What Is Zero Trust Network Access for Enterprises
Zero Trust has moved from being a trending concept to a core enterprise security requirement. Yet many leaders still ask the same question, what is zero trust network access and how does it truly protect modern organizations?
In my experience working with enterprise environments across industries, the biggest shift in security thinking has been this. We no longer trust users or devices simply because they are inside the network. Today, identity, device health, context, and behavior matter more than location.
This article explains what zero trust network access, how it works, why enterprises need it, and how to implement it in a scalable and business aligned way. If your organization is moving to cloud, supporting remote work, or modernizing legacy infrastructure, this guide will help you understand why Zero Trust Network Access is becoming the foundation of secure digital transformation.
What Is Zero Trust Network Access
Let us begin with the core definition.
What is zero trust network access?
Zero Trust Network Access, often referred to as ZTNA, is a security framework that grants users access to specific applications based on strict identity verification and contextual validation. It assumes that no user, device, or system should be trusted by default, whether inside or outside the corporate network.
Traditional network security models were built around the idea of perimeter defense. Once a user was inside the corporate network through VPN, they were often trusted broadly. This model does not work in a world of cloud computing, hybrid work, mobile devices, and SaaS applications.
ZTNA changes this completely.
Instead of granting access to the entire network, it provides application level access only after verifying:
- User identity
- Device posture
- Location
- Risk signals
- Policy compliance
Access is granted on a least privilege basis and continuously evaluated.
If you want to understand the broader philosophy behind this approach, you can explore our detailed guide on Zero Trust security mindset here:
https://ngcloudsecurity.com/zero-trust-a-new-security-mindset-for-new-challenges/
Why Enterprises Are Moving Away From VPN
For years, VPN was the default solution for remote access. However, the modern threat landscape has exposed several weaknesses in VPN based architectures.
With VPN:
- Users often get network wide access
- Lateral movement becomes easier for attackers
- Compromised credentials can expose entire environments
- Performance suffers due to backhauling traffic
ZTNA addresses these issues by limiting access to specific applications instead of entire networks.
If you are comparing both models in depth, I recommend reading this detailed breakdown on zero trust network access vs vpn.
In enterprise security strategy discussions, the question is no longer VPN or ZTNA. The real question is how quickly can we transition to a Zero Trust based access model without disrupting operations.
Core Principles of Zero Trust Network Access
To truly understand what is zero trust network access, you must understand its principles.
1. Never Trust Always Verify
Every access request is authenticated and authorized. There is no implicit trust based on network location.
2. Least Privilege Access
Users receive access only to the applications and resources required for their roles. Nothing more.
3. Continuous Validation
Access is not a one time approval. Risk signals are continuously evaluated. If a device becomes non compliant or a login appears suspicious, access can be revoked instantly.
4. Micro Segmentation
Applications and services are logically segmented to prevent lateral movement.
5. Identity Driven Security
Identity becomes the new security perimeter. Modern identity platforms such as Microsoft Entra play a critical role.
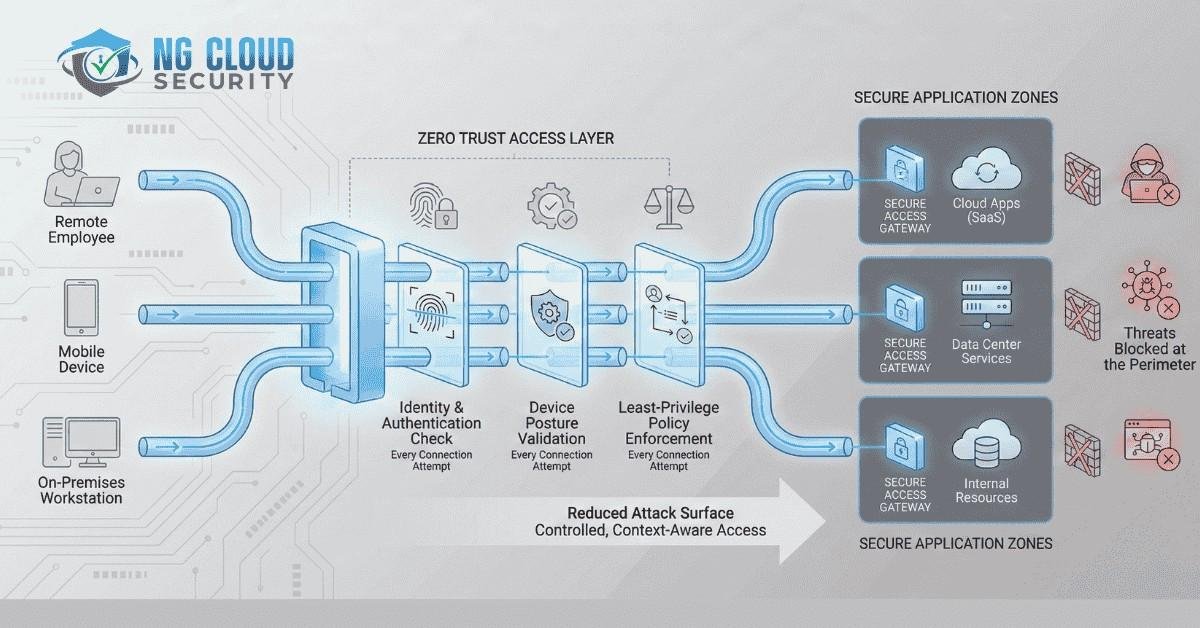
How Zero Trust Network Access Works in Enterprises
Now let us look at how ZTNA works in practice.
When a user attempts to access an enterprise application, the following sequence typically occurs:
- User authentication through identity provider
- Multi factor authentication verification
- Device compliance validation
- Contextual risk analysis
- Policy enforcement
- Application specific access granted
The user never directly connects to the internal network. Instead, a secure broker connects the user to the specific application.
This significantly reduces the attack surface.
If you want a simplified explanation for business leaders, this guide may help:
https://ngcloudsecurity.com/how-does-zero-trust-work-a-simple-breakdown-for-business-owners/
Key Components of a ZTNA Architecture
A strong Zero Trust Network Access deployment includes several integrated components.
Identity and Access Management
Identity platforms validate users and enforce access policies. Conditional access policies are critical for risk based decision making.
Device Security and Endpoint Protection
Endpoints must be secure and compliant before access is granted. This includes endpoint detection, threat monitoring, and configuration management.
You can explore endpoint related risks here:
https://ngcloudsecurity.com/top-endpoint-security-threats/
For organizations looking to assess their endpoint readiness:
https://ngcloudsecurity.com/endpoint-security-assessment/
Secure Access Broker
This component acts as the intermediary between users and applications. It ensures users never directly expose internal services.
Continuous Monitoring and SOC Integration
Security operations teams monitor access patterns and respond to anomalies in real time. Managed SOC services often integrate deeply with Zero Trust architecture.
Business Benefits of Zero Trust Network Access
From my experience advising enterprise leadership teams, the value of ZTNA extends beyond security.
Reduced Attack Surface
By eliminating broad network level access, organizations drastically reduce lateral movement risks.
Improved Compliance Alignment
ZTNA supports regulatory requirements by enforcing strict access controls and audit trails.
Better Support for Hybrid Work
Employees can securely access applications from anywhere without exposing internal networks.
Faster Cloud Adoption
As enterprises adopt multi cloud and SaaS platforms, Zero Trust becomes essential. You can explore cloud security best practices here:
https://ngcloudsecurity.com/best-practices-for-cloud-security-protect-your-data/
Operational Efficiency
Security teams spend less time managing complex VPN configurations and more time focusing on risk reduction.
ZTNA and Cloud Transformation
Cloud adoption changes everything about network design.
In traditional data center environments, security was perimeter focused. In cloud environments, applications are distributed across providers, regions, and services.
ZTNA fits naturally into this architecture.
It provides:
- Application level segmentation
- Identity centric policy enforcement
- Integration with cloud native security controls
- Consistent access across hybrid environments
If your organization is planning cloud transformation, consider aligning access strategy early. Our Cloud Security Assessment services can help evaluate.
Common Challenges in ZTNA Implementation
While Zero Trust Network Access offers strong advantages, implementation requires careful planning.
Legacy Applications
Some older applications are not designed for modern authentication standards.
Identity Gaps
Organizations without strong identity governance struggle to implement effective policy enforcement.
Cultural Resistance
Teams accustomed to VPN based models may initially resist change.
Visibility Limitations
Without centralized monitoring, policy enforcement can become fragmented.
In enterprise programs, I always recommend starting with a structured assessment phase before deploying ZTNA widely.
Zero Trust Network Access and Zero Trust Strategy
ZTNA is a major pillar of Zero Trust, but it is not the entire framework.
Zero Trust also includes:
- Data protection
- Endpoint security
- Email security
- Threat intelligence
- Identity governance
- Continuous monitoring
If you want a deeper look at Zero Trust in cybersecurity strategy, this resource is helpful:
https://ngcloudsecurity.com/what-does-zero-trust-mean-in-cyber-security-strategy/
ZTNA Use Cases in Enterprise Environments
Zero Trust Network Access is particularly valuable in the following scenarios:
Remote Workforce Enablement
Secure access without exposing full networks.
Third Party Vendor Access
Granular control for contractors and partners.
Multi Cloud Application Access
Unified access policies across different cloud providers.
Mergers and Acquisitions
Temporary and segmented access during integration phases.
High Risk Environments
Financial services, healthcare, government, and regulated industries.
Measuring the Success of ZTNA
Enterprises should track measurable outcomes such as:
- Reduction in lateral movement incidents
- Decrease in credential based breaches
- Improved audit outcomes
- Faster onboarding and offboarding
- Reduced VPN dependency
Security should support business growth. A well designed ZTNA architecture enables innovation while maintaining strong governance.
Final Thoughts on What Is Zero Trust Network Access
So, what is zero trust network access in practical terms?
It is a modern security framework that replaces outdated perimeter based trust with identity driven, application specific, continuously validated access control.
For enterprises navigating digital transformation, cloud migration, and evolving compliance requirements, ZTNA is not optional. It is foundational.
In my experience, organizations that adopt Zero Trust early are more resilient, more agile, and better prepared for emerging threats.
If you are evaluating how Zero Trust Network Access fits into your enterprise strategy, start with an assessment, define clear objectives, align identity and endpoint readiness, and implement in phased stages.
Most importantly, treat Zero Trust as a business strategy, not just a technical project.
When executed correctly, Zero Trust Network Access becomes a competitive advantage, enabling secure growth in a rapidly changing digital world.