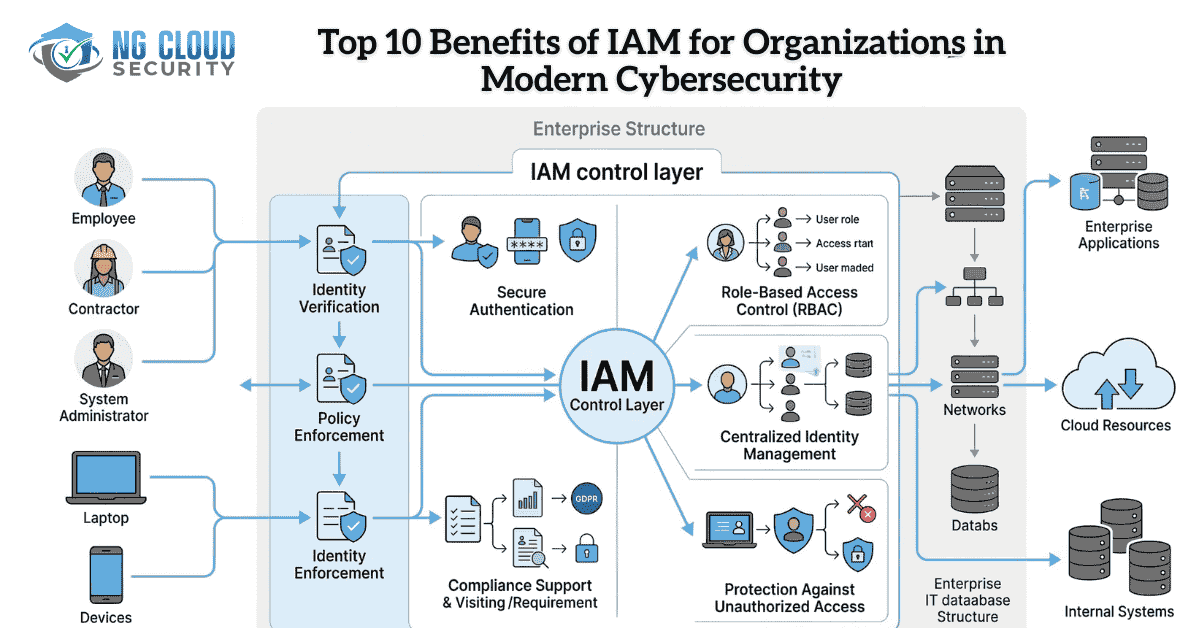
Top 10 Benefits of IAM for Organizations in Modern Cybersecurity
Digital transformation has expanded how organizations access applications, data, and cloud platforms through secure cloud migration strategies. Employees, contractors, and partners now connect from multiple locations and devices. While this improves productivity, it also introduces serious security risks if access is not controlled properly.
This is where Identity and Access Management becomes essential.
Identity and Access Management, commonly known as IAM, is a cybersecurity framework that ensures only authorized users can access specific systems, applications, and data. Instead of relying on traditional perimeter security, modern organizations secure identities as the primary layer of defense.
Understanding the benefits of IAM helps organizations strengthen security posture while improving operational efficiency and regulatory compliance.
What is Identity and Access Management
Identity and Access Management is a collection of technologies and policies used to verify user identities and manage access permissions across enterprise systems.
IAM ensures that every user receives the appropriate level of access based on their role within the organization. It also continuously monitors authentication activity to detect potential threats.
Organizations implementing identity security often rely on centralized identity platforms and governance frameworks delivered through solutions such as modern identity and access management services that integrate identity protection across cloud and enterprise environments.
1. Stronger Protection Against Unauthorized Access
One of the most significant benefits of IAM is the ability to prevent unauthorized users from accessing sensitive business resources.
IAM platforms enforce authentication mechanisms such as multi factor authentication, conditional access policies, and risk based identity verification. These security controls ensure that users must verify their identity before gaining access to critical systems.
By validating user identity at every access point, organizations significantly reduce the risk of account compromise and credential theft.
2. Centralized Control Over User Access
Large organizations typically use dozens of applications across multiple environments. Managing access separately for each system creates complexity and security gaps.
IAM centralizes identity management so administrators can control access policies from a single platform. This approach allows organizations to efficiently manage employee accounts, enforce access policies, and maintain visibility into user privileges across the entire IT environment.
Centralized identity governance also simplifies access audits and administrative processes.
3. Improved Compliance and Security Governance
Regulatory frameworks increasingly require organizations to demonstrate strong identity security controls. IAM systems provide detailed logs, monitoring tools, and access reports that help security teams maintain compliance with industry standards.
These capabilities enable organizations to track who accessed which resources and when. Businesses often combine IAM with structured security reviews such as security assessment and compliance services to ensure identity governance aligns with regulatory requirements.
Effective identity governance reduces compliance risk while strengthening overall cybersecurity posture.
4. Enhanced User Experience Through Single Sign On
Security improvements should not come at the cost of usability. IAM platforms improve user experience through features such as Single Sign On.
Single Sign On allows employees to authenticate once and gain secure access to multiple applications without repeatedly entering credentials. This reduces password fatigue while maintaining strong authentication standards.
As a result, employees spend less time managing login credentials and more time focusing on their work.
5. Reduced Risk of Insider Threats
Insider threats represent a significant cybersecurity concern. Employees or contractors with excessive permissions can unintentionally or intentionally expose sensitive data.
IAM addresses this challenge through role based access control and least privilege principles. These controls ensure that users receive only the permissions required to perform their job functions.
By restricting unnecessary access, organizations minimize the potential impact of insider related security incidents.
6. Secure Access for Remote and Hybrid Workforces
Remote work has permanently changed the enterprise security landscape. Employees now connect to business systems from home networks, mobile devices, and cloud platforms.
IAM enables secure access regardless of location by verifying identity before granting system permissions. Organizations implementing remote security models often combine IAM with modern access frameworks such as Zero Trust Network Access to enforce continuous verification and device level security.
This approach ensures that remote access remains both secure and manageable.
7. Automated User Lifecycle Management
User lifecycle management is a critical but often overlooked aspect of cybersecurity. Manual account management frequently leads to inactive accounts and outdated permissions.
IAM platforms automate provisioning and deprovisioning processes. When employees join the organization, the system automatically assigns the appropriate access permissions based on their role. When employees leave, access is immediately revoked.
Automation ensures that identity governance remains consistent while reducing administrative overhead.
8. Greater Visibility into Identity Activity
Modern IAM solutions provide detailed analytics and monitoring tools that track user authentication behavior.
Security teams gain insight into login attempts, device access patterns, and unusual activity across the organization. This visibility allows organizations to detect potential threats early and respond quickly before incidents escalate.
Identity analytics also supports proactive security monitoring and threat detection strategies.
9. Foundation for Zero Trust Security Architecture
Modern cybersecurity strategies increasingly rely on the Zero Trust model, where every user and device must be verified before accessing resources.
IAM plays a foundational role in enabling Zero Trust by enforcing continuous authentication and dynamic access policies. Organizations building advanced security frameworks frequently align IAM strategies with concepts explained in Zero Trust security architecture.
This identity centric security approach significantly reduces the risk of lateral movement within networks.
10. Improved Operational Efficiency
Managing identities manually across multiple systems is both time consuming and error prone. IAM solutions streamline identity governance by automating access controls and integrating identity policies across platforms.
Security teams can manage user access more efficiently while maintaining consistent security standards. As organizations scale their digital infrastructure, IAM ensures that identity management remains both secure and operationally efficient.
Final Thoughts
In modern cybersecurity, identity has become the primary control point for protecting digital resources. As organizations expand their cloud environments and remote workforce capabilities, controlling user access becomes increasingly critical.
The benefits of IAM extend beyond simple authentication. IAM strengthens security defenses, supports compliance initiatives, improves user productivity, and enables advanced security models such as Zero Trust.
Organizations that prioritize identity security today build a stronger foundation for protecting their systems, data, and users in an increasingly complex threat landscape.