What Are the Three Principles of Zero Trust Architecture Explained
Zero Trust is no longer just a cybersecurity buzzword. It has become a strategic approach that organizations rely on to secure modern environments driven by cloud, remote work, and evolving cyber threats. If you are searching for what are the three principles of zero trust, the answer goes beyond theory. These principles define how modern security actually works in real business environments.
From my experience working with organizations adopting cloud and hybrid infrastructure, the biggest gap in traditional security is simple. It assumes that users inside the network can be trusted. Attackers today exploit this exact weakness.
Zero Trust removes this assumption completely and replaces it with continuous verification and control.
What Is Zero Trust Architecture
Zero Trust Architecture is a security model built on the idea that no user or system should be trusted by default. Every access request must be verified, regardless of where it comes from.
Unlike traditional perimeter based security, Zero Trust focuses on identity, access, and visibility across the entire environment. This approach is also aligned with globally recognized frameworks like the Zero Trust security model definition.
If you want a deeper understanding of how this model works in real scenarios, you can explore this detailed guide on how Zero Trust works in real business environments.
It is important to understand that Zero Trust is not a product. It is a framework that combines identity management, endpoint security, network control, and continuous monitoring.
What Are the Three Principles of Zero Trust
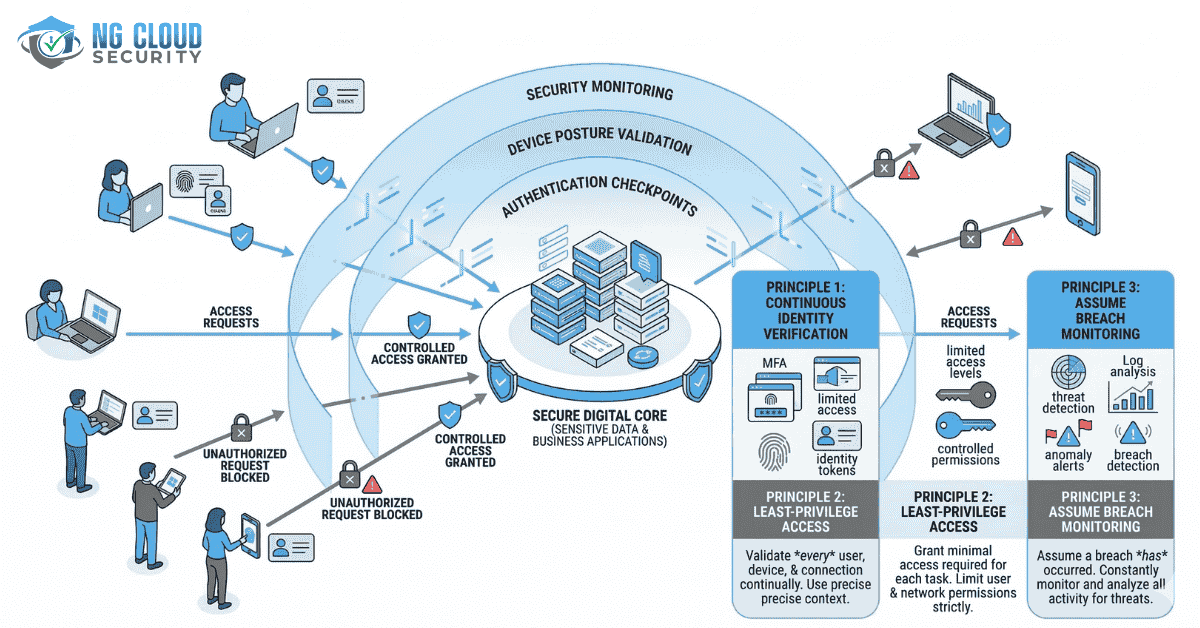
To clearly answer what are the three principles of zero trust, you need to understand these three core foundations that drive the entire architecture.
1. Verify Explicitly
The first principle is to verify every access request without exception. Every user, device, and application must be authenticated and authorized before accessing any resource.
This includes multiple factors such as identity, device health, location, and behavioral signals. Access decisions are made dynamically based on risk, which is also part of a identity based security approach followed by modern enterprises.
In real environments, this means trust is never permanent. Even after login, systems continuously evaluate user activity. If risk increases, access can be restricted instantly.
This is why modern identity systems play a critical role. You can explore how identity strengthens security in this guide on Azure Active Directory security capabilities.
2. Use Least Privilege Access
The second principle focuses on limiting access strictly to what is required. Users and systems should only have permissions necessary to perform their tasks.
This reduces the attack surface and prevents unnecessary exposure of sensitive systems. In many organizations, excessive permissions create hidden risks.
Least privilege access ensures that access is controlled, time based, and monitored. Administrative access is restricted, and high risk actions are tracked closely.
If you want to understand how access control improves security posture, this guide on benefits of Identity and Access Management explains it in detail.
From what I have seen, organizations that implement least privilege correctly significantly reduce both insider threats and damage from compromised accounts.
3. Assume Breach
The third principle is to always assume that a breach can happen. Instead of relying only on prevention, Zero Trust focuses on detection, response, and containment.
This principle changes how networks are designed. Systems are segmented so that attackers cannot move freely across environments. Even if one area is compromised, the impact remains limited.
This aligns with guidance from modern frameworks like the cybersecurity framework that emphasizes containment and resilience.
Continuous monitoring and threat detection tools help identify suspicious activity in real time. This ensures faster response and reduced damage.
To understand how modern detection and response systems support this approach, you can refer to this guide on extended detection and response solutions.
In my experience, this principle builds true resilience because organizations are prepared for real world attack scenarios.
Why These Three Principles Matter
Understanding what are the three principles of zero trust is important because they directly address today’s cybersecurity challenges.
Organizations now operate in distributed environments with cloud applications, remote users, and third party integrations. Traditional security models cannot handle this complexity.
These principles create a system where access is controlled, trust is eliminated, and threats are identified early.
They also align with modern compliance requirements and security frameworks.
How Zero Trust Works in Real Environments
Zero Trust is implemented through a combination of technologies and processes working together.
Identity systems verify users. Endpoint tools validate devices. Network controls restrict communication. Monitoring platforms provide visibility into activity.
If you are planning to adopt this model, working with experts offering Zero Trust security services can help ensure proper implementation without disrupting business operations.
A phased approach works best. Start with identity and access control, then expand to network segmentation and continuous monitoring.
Business Benefits of Zero Trust
Organizations adopting Zero Trust gain more than just improved security.
They achieve better visibility across systems, stronger control over access, and faster response to threats. Compliance becomes easier because policies are enforced consistently.
Zero Trust also supports business growth by enabling secure remote access and cloud adoption.
From what I have seen, it gives leadership confidence that security is aligned with business goals.
Common Challenges and Practical Approach
Implementing Zero Trust can feel complex, especially for organizations with legacy systems.
The key is to avoid trying to do everything at once. Start with critical assets and high risk areas. Use automation to simplify processes and reduce manual effort.
Balancing security with user experience is also important. Smart authentication methods help maintain both security and productivity.
Zero Trust is not a one time project. It is an evolving strategy that improves over time.
Final Thoughts
If you are still asking what are the three principles of zero trust, remember these three core ideas. Verify every request, limit access strictly, and always assume breach.
These principles redefine how organizations approach cybersecurity in a world where threats are constantly evolving.
From my experience, businesses that adopt Zero Trust build a stronger, more resilient, and future ready security framework that supports both protection and growth.