Types of Endpoint Security Explained: From Traditional Antivirus to XDR
Endpoint security has evolved rapidly over the past decade. As organizations move to cloud platforms, remote work models, and mobile devices, protecting endpoints has become a core pillar of modern cybersecurity. If you are new to this topic, you can also read our detailed guide on what is endpoint security and how it works.
Understanding the different types of endpoint security helps businesses build stronger defense strategies that align with operational growth and risk management goals.
What Is Endpoint Security
Endpoint security refers to protecting devices such as laptops, desktops, servers, and mobile devices that connect to corporate environments. These devices are common entry points for ransomware, phishing, and credential based attacks.
To better understand the risk landscape, explore our article on top endpoint security threats.
Modern endpoint protection is not just about installing software. It is about building layered protection supported by monitoring, response, and compliance controls.
1. Traditional Antivirus
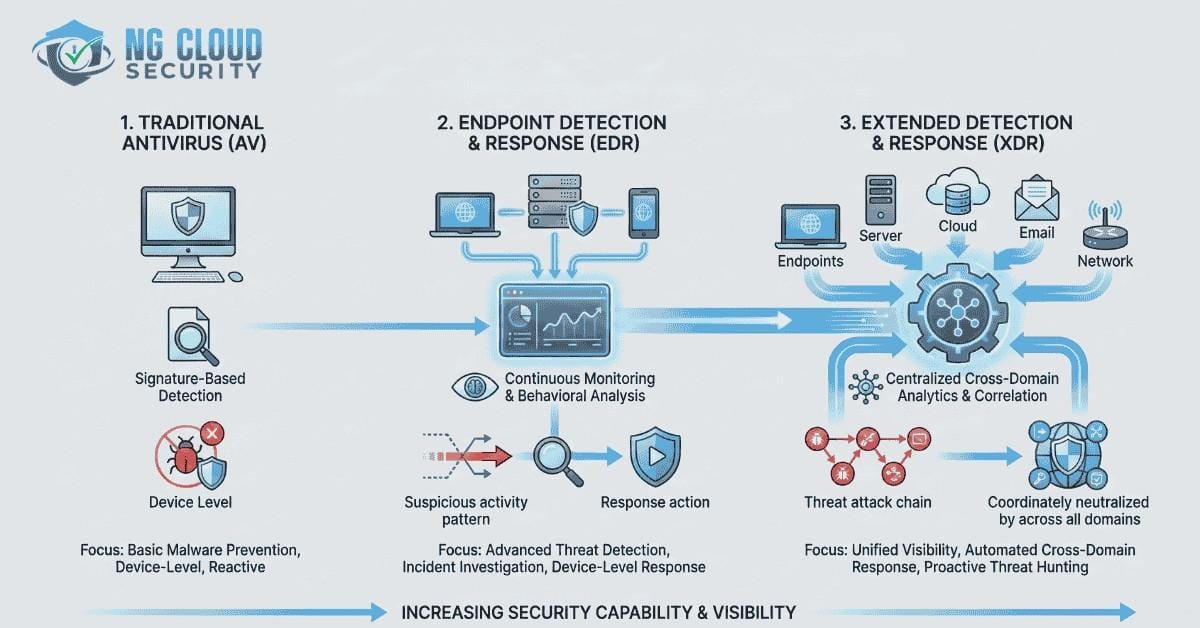
Traditional antivirus is the foundation of endpoint protection. It primarily uses signature based detection to identify known malware.
How It Works
Antivirus scans files and compares them to a database of known malicious signatures. When a match is detected, the file is quarantined or removed.
Limitations
While antivirus remains useful, it struggles against advanced threats and zero day exploits. That is why many organizations compare solutions like EDR and antivirus to understand which offers better protection.
Antivirus alone is no longer sufficient for modern environments.
2. Next Generation Antivirus
Next Generation Antivirus builds on traditional antivirus by adding behavioral detection and machine learning capabilities.
Instead of relying only on signatures, it analyzes patterns such as suspicious process execution, abnormal privilege usage, and unusual network communication.
This type of solution improves protection against emerging threats while maintaining system performance.
3. Endpoint Detection and Response
Endpoint Detection and Response focuses on continuous monitoring, investigation, and response.
Key Capabilities
- Real time monitoring
- Threat hunting
- Incident investigation
- Automated containment
EDR solutions provide detailed visibility into endpoint telemetry. Organizations that want to strengthen proactive detection often combine EDR with structured security operations such as SOC managed services.
For businesses seeking advanced endpoint governance, an endpoint security assessment can identify gaps in visibility and response readiness.
4. Extended Detection and Response
Extended Detection and Response expands beyond endpoints. It correlates signals across identity, cloud, email, and network layers.
Unlike standalone EDR tools, XDR provides centralized analytics and automated response across environments. You can explore more about this approach in our article on Microsoft Defender for XDR.
XDR is particularly valuable for organizations adopting Zero Trust strategies. If you are building such a framework, read our insights on Zero Trust security mindset.
5. Mobile Endpoint Security
With hybrid work models, mobile devices are part of the enterprise attack surface.
Mobile endpoint security protects smartphones and tablets through application control, device encryption enforcement, and mobile threat defense.
Mobile security works best when aligned with broader endpoint and identity controls.
6. Endpoint Privilege Management
Many endpoint breaches happen because users have excessive privileges. Privilege management reduces risk by enforcing least privilege principles.
By removing unnecessary administrative access and monitoring elevated activity, organizations reduce their attack surface significantly.
Identity centric security controls such as modern identity and access management play a critical role in strengthening endpoint protection.
7. Unified Endpoint Management
Unified Endpoint Management ensures consistent policy enforcement, compliance monitoring, and device lifecycle management.
It supports patch management, encryption enforcement, and configuration control. When combined with broader endpoint security services, UEM enables organizations to maintain security hygiene at scale.
How to Choose the Right Types of Endpoint Security
Selecting the right types of endpoint security depends on your organization size, compliance needs, and operational maturity.
Small businesses may begin with Next Generation Antivirus and basic monitoring. Mid sized organizations benefit from EDR supported by structured response processes. Enterprises with distributed environments typically require XDR combined with cloud integrated security.
Endpoint security must align with broader cloud security strategy and identity protection initiatives.
Final Thoughts
Endpoint security has evolved from simple antivirus software to intelligent, integrated platforms capable of detecting and responding to complex threats.
Understanding the different types of endpoint security helps organizations move beyond reactive defense and build proactive resilience. A layered approach that combines prevention, detection, response, and governance is essential for long term protection.
If you are evaluating your current posture, consider conducting a structured assessment and aligning your endpoint controls with Zero Trust principles and modern cloud security frameworks.