What Is Port Scanning in Cyber Security and How Hackers Use It
If you are searching for what is port scanning in cyber security, you are already thinking like a security leader. Port scanning is one of the most common reconnaissance techniques used in modern cyber attacks. It is often the first step attackers take before attempting to exploit a system.
From my experience working with organizations that invest in a strong Zero Trust security strategy, early detection of scanning activity can prevent major breaches.
What Is Port Scanning in Cyber Security
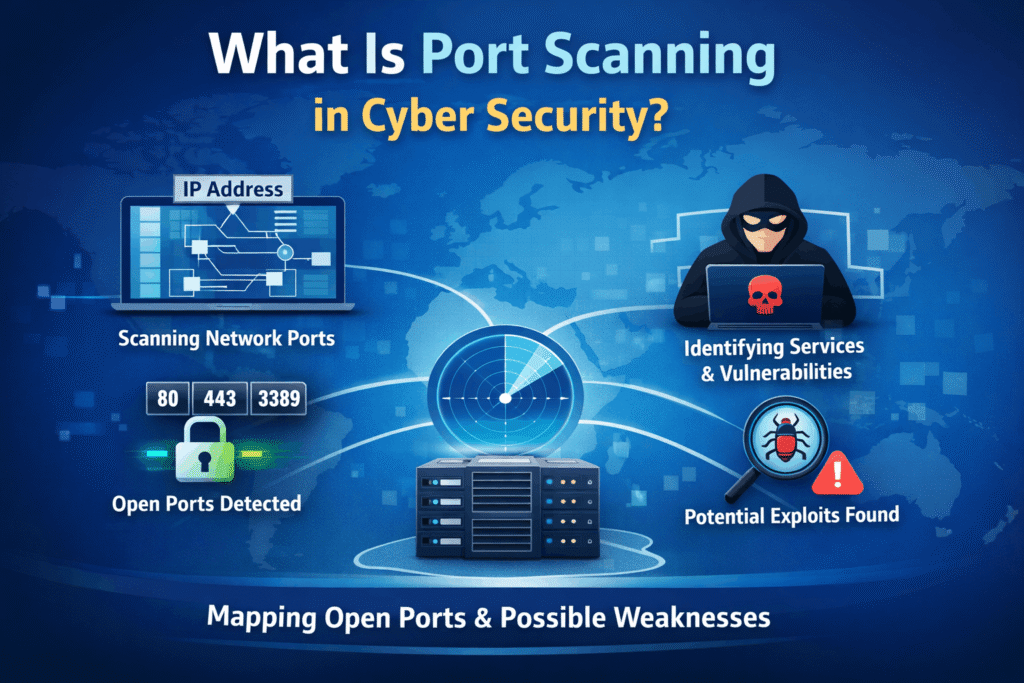
Port scanning in cyber security is the process of sending requests to multiple network ports on a server or device to determine which ports are open and listening.
Each device connected to a network uses ports to communicate. Services like web servers, email systems, remote access tools, and databases operate on specific port numbers. When a hacker scans ports, they are essentially checking which doors are open.
Understanding what port scanning is in cyber security helps organizations reduce unnecessary exposure and protect critical infrastructure.
If your organization runs public facing workloads in Azure or hybrid environments, regular assessments like a cloud security assessment can help identify exposed ports before attackers do.
Why Port Scanning Is a Serious Security Risk
Port scanning itself is not illegal. Security teams use it for legitimate testing. However, attackers use it as part of reconnaissance.
Once open ports are discovered, attackers can:
- Identify running services
- Detect outdated applications
- Discover exposed remote desktop services
- Find weak firewall configurations
- Target known vulnerabilities
For example, exposed remote access without proper controls can create a direct attack path. That is why businesses investing in endpoint security solutions and secure remote configurations significantly reduce risk.
Organizations that ignore scanning activity often experience larger incidents later, including ransomware and data breaches.
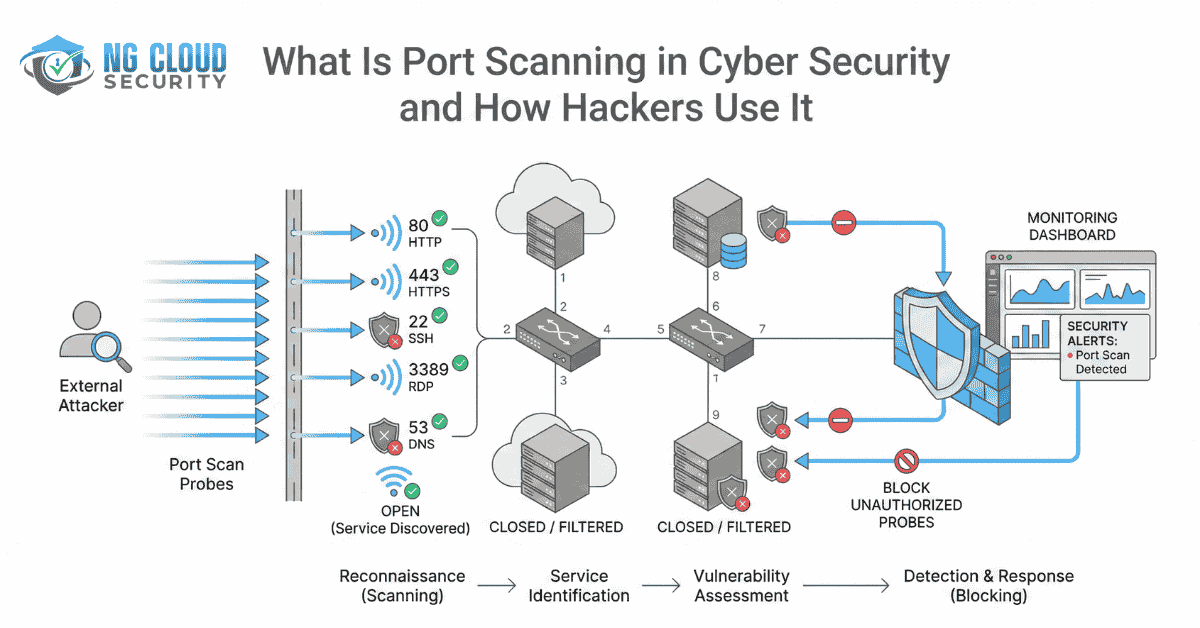
How Hackers Use Port Scanning
Attackers use port scanning methodically. It is not random.
Target Identification
The attacker selects a domain or IP address. This may belong to a company website, application server, or cloud workload.
Port Discovery
Automated tools scan thousands of ports in seconds to identify which ones respond.
Service Identification
Once open ports are detected, attackers determine what services are running. It may reveal web servers, file transfer services, databases, or mail servers.
For example, if email related ports are exposed, attackers may attempt phishing or spoofing attacks. This is why strong email security controls are critical.
Vulnerability Mapping
Attackers compare discovered services against known vulnerabilities.
Exploitation
If a weakness exists, they attempt unauthorized access or privilege escalation.
In many cases, port scanning logs are the earliest warning sign that your environment is being tested. A proactive security assessment and control review can help detect such behavior early.
Common Types of Port Scanning Techniques
To fully understand what is port scanning in cyber security, you should know the common scanning methods.
TCP Connect Scan
This method completes the full connection. It is easy to detect but very effective.
SYN Scan
This technique performs a half open connection. It is faster and more stealthy.
UDP Scan
Often overlooked, UDP scanning targets services such as DNS.
Stealth Scan
Designed to bypass basic detection systems.
Advanced attackers combine multiple techniques to create a complete map of your infrastructure.
Organizations with mature monitoring, such as SOC managed services, can identify suspicious scanning behavior before exploitation occurs.
Risks of Open Ports in Cloud and Hybrid Environments
In modern cloud environments, misconfigured security groups and firewall rules can unintentionally expose ports to the internet.
If you are operating workloads in Azure, strong perimeter protection such as Azure Firewall and structured deployment models like Azure Landing Zone help reduce attack surface.
Open ports become dangerous when:
- Services are outdated
- Multi factor authentication is missing
- Network segmentation is weak
- Monitoring is not enabled
- Remote access is publicly exposed
A single exposed port can lead to data theft, ransomware, compliance violations, and operational downtime.
How to Protect Against Malicious Port Scanning
Here are practical steps to reduce risk.
Close Unnecessary Ports
Disable services that are not required. Minimize your attack surface.
Implement Zero Trust Access
Adopt principles from Zero Trust security services to verify every connection request.
Use Network Monitoring
Continuous monitoring detects repeated connection attempts across multiple ports.
Strengthen Endpoint Protection
Modern endpoint security assessment helps identify vulnerabilities before attackers do.
Conduct Regular Cloud Reviews
Periodic reviews under cloud security services ensure firewall rules and configurations remain secure.
From my experience, organizations that combine strong architecture with continuous monitoring and follow the NIST Cybersecurity Framework guidelines rarely experience successful exploitation after a scan.
Final Thoughts
Understanding what port scanning is in cyber security is essential for protecting modern IT environments. It is one of the oldest yet most effective reconnaissance methods used by attackers.
Port scanning reveals open doors. Your job is to make sure those doors are locked, monitored, and accessible only to authorized users.
Cyber security is not about reacting after an attack. It is about reducing exposure before exploitation happens. With the right strategy, architecture, and monitoring, you can turn early scanning attempts into early warning signals rather than breach headlines.