Difference Between NIDS and HIDS Explained with Examples
Cybersecurity threats continue to evolve as organizations expand their digital infrastructure. Modern environments now include cloud platforms, remote work systems, SaaS applications, and connected devices. Because of this growing complexity, monitoring suspicious activity across systems and networks has become a critical part of security operations.
Intrusion detection technologies help security teams detect malicious activities before attackers cause significant damage. Two important detection technologies used in enterprise environments are Network Intrusion Detection Systems and Host Intrusion Detection Systems.
Many security professionals search for the difference between NIDS and HIDS because both solutions monitor cyber threats but operate at different layers of the infrastructure. From my experience working with enterprise security environments, organizations gain better protection when they clearly understand how each detection system works and where it should be implemented.
This guide explains the difference between NIDS and HIDS, how they work, and when organizations should use each approach.
What Is an Intrusion Detection System
An Intrusion Detection System monitors system activity or network traffic to identify suspicious behavior, malicious patterns, or security policy violations. Instead of blocking attacks directly, the primary purpose of an intrusion detection system is to analyze activity and alert security teams when something abnormal occurs.
These systems analyze data using two common techniques. Signature based detection compares activity against known attack patterns stored in a database. Behavior based detection identifies unusual activity that deviates from normal system behavior.
Organizations often deploy intrusion detection solutions alongside other security strategies such as Zero Trust network access and layered monitoring systems to improve overall visibility.
What Is a Network Intrusion Detection System
A Network Intrusion Detection System monitors traffic flowing across an organization’s network infrastructure. It inspects packets moving between systems and identifies suspicious communication patterns that may indicate an attack.
NIDS solutions are typically deployed at important network points such as gateways, routers, switches, or network segmentation zones. These locations allow the system to analyze traffic from multiple devices simultaneously.
The primary objective of NIDS is to detect network level attacks such as scanning attempts, abnormal traffic spikes, or suspicious communication with external servers.
Organizations that implement strong network monitoring often combine NIDS with centralized monitoring platforms such as security information and event management solutions to correlate alerts across multiple systems.
Example of NIDS in Action
Consider a scenario where an attacker attempts to scan an organization’s network to identify vulnerable services. The attacker sends connection requests to hundreds of ports across several servers.
A network intrusion detection system observes this unusual traffic pattern and identifies it as a port scanning activity. Since the behavior matches a known reconnaissance pattern, the system generates an alert for the security operations team.
Security teams can then investigate the activity and block the malicious source before the attacker discovers vulnerable systems. Organizations that want to understand this attack method in detail can also review how port scanning works in cyber security.
What Is a Host Intrusion Detection System
A Host Intrusion Detection System focuses on monitoring activities inside a specific device such as a server, workstation, or endpoint.
Instead of analyzing network traffic, HIDS monitors internal system activity. This includes file integrity monitoring, application behavior, system logs, configuration changes, and user actions.
From my experience advising organizations on security architecture, HIDS plays a crucial role in detecting attacks that occur after an attacker has gained access to a device.
Many organizations deploy host level monitoring as part of broader endpoint protection strategies such as endpoint security solutions.
Example of HIDS in Action
Imagine a situation where an attacker exploits a vulnerability in a web application and gains access to a server. After gaining access, the attacker attempts to modify system configuration files and install malicious software.
A host intrusion detection system identifies that protected files have been altered. The system immediately logs the activity and generates an alert.
This allows the security team to isolate the system, investigate the compromise, and prevent further damage.
Key Difference Between NIDS and HIDS
The primary difference between NIDS and HIDS lies in where the monitoring takes place.
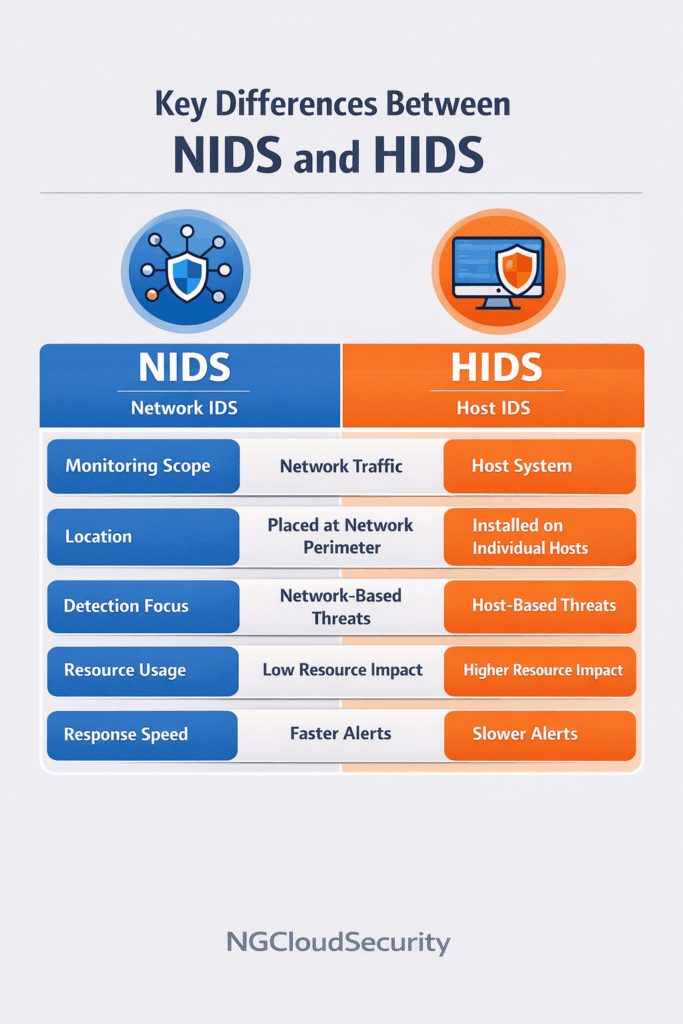
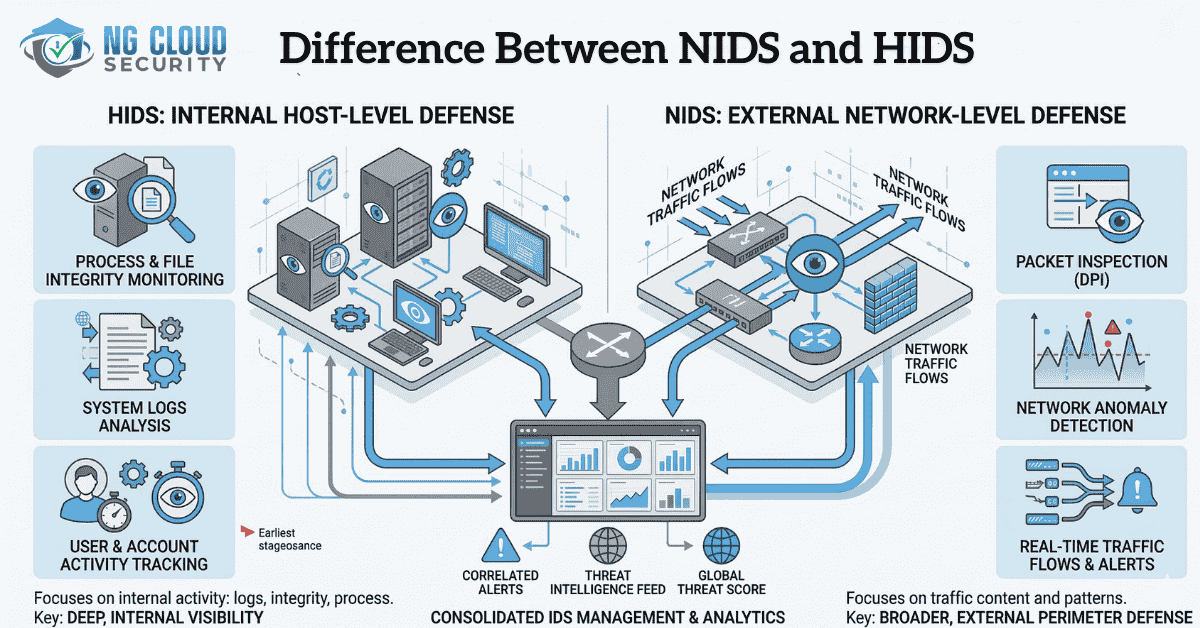
Network intrusion detection systems monitor communication across the network infrastructure. Host intrusion detection systems monitor activities inside individual systems.
NIDS focuses on analyzing network traffic patterns between devices. HIDS focuses on detecting suspicious actions occurring within the operating system or applications.
Both technologies provide different layers of visibility into potential cyber threats.
Comparison Between NIDS and HIDS
Monitoring Scope
NIDS monitors traffic across entire network segments and can observe communication between multiple systems.
HIDS monitors activity inside a specific device and analyzes logs, processes, and file changes.
Deployment Location
NIDS is deployed at network checkpoints such as routers, switches, or network gateways.
HIDS is installed directly on servers, workstations, and endpoints.
Threat Detection Capabilities
Network intrusion detection systems are effective at detecting network based attacks such as scanning attempts, suspicious traffic patterns, or denial of service activities.
Host intrusion detection systems are better at identifying unauthorized file modifications, malware execution, privilege escalation attempts, and insider threats.
Deployment Complexity
NIDS requires fewer deployment points because it monitors network traffic centrally.
HIDS must be installed on every device that requires monitoring, which can increase deployment effort in large environments.
Advantages of Network Intrusion Detection Systems
Network intrusion detection systems provide broad visibility across the entire network environment. They can detect attacks targeting multiple systems simultaneously and identify early stage reconnaissance activities.
Another advantage is that they do not consume resources on individual hosts because the monitoring occurs at the network level.
Advantages of Host Intrusion Detection Systems
Host intrusion detection systems provide deeper visibility into system level activities. They are capable of detecting file integrity changes, unauthorized configuration updates, and suspicious processes running on a system.
These solutions are particularly valuable for protecting critical workloads such as application servers, database servers, and cloud workloads.
Organizations that deploy HIDS as part of broader security monitoring strategies often integrate them with centralized security operations platforms such as managed SOC services to improve incident response.
Why Modern Security Architectures Use Both
Relying on only one intrusion detection method can leave security gaps. Network monitoring alone cannot detect malicious actions occurring inside a device. Host monitoring alone cannot identify large scale network reconnaissance activities.
For this reason, modern cybersecurity strategies combine both technologies as part of a layered defense model.
When NIDS and HIDS work together, organizations gain visibility across both network communication and system behavior. This approach allows security teams to detect attacks at multiple stages and respond faster to potential incidents.
Conclusion
Understanding the difference between NIDS and HIDS is essential for designing a strong cybersecurity monitoring strategy. Network intrusion detection systems analyze traffic across the network to identify suspicious communication patterns. Host intrusion detection systems monitor activity inside individual devices to detect unauthorized changes or malicious behavior.
Both technologies address different parts of the attack lifecycle. From my experience working with enterprise security environments, organizations that combine network level monitoring with host level detection achieve better threat visibility and stronger protection against modern cyber attacks.