Advantages and Disadvantages of Intrusion Detection System
Cyber threats are becoming more advanced every year, and organizations must continuously monitor their networks to detect suspicious activity before it turns into a serious security incident. One of the most widely used technologies for this purpose is an intrusion detection system.
An intrusion detection system helps organizations monitor network traffic, detect unusual behavior, and alert security teams when potential threats appear. In modern cybersecurity environments, IDS tools play a critical role in identifying attacks early and improving overall security visibility.
However, like any security technology, it is important to understand both the advantages and disadvantages of intrusion detection system solutions before implementing them in an organization.
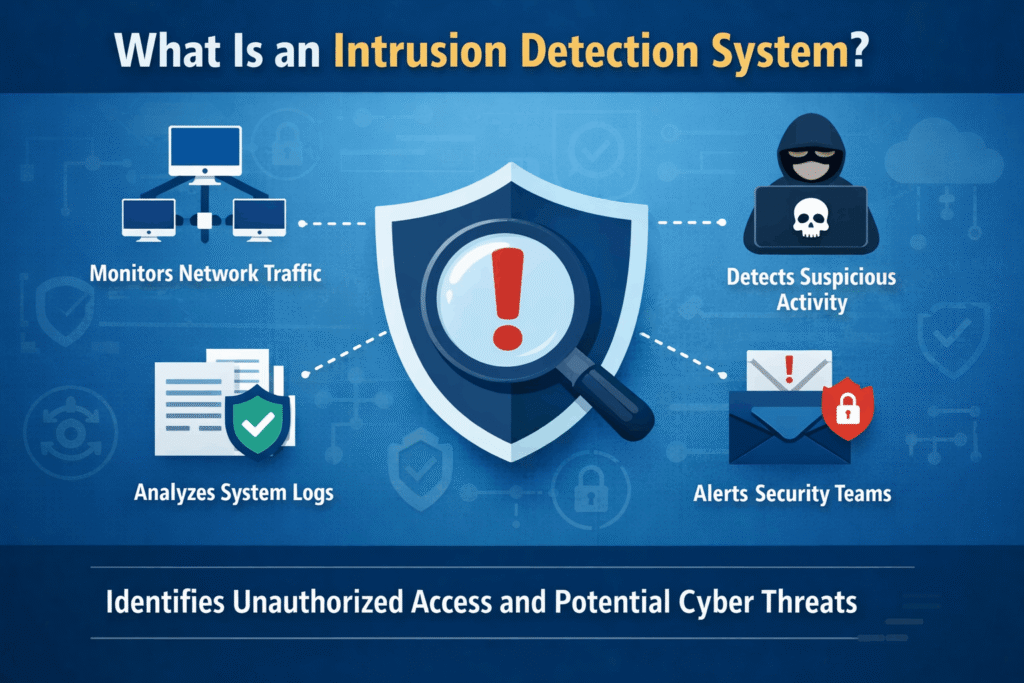
What Is an Intrusion Detection System
An intrusion detection system, commonly known as IDS, is a cybersecurity tool that monitors network traffic or system activity to identify suspicious behavior, security policy violations, or potential cyber attacks.
IDS analyzes network packets, system logs, and user activities to detect abnormal patterns that may indicate malicious behavior such as unauthorized access attempts, malware activity, or data exfiltration.
Many organizations deploy IDS together with other cybersecurity technologies such as endpoint protection tools. For example, companies often combine IDS monitoring with advanced endpoint protection platforms. If you want to understand how endpoint protection works in modern environments, you can learn more about different types of endpoint protection solutions.
Types of Intrusion Detection Systems
Intrusion detection systems are typically categorized based on how and where they monitor activity.
Network Based Intrusion Detection System
A network based intrusion detection system monitors network traffic across an entire infrastructure. It analyzes packets moving through the network to detect suspicious patterns that could indicate cyber attacks.
Network IDS solutions are effective for identifying activities such as malware communication, suspicious connections, and reconnaissance attempts. For instance, attackers often scan networks to discover open ports before launching an attack. Understanding how attackers use port scanning to find vulnerabilities helps security teams recognize early warning signs of a potential intrusion.
Host Based Intrusion Detection System
A host based intrusion detection system runs directly on individual devices such as servers or endpoints. It monitors system logs, file integrity, and user activity to detect unauthorized modifications or suspicious actions.
Host based IDS solutions are particularly useful for identifying insider threats or compromised user accounts within an organization.
Signature Based Intrusion Detection
Signature based IDS detects threats by comparing network activity with a database of known attack signatures. When activity matches a known attack pattern, the system generates an alert.
This method is highly effective for detecting known threats but may struggle to identify new attack techniques.
Anomaly Based Intrusion Detection
An anomaly based IDS focuses on detecting unusual behavior. It first establishes a baseline of normal network activity and then identifies deviations from that baseline.
This approach helps detect previously unknown threats, although it may sometimes produce more alerts than signature based detection.
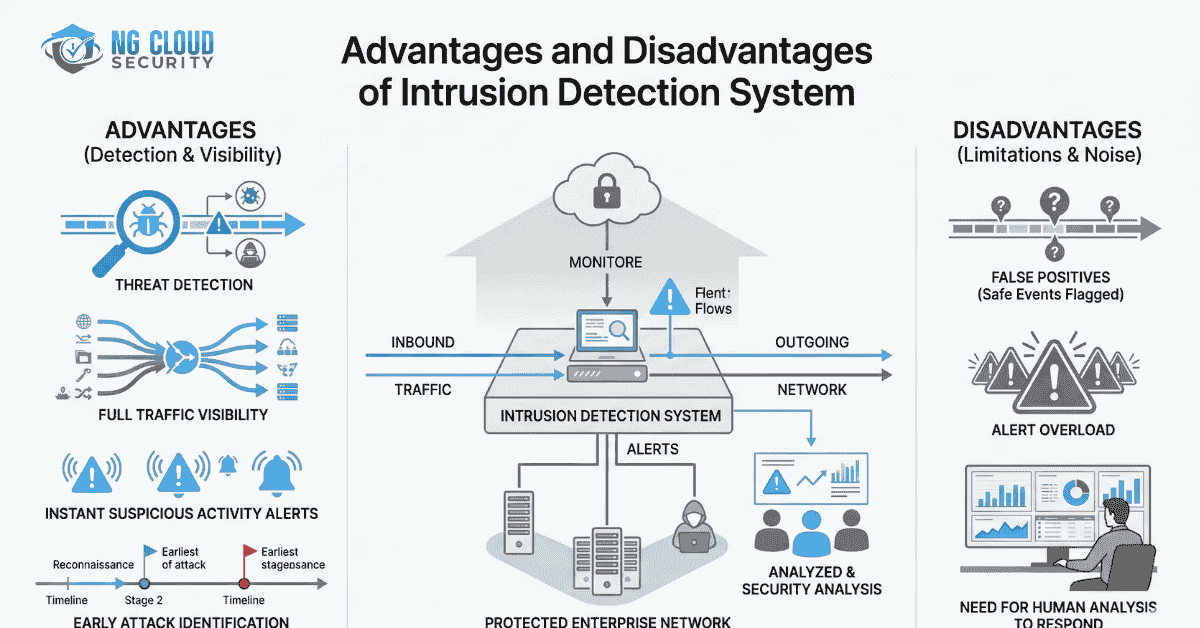
Advantages of Intrusion Detection System
Intrusion detection systems provide several benefits that improve an organization’s ability to detect and respond to cyber threats.
Early Threat Detection
One of the biggest advantages of intrusion detection system technology is early detection of potential attacks.
IDS continuously monitors network activity and identifies suspicious behavior before attackers can fully compromise systems.
In many real world scenarios, early alerts from IDS platforms allow security teams to respond quickly and prevent serious damage.
Improved Network Visibility
IDS provides detailed visibility into network traffic and system activity. Security teams gain insights into how users interact with systems and where potential vulnerabilities may exist.
This visibility is especially important for organizations adopting modern cybersecurity models such as Zero Trust architecture. If you want to understand this security approach better, you can explore what zero trust network access means for enterprise security.
Faster Incident Response
IDS alerts enable security teams to investigate suspicious activity immediately.
Instead of discovering a breach weeks later, organizations can respond quickly to suspicious activity and reduce the impact of security incidents.
Compliance and Security Monitoring
Many regulatory frameworks require organizations to monitor network activity and detect unauthorized access attempts.
Deploying IDS helps organizations maintain security logs and monitoring capabilities that support compliance requirements.
Detection of Insider Threats
Not all cyber attacks come from external attackers. Some security incidents originate from compromised accounts or malicious insiders.
Host based IDS tools can detect unusual file changes, privilege escalation attempts, or suspicious internal activity.
Organizations often combine IDS monitoring with endpoint detection tools. Understanding the difference between EDR and traditional antivirus protection can help businesses strengthen their security architecture.
Disadvantages of Intrusion Detection System
Despite its advantages, intrusion detection systems also have certain limitations.
High Number of False Alerts
IDS solutions sometimes generate alerts for normal network activity. These false alerts can overwhelm security teams and create alert fatigue.
Proper configuration and tuning are required to reduce the number of false positives.
False Negatives
While IDS detects many threats, it may occasionally fail to identify certain attacks. This situation is known as a false negative.
False negatives may occur when detection signatures are outdated or when attackers use advanced techniques that bypass traditional detection rules.
Difficulty Inspecting Encrypted Traffic
Modern networks rely heavily on encryption to protect data.
Because encrypted packets cannot always be inspected, intrusion detection systems may have difficulty analyzing the contents of encrypted traffic. Attackers sometimes exploit encrypted channels to hide malicious activity.
Requires Skilled Security Professionals
IDS generates alerts but does not automatically resolve security incidents.
Security professionals must analyze alerts, investigate suspicious events, and take appropriate actions to mitigate threats.
Continuous Updates Required
Intrusion detection systems rely on updated detection signatures and threat intelligence.
Without regular updates, IDS tools may fail to detect new attack techniques. Security teams must continuously update detection libraries to maintain effectiveness.
In cloud environments such as Microsoft Azure, IDS is often combined with other security practices. Organizations should also follow best practices organizations use to strengthen cloud security to protect modern infrastructure.
Intrusion Detection System vs Intrusion Prevention System
Intrusion detection systems are often confused with intrusion prevention systems.
An intrusion detection system focuses on monitoring network activity and alerting security teams when suspicious behavior is detected.
An intrusion prevention system goes one step further by automatically blocking malicious traffic or suspicious connections.
In many organizations, both technologies are deployed together to provide a layered security approach that detects and prevents attacks more effectively.
Final Thoughts
Understanding the advantages and disadvantages of intrusion detection system technology is essential for building a strong cybersecurity strategy.
IDS provides valuable benefits such as early threat detection, improved network visibility, and faster incident response. However, organizations must also consider limitations such as false alerts, encrypted traffic challenges, and the need for skilled security professionals.
When combined with modern security frameworks, endpoint protection, and cloud security practices, intrusion detection systems become a powerful tool for protecting enterprise networks from evolving cyber threats.