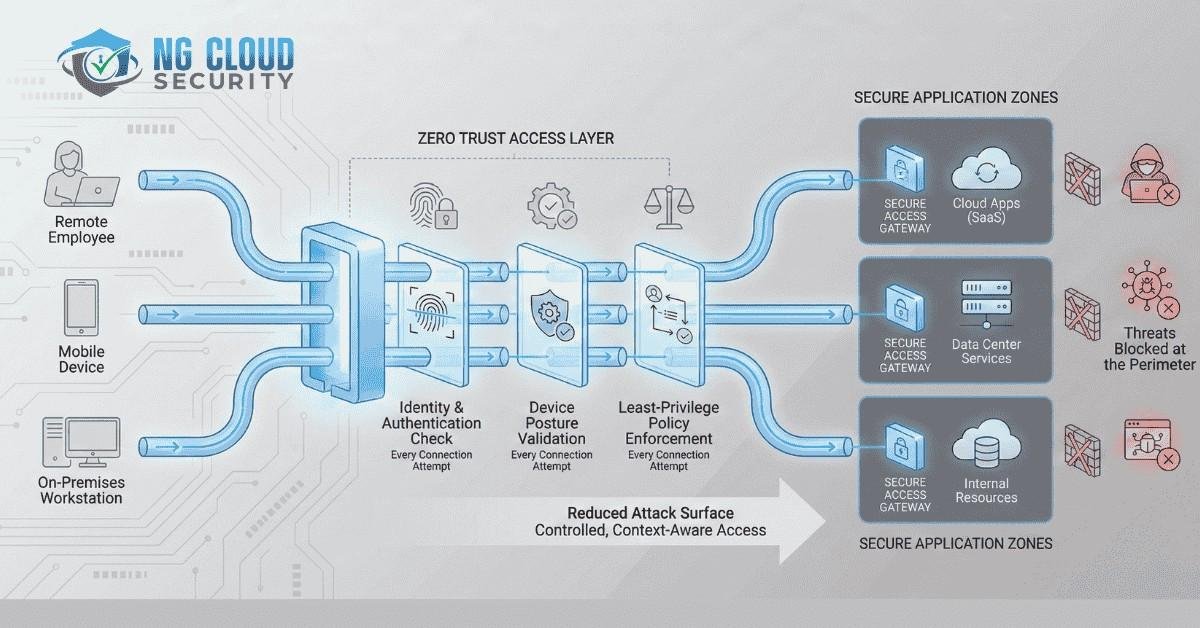
Zero Trust has moved from being a trending concept to a core enterprise security requirement. Yet many leaders still ask the same question, what is zero trust network access and how does it truly protect modern organizations? In my experience working with enterprise environments across industries, the biggest shift in security thinking has been this. […]
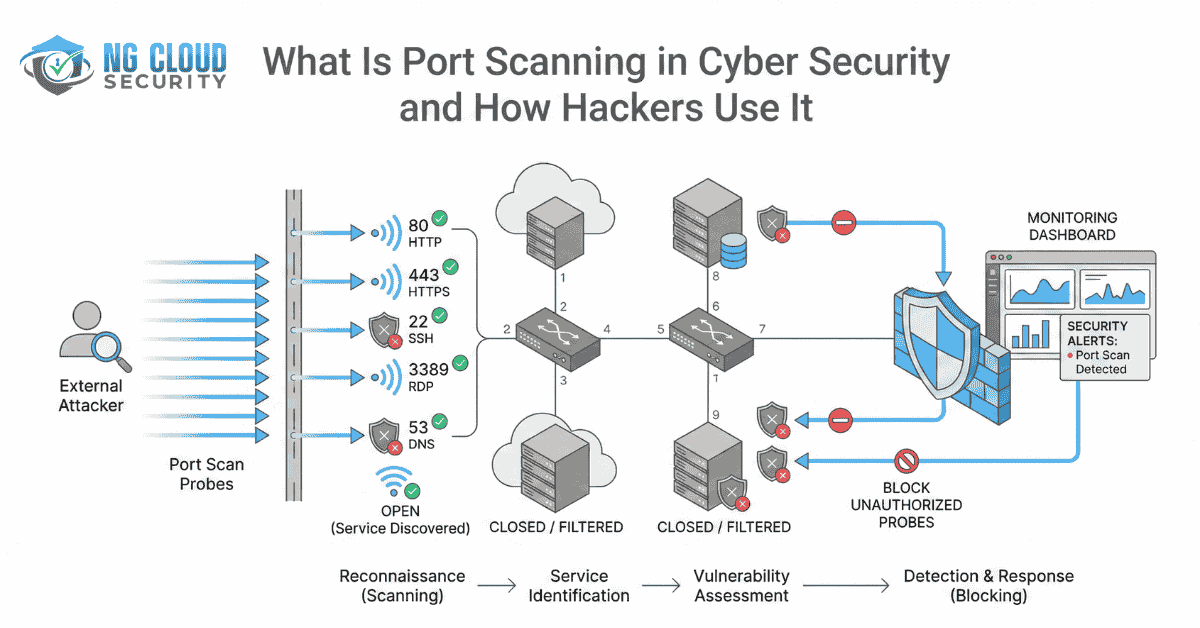
If you are searching for what is port scanning in cyber security, you are already thinking like a security leader. Port scanning is one of the most common reconnaissance techniques used in modern cyber attacks. It is often the first step attackers take before attempting to exploit a system. From my experience working with organizations […]
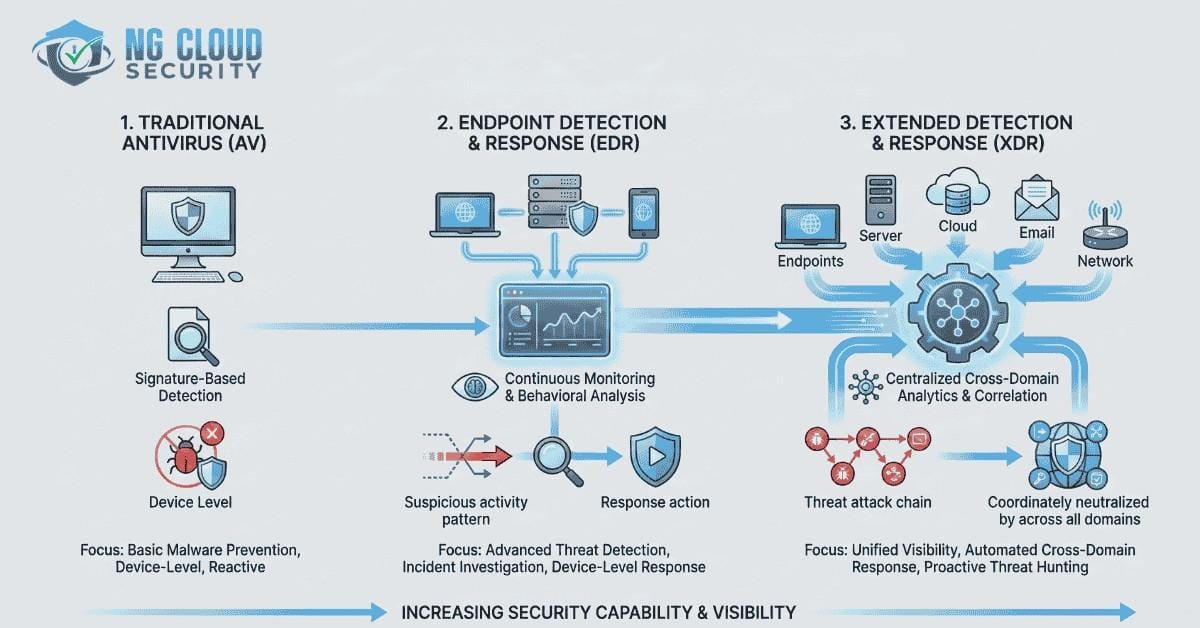
Endpoint security has evolved rapidly over the past decade. As organizations move to cloud platforms, remote work models, and mobile devices, protecting endpoints has become a core pillar of modern cybersecurity. If you are new to this topic, you can also read our detailed guide on what is endpoint security and how it works. Understanding […]
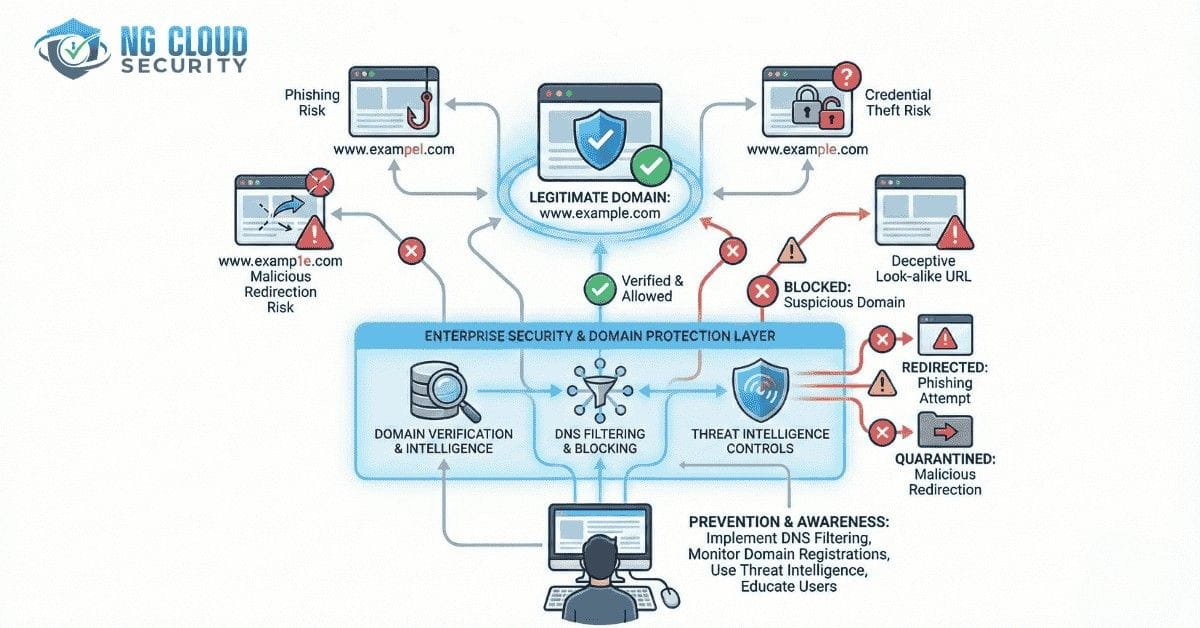
Typosquatting in cyber security is a growing threat that exploits simple human typing errors to steal credentials, distribute malware, and damage brand reputation. While many organizations focus on firewalls and endpoint tools, domain abuse often remains overlooked. In enterprise environments, a single mistyped URL can lead to phishing, account takeover, business email compromise, and regulatory […]
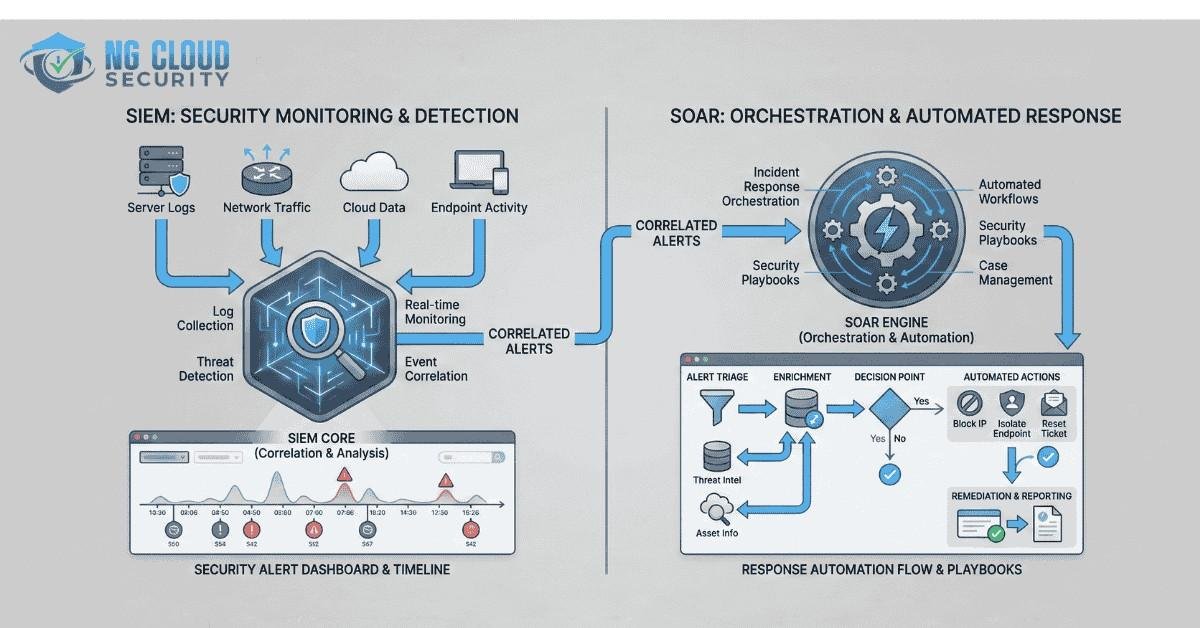
Security teams today are under constant pressure. Alerts are increasing, attack techniques are evolving, and business environments are becoming more complex with cloud adoption, remote work, and regulatory demands. In many organizations, the Security Operations Center acts as the first and last line of defense. One of the most common questions I see security leaders […]
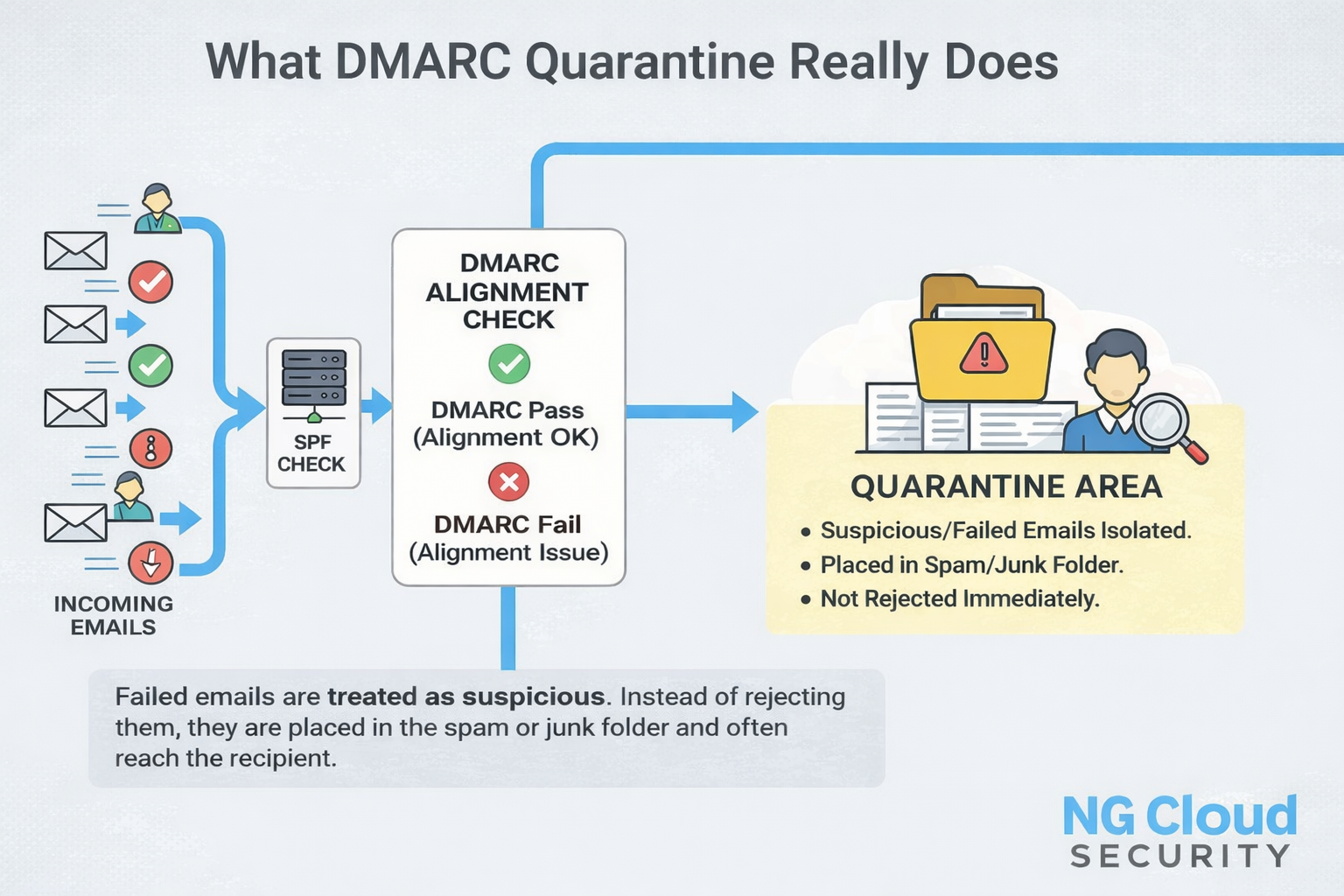
Email remains one of the most trusted channels for business communication, yet it is also one of the most abused. In my experience working with organizations across industries, email authentication issues often surface only after customers report missing invoices or password reset messages. That is usually when DMARC becomes part of the conversation. One of […]