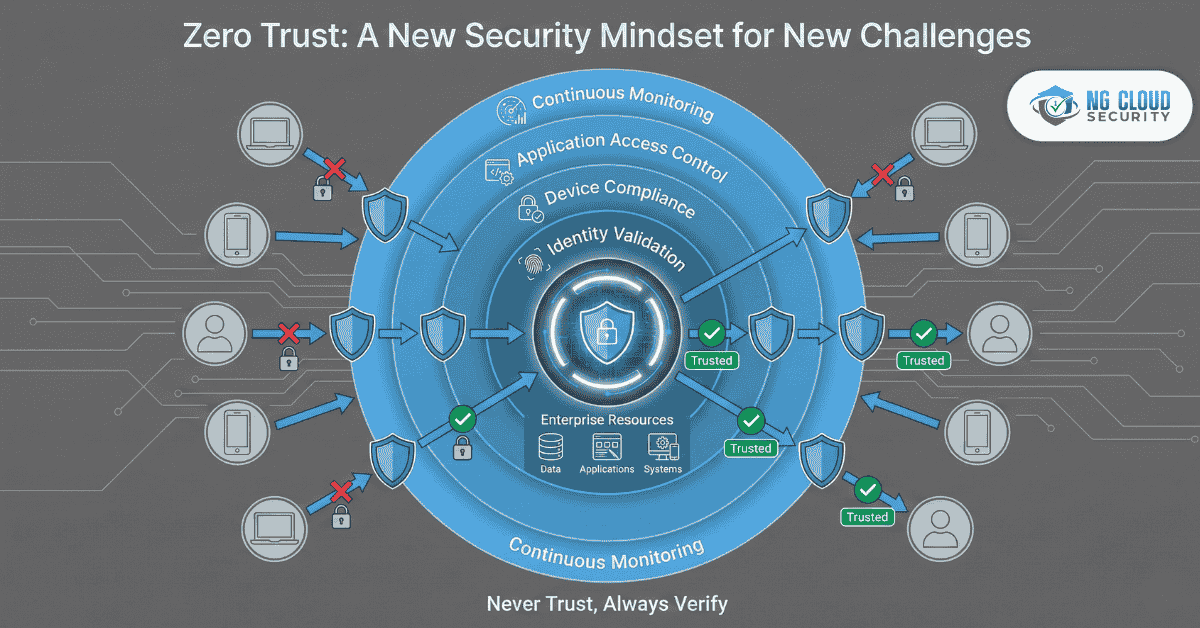
In today’s digital-first world, cyber threats are no longer limited to external attacks. Insider threats, credential theft, and supply chain vulnerabilities have become equally dangerous. Traditional perimeter-based security models that rely on the concept of “trust but verify” are proving inadequate. That’s where Zero Trust security solutions come in — a revolutionary approach that challenges […]
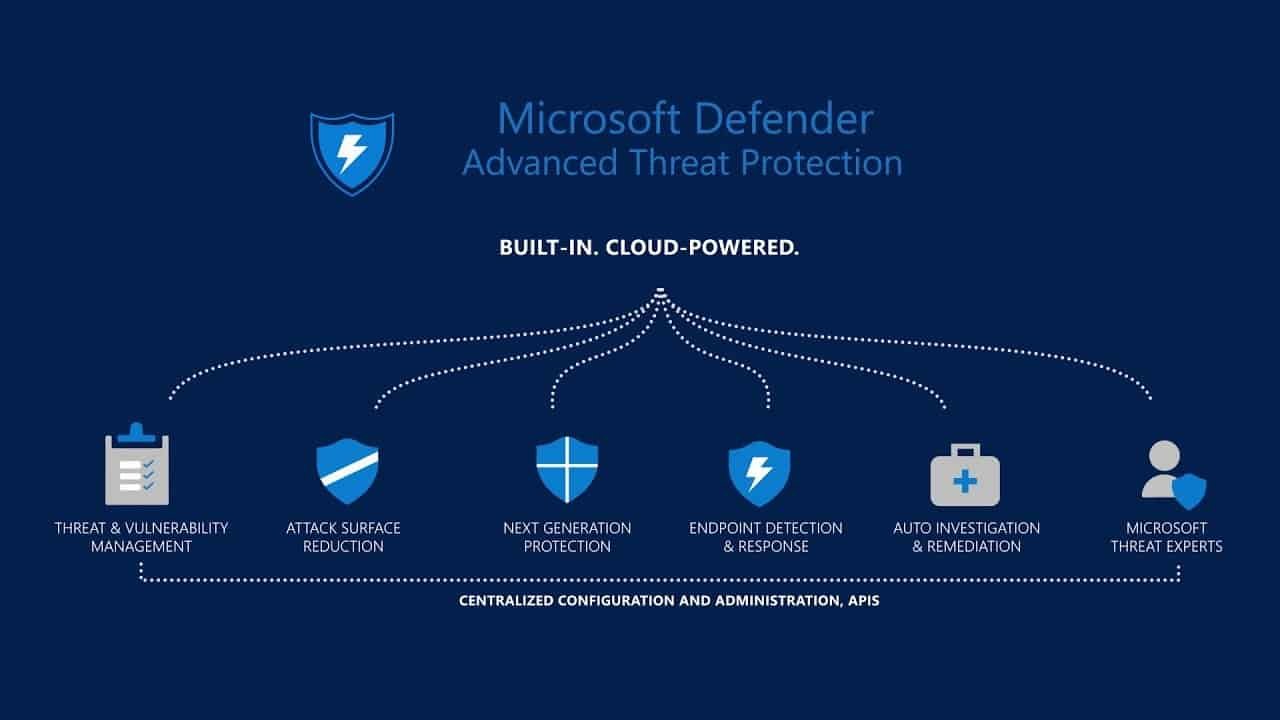
remain a critical concern for businesses as cybercriminals evolve. With hybrid work, mobile devices, and cloud integration, endpoints are among the most targeted attack surfaces. NG Cloud Security helps organizations stay ahead using Microsoft Defender for Endpoint. In 2026, endpoint security stands at the frontline of digital defense.With the rise of hybrid work, mobile access, […]
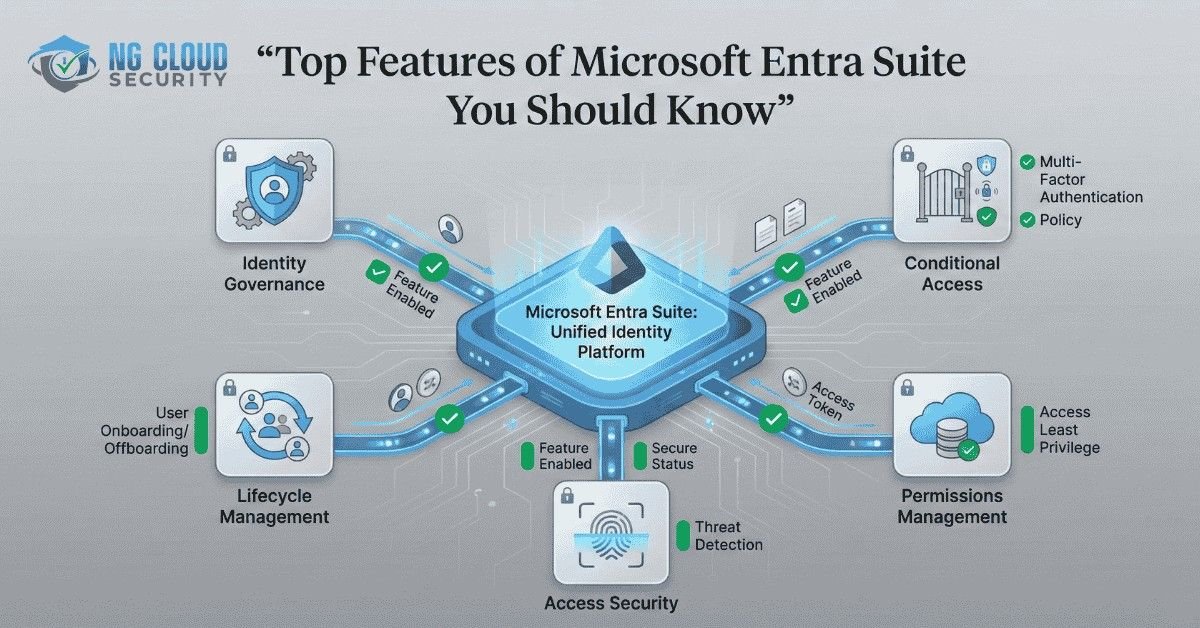
In today’s digital landscape, managing identity and access securely is more critical than ever. As organizations expand across cloud and hybrid environments, the need for a unified identity management solution becomes paramount. Microsoft Entra Suite has emerged as a powerful solution for modern identity and access management (IAM), offering enterprises a way to protect users, […]
In today’s fast-evolving cyber landscape, organizations face threats that are more advanced and harder to detect than ever before. Traditional security solutions that work in isolation often fail to provide comprehensive visibility across an organization’s IT environment. This is where XDR security solutions step in to bridge the gap, and Microsoft has emerged as a […]
In today’s digital-first world, businesses rely heavily on cloud infrastructure for flexibility,scalability, and cost efficiency. While the cloud offers countless advantages, it also comes withrisks that organizations cannot afford to ignore. Cloud Security Challenges are among the mostpressing issues in IT, often putting sensitive data and critical systems at risk if left unaddressed.To build trust […]
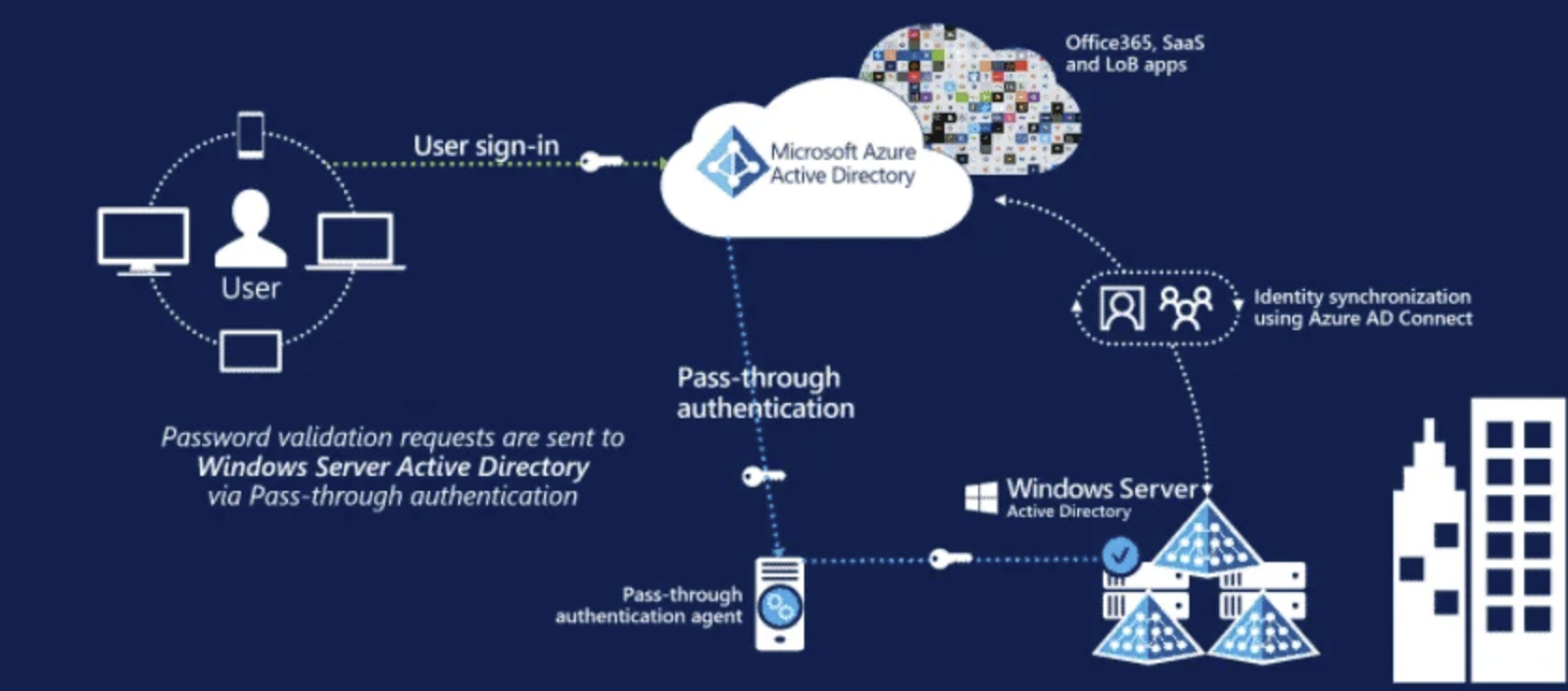
Enterprises face an increasing number of cyber-threats in today’s digital world. These threats target the weakest security link: identity. Securing identity is now a must-have with hybrid work, cloud adoption and more sophisticated attacks. Azure Active Directory Services, now part of Microsoft Entra, provides enterprises with advanced security and governance to protect users and devices. […]
In today’s digital-first world, the biggest risks to data often come from within—not just from hackers or malicious outsiders. Insider threats, whether intentional or accidental, are rising rapidly across industries. This is where Microsoft 365 Insider Risk Management (IRM) becomes a powerful solution for organizations of all sizes.This blog breaks down what Insider Risk Management […]
In today’s digital landscape, Microsoft 365 E5 Identity is essential for organizations looking to enhance their security measures. This suite goes beyond basic access control to provide advanced features that protect identities and resources. With its robust tools, businesses can strengthen their security posture and ensure that only authorized users have access to sensitive data. […]
In today’s world, Microsoft 365 E5 Compliance is essential for businesses of all sizes. Compliance is not just a requirement; it is a crucial part of effective business operations. Organizations must protect sensitive data, ensure regulatory adherence, and maintain trust with their customers. The Microsoft 365 E5 suite provides powerful tools to help manage these challenges […]
If your cloud environment is live, that’s a great first step. But have you checked if it’s secure, meets compliance needs, and is aligned with the Zero Trust model? Many organizations move fast into the cloud without checking for security gaps or compliance issues. An Azure Cloud Security Assessment helps spot those issues before they […]